Seems can also be deceiving, such a lot in order that the acquainted icon may masks malware designed to thieve your information and cash.
06 Oct 2025
•
,
5 min. learn
PDF recordsdata have transform a staple of our day-to-day virtual lives, each at paintings and at house. They paintings seamlessly throughout running programs and units, and so they couldn’t be more uncomplicated to create and proportion. On a daily basis, numerous PDF (Transportable File Structure) recordsdata are exchanged throughout inboxes and messaging platforms, and chances are high that, you’ve opened one these days with no 2nd concept.
Then again, this all could also be partially what makes PDFs the easiest hide for all approach of threats. To start with look, PDF recordsdata appear about as benign as virtual recordsdata get. To the bare eye, a malware-laced PDF or, certainly, some other document kind spreading below the guise of a PDF doesn’t essentially glance a lot other from an odd bill, resume or executive shape.
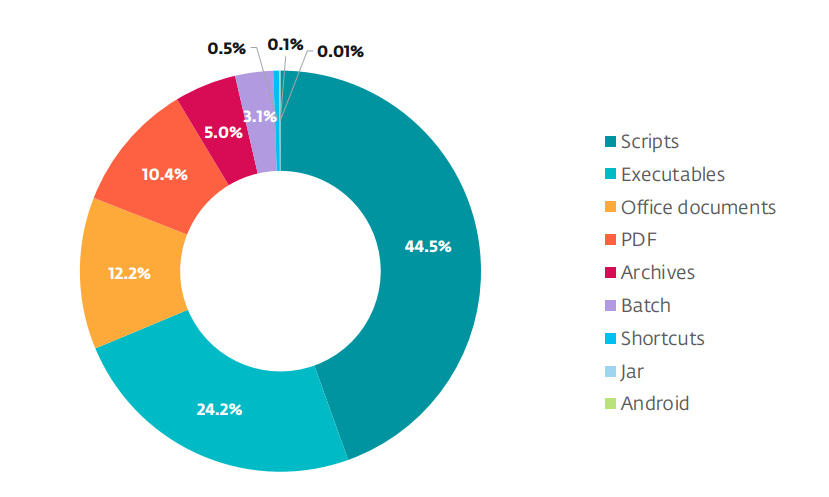
Safety researchers are seeing PDF recordsdata display up time and again as lures particularly in mass social engineering campaigns, but additionally in APT crew operations or even in subtle zero-day assaults. Fresh ESET telemetry confirms that PDFs rank a few of the best document sorts abused in malicious campaigns.
A wolf in sheep’s clothes
Booby-trapped PDFs in most cases arrive as electronic mail attachments or hyperlinks in phishing messages that trick sufferers into taking motion. As is commonplace with social engineering campaigns, the lures are moderately crafted to spark emotion, reminiscent of urgency (suppose “ultimate realize”), worry (“account suspended”) or interest (“check effects to be had”). The top objective is to get you to decrease your guard and the usage of all approach of exhortations, reminiscent of “pay now” and “overview instantly”, drive you into opening a document or clicking a hyperlink.
The assault ways range and feature over time incorporated:
- Embedded scripts that run when the document opens, letting attackers release quite a lot of movements and deploy further payloads. JavaScript in PDFs can carry out official duties, reminiscent of growing interactive paperwork and automating processes, however it’s additionally abused to obtain or execute code.
- Hidden or malicious hyperlinks: Hyperlinks contained within the PDF can redirect you to credential-harvesting pages or urged you to obtain a malicious ZIP archive or executable.
- Exploiting vulnerabilities in PDF readers: Malformed items or specifically crafted content material can profit from insects in susceptible variations of commonplace PDF readers and result in code execution, as used to be the case with a tool loophole affecting Adobe Reader and documented through ESET researchers.
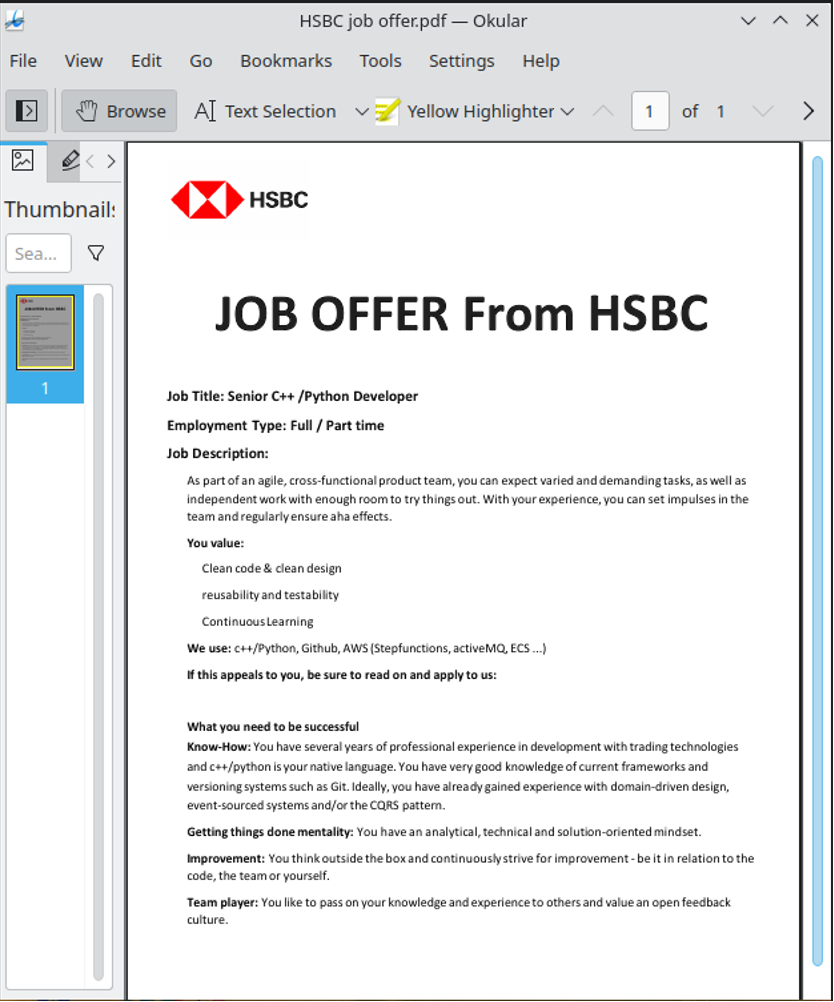
- Recordsdata that handiest pose as PDFs and are as a substitute scripts, executables and even malicious Microsoft Place of job recordsdata, amongst others, however their true document extensions is also hidden. Whilst you might even see a document known as “bill.pdf”, clicking it if truth be told launches an executable.
Talking of which, previous this yr we wrote a few marketing campaign that allotted the Grandoreiro banking trojan and began with an electronic mail urging the sufferer to open a record, ostensibly in PDF structure. In fact, it’s a ZIP archive containing, amongst different issues, a VBScript document that unleashes Grandoreiro at the tool and in the end offers criminals get admission to to the sufferer’s banking credentials.


Find out how to spot a suspicious PDF
So what are the pink flags that are supposed to put you on top alert?
- The document has a deceptive visual identify or double extension. That is the case with names like bill.pdf.exe or record.pdf.scr, particularly the place attackers forged their nets vast and intend to ensnare as many of us as conceivable. Those recordsdata if truth be told aren’t PDFs in any respect – they’re simply dressed as much as seem like PDFs.
- The sender’s electronic mail deal with or identify doesn’t fit what the document says. The e-mail sender’s deal with isn’t the same as the group that the record claims to be from, or the area is misspelled or suspicious.
- The PDF is compressed within a ZIP or RAR archive. The PDF arrives within a ZIP or RAR – that’s in a bid to bypass detection through electronic mail filters.
- All the message is surprising or sounds “out of context”. Ask your self: did I ask for this document? Do I do know the sender? Does it make sense for them to ship it to me?
What to do in the event you obtain a suspicious PDF
If a PDF raises pink flags, take those precautions:
- Face up to the temptation to instantly obtain or open the document. The adage “when doubtful, kick it out” works right here effectively.
- Examine the sender and context. Earlier than opening the possibly sketchy attachment, touch the sender through a separate communique channel, reminiscent of a telephone name, to test that they’ve in reality despatched it.
- Take a look at the document extension and dimension. Toggle “display document extensions” or identical for your running device and make sure the document is an actual .pdf (no longer an .exe, for instance) and that the document dimension turns out believable.
- Scan the document together with your safety tool (or on the other hand, add it to VirusTotal to get a handy guide a rough first glance).
- Open with care. When you completely will have to open it and feature taken the opposite precautions, use an up-to-date PDF viewer with sandboxing or a secure view function enabled (reminiscent of Adobe’s Secure View).
What to do in the event you suspect you’ve opened a sketchy PDF
- Disconnect from the web to cut back the danger of knowledge exfiltration or additional payload downloads.
- Run a complete laptop scan with an up to date safety answer. When you don’t have any, run a one-time take a look at as to be had courtesy of ESET’s loose scanner.
- Take a look at working processes and community connections for anomalies. When you’re no longer skilled, get a qualified to analyze.
- Alternate passwords particularly in your monetary and different treasured accounts, specifically the place you think your credentials can have been stolen – however accomplish that from a tool rather than the only the place you downloaded the PDF.
- Record the incident in your IT/safety workforce (if you opened the document in your paintings device).
Parting ideas
Those tried-and-tested regulations will cross a ways in opposition to conserving you protected from dodgy PDFs:
- When you weren’t anticipating the document, don’t open it, no less than no longer with out checking first that the document is official.
- Teach your self on the right way to acknowledge phishing scams.
- As many assaults depend on recognized tool vulnerabilities, stay your running device and all different tool, together with PDF readers, up-to-date.
- Permit Secure View or sandbox mode for your PDF reader of selection and imagine adjusting or disabling your JavaScript settings in it.
- Use respected, multi-layered safety tool on all of your units.
It’s protected to mention that cybercriminals will proceed to milk the accept as true with we position in PDFs. The usage of PDFs for malicious ends could also be a reminder that safety threats in most cases don’t arrive wrapped in suspicious-looking recordsdata. The tried-and-true rule applies right here, too: Deal with each surprising hyperlink and attachment with warning and depend on relied on gear to offer protection to your information and units.