
Risk actors are exploiting 3 just lately disclosed Home windows safety vulnerabilities in assaults geared toward gaining SYSTEM or increased administrator permissions.
For the reason that get started of the month, a safety researcher referred to as “Chaotic Eclipse” or “Nightmare-Eclipse” has revealed proof-of-concept exploit code for all 3 safety problems in protest to how Microsoft’s Safety Reaction Heart (MSRC) treated the disclosure procedure.
Two of the vulnerabilities (dubbed BlueHammer and RedSun) are Microsoft Defender native privilege escalation (LPE) flaws, whilst the 3rd (referred to as UnDefend) can also be exploited as a regular consumer to dam Microsoft Defender definition updates.

On the time of the leak, the protection flaws those exploits centered have been regarded as zero-days by means of Microsoft’s definition, since they’d no professional patches or updates to deal with them.
On Thursday, Huntress Labs safety researchers reported seeing all 3 zero-day exploits deployed within the wild, with the BlueHammer vulnerability being exploited since April 10.
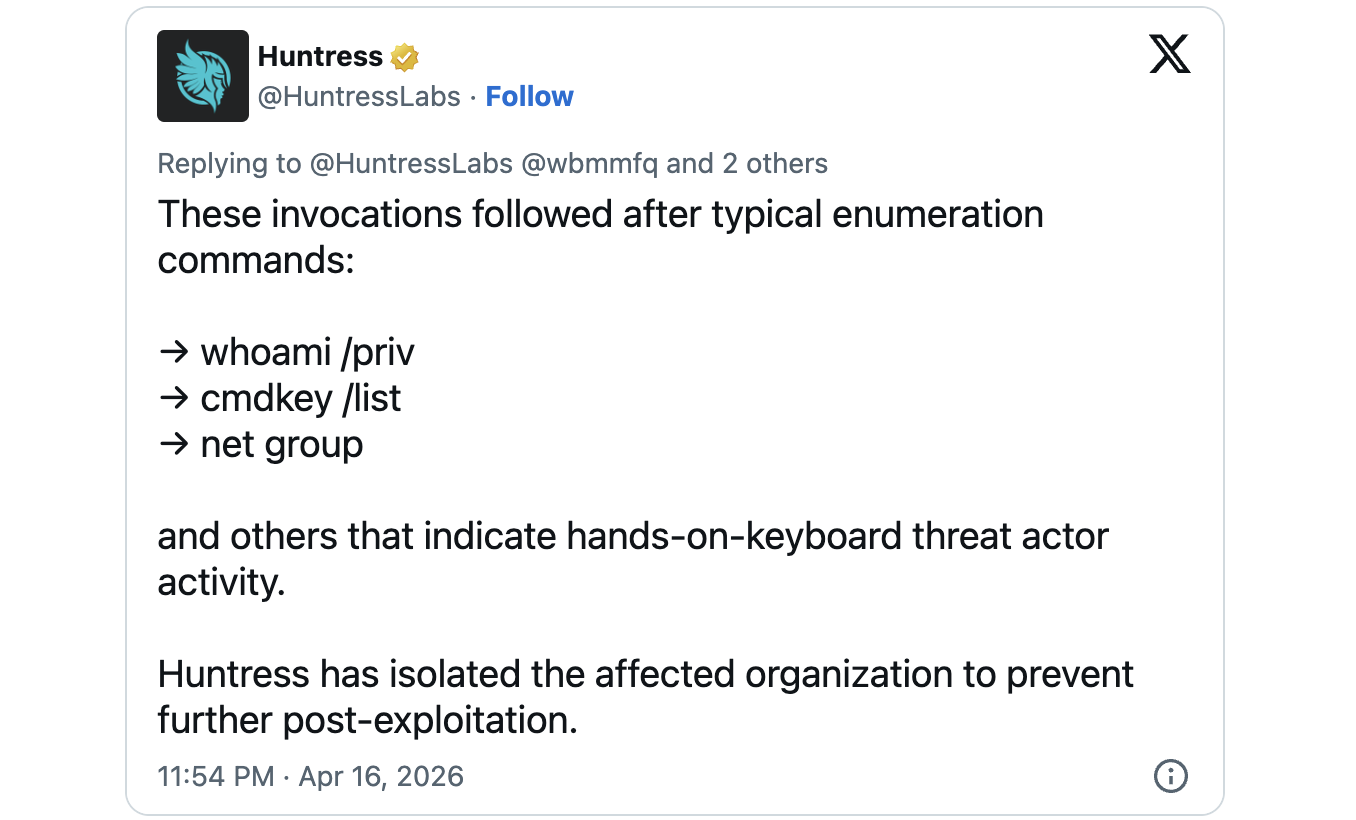
In addition they noticed UnDefend and RedSun exploits on a Home windows software that was once breached the usage of a compromised SSLVPN consumer, in assaults appearing proof of “hands-on-keyboard danger actor process.”
“The Huntress SOC is gazing using Nightmare-Eclipse’s BlueHammer, RedSun, and UnDefend exploitation tactics,” the researchers mentioned.
Two zero-days nonetheless looking forward to a patch
Whilst Microsoft is now monitoring the BlueHammer vulnerability as CVE-2026-33825 and has patched it within the April 2026 safety updates, the opposite two flaws stay unaddressed.
As BleepingComputer prior to now reported, attackers can use the RedSun exploit to realize SYSTEM privileges on Home windows 10, Home windows 11, and Home windows Server 2019 and later programs when Home windows Defender is enabled, even after making use of the April Patch Tuesday patches.
“When Home windows Defender realizes {that a} malicious document has a cloud tag, for no matter silly and hilarious explanation why, the antivirus that is intended to offer protection to comes to a decision that this is a just right concept to simply rewrite the document it discovered once more to it is authentic location,” the researcher defined. “The PoC abuses this behaviour to overwrite machine recordsdata and achieve administrative privileges.”
“Microsoft has a buyer dedication to research reported safety problems and replace impacted units to offer protection to shoppers once conceivable,” a Microsoft spokesperson instructed BleepingComputer previous this week when contacted for more info at the disclosure problems reported by means of the nameless researcher.
“We additionally make stronger coordinated vulnerability disclosure, a broadly followed business follow that is helping be sure problems are moderately investigated and addressed earlier than public disclosure, supporting each buyer coverage and the protection analysis neighborhood.”

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Self sufficient Validation Summit (Would possibly 12 & 14), see how independent, context-rich validation reveals what is exploitable, proves controls dangle, and closes the remediation loop.



