
A technical have a look at the primary 24 hours: how briefly attackers enumerate and goal newly uncovered property
Written by means of Topher Lyons – Sprocket Safety
The instant a brand new asset will get a public IP cope with, a clock begins. No longer a sluggish one. A constant, automatic one. The distance between “this simply went are living” and “that is being actively probed” is mins, now not days.
That’s now not theoretical. With the assistance of our ASM Group Version, it’s what Sprocket Safety sees often throughout buyer environments, and it’s precisely what attackers depend on: your workforce received’t know one thing is uncovered till it’s already too past due.
The First 24 Hours: A Technical Timeline
T+0: The asset is going are living.
A developer pushes a brand new cloud example. A misconfigured firewall rule opens a port. A supplier portal spins up on a subdomain no one flagged. Regardless of the purpose, a brand new internet-routable endpoint now exists, and safety doesn’t get a notification.
T+5 to T+60 mins: The scanners in finding it.
Computerized scanning infrastructure sweeps all of the public information superhighway, repeatedly. Shodan, Censys, ShadowServer, and others index new hosts on a rolling foundation (Censys on my own covers tens of hundreds of ports).
Inside an hour, your asset has its open ports catalogued, banner data grabbed (internet server model, TLS cert, SSH fingerprint), and reaction signatures in comparison towards identified vulnerability databases.
T+1 to T+6 hours: Enumeration starts.
Via now your asset displays up in Shodan and Censys queries. Computerized assault tooling begins its personal recon cross: on the lookout for carrier variations, open control ports (RDP on 3389, SSH on 22, admin panels on 8080/8443), and TLS certs that pivot to comparable domain names and subdomains.
In case your new asset has a cert, attackers can be informed so much about your broader infrastructure with out ever touching one thing you had been gazing.
T+6 to T+12 hours: Lively probing.
Passive discovery flips to lively concentrated on. GreyNoise knowledge displays scanner process spikes on this window. Credential stuffing kicks off towards SSH and RDP. Internet services and products get started getting hit with listing brute-forcing. Databases like Elasticsearch and Redis get probed for unauthenticated get right of entry to. Frameworks get examined towards identified CVEs.
None of this wishes a human to kick it off. Botnets deal with it at scale, across the clock.
T+12 to T+24 hours: Compromise.
Unit 42 researchers deployed 320 honeypots throughout cloud suppliers (RDP, SSH, SMB, Postgres) to peer what would occur. 80% had been compromised inside of 24 hours.
For the rest working with exploitable vulnerabilities, misconfigs, or default credentials, that’s all it takes to head from “this simply went are living” to “that is already owned.”
Sprocket Safety ASM Group Version unearths what attackers are on the lookout for (hidden APIs, forgotten subdomains, misconfigured services and products) prior to they in finding it first.
Get steady exterior assault floor visibility, loose.
Get ASM Visibility
Actual-Global Instance: The Hidden API No person Knew Existed
The timeline above assumes you recognize what’s uncovered. One of the most deadly exposures are property your individual workforce has no thought are public, and the trail to discovering them is precisely what attackers use.
With a up to date discovering, ASM flagged a public-facing logistics internet app and, as a part of URL enumeration, pulled down and analyzed the compiled JavaScript package being served to browsers.
Buried in that JS report used to be a connection with a backend API. No longer in any asset stock. No longer one thing any individual explicitly uncovered. However are living, public, and fully open.
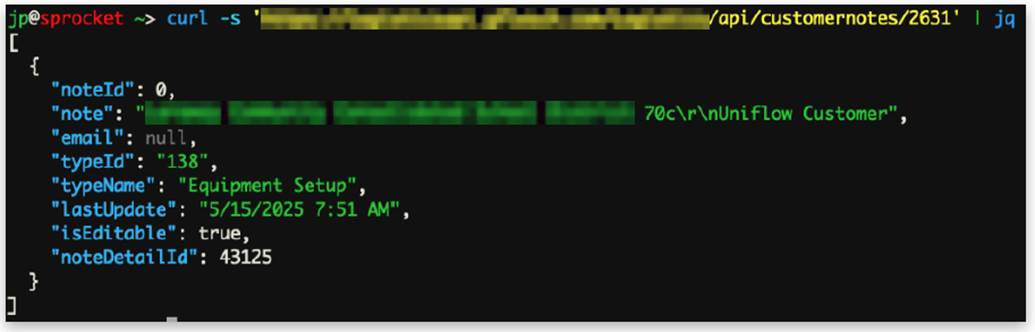
Human testers ran the similar request an attacker would:
curl -s 'https://logisticsapi.[redacted].com/Logistics/api/customernotes/2631' | jq
The server answered. No token, no credentials.
Via iterating via endpoint IDs, testers pulled:
- Buyer names, e-mail addresses, and account notes
- Cleartext credentials for buyer accounts
- Default instrument usernames and passwords
- Interior community data for deployed units
- Worker names and e-mail addresses
The overall chain from public site to JS research to hidden API to unauthenticated knowledge sell off mirrors precisely what attacker tooling does throughout enumeration. The adaptation right here used to be that Sprocket Safety were given there first.
The Compounding Drawback: You Don’t Know What You Have
Unit 42’s assault floor analysis discovered that the common group’s exterior assault floor adjustments by means of greater than 300 new services and products each and every month. Greater than 20% of externally available cloud services and products flip over on a per thirty days foundation.
Safety groups aren’t maintaining. The basis purpose in maximum breach investigations comes again to a variation of the similar observation: “We didn’t know that used to be on the net.”
An asset you don’t find out about is one you’ll be able to’t patch, observe, or pull offline when issues pass sideways. And because the instance above displays, it’s frequently now not one thing somebody intentionally deployed.
It’s a backend carrier that were given referenced in a JavaScript report no one concept to have a look at.
From Came upon to Validated: The ASM-to-Pentesting Trail
Discovering the hidden API is the first step. Working out what’s in fact exploitable and what the true trade have an effect on is takes human eyes.
That’s the trail Sprocket Safety is constructed round. ASM Group Version often enumerates your exterior assault floor: finding property, pulling JavaScript bundles, mapping subdomains, surfacing what’s in fact visual from out of doors your community.
When one thing surprising displays up (an API that shouldn’t be public, an admin panel no one flagged, an abnormal cert), that feeds at once into human-led checking out.
That’s precisely how the instance discovering performed out. ASM’s enumeration surfaced the JavaScript reference. Human testers validated the unauthenticated get right of entry to, mapped the uncovered endpoints, and documented actual knowledge publicity with transparent remediation steps. No longer a scanner alert. A real discovering.
Steady ASM discovery feeding into centered human checking out is what closes the distance between “we predict our assault floor is X” and “right here’s what an attacker in fact sees.”
To find Your Belongings Sooner than Attackers Do
The primary-24-hours downside isn’t solved by means of sooner patching. It’s solved by means of figuring out what you will have prior to attackers in finding it.
Sprocket ASM Group Version offers you steady, attacker-perspective visibility into your exterior assault floor, loose.
See what’s uncovered, uncover what you didn’t know used to be public, and prioritize what in fact issues.
The clock is already working.
Backed and written by means of Sprocket Safety.



