Right here’s what to grasp in regards to the malware with an insatiable urge for food for precious information, such a lot in order that it tops this 12 months’s infostealer detection charts
22 Oct 2025
•
,
3 min. learn

Infostealers stay one of the vital chronic threats on lately’s danger panorama. They’re constructed to quietly siphon off precious data, generally login credentials and monetary and cryptocurrency main points, from compromised techniques and ship it to adversaries. And so they accomplish that with nice good fortune.
ESET researchers have tracked a large number of campaigns lately the place an infostealer was once the general payload. Agent Tesla, Lumma Stealer, FormBook and HoudRAT proceed to make the rounds in huge numbers, however in keeping with the ESET Danger File H1 2025, one circle of relatives surged forward of the remainder within the first part of this 12 months: SnakeStealer.
A danger is born
Detected by way of ESET merchandise principally as MSIL/Secret agent.Agent.AES, SnakeStealer first gave the impression in 2019. Early studies traced it to a danger at the start advertised as 404 Keylogger or 404 Crypter on underground boards ahead of it rebranded below its present title.
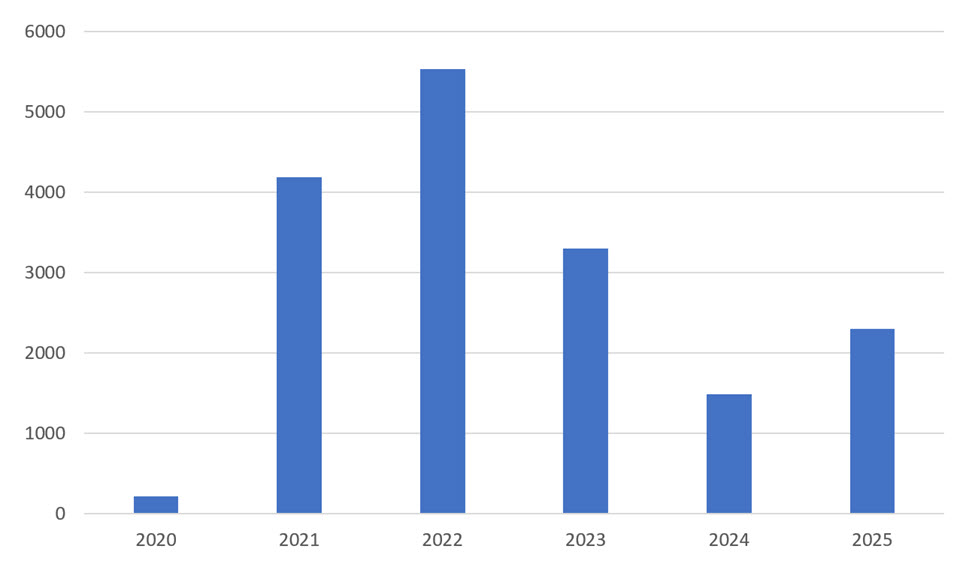
In its early variants, SnakeStealer used Discord to host its payloads, which sufferers unwittingly downloaded after opening a malicious e mail attachment. Whilst web hosting malware on reliable cloud platforms wasn’t new, the popular abuse of Discord quickly become an indicator tactic. SnakeStealer reached its first large wave of process in 2020 and 2021, spreading globally with none transparent regional center of attention.
In the meantime, the supply strategies various. Phishing attachments nonetheless stay the main vector, however the payload itself could also be disguised in more than a few paperwork, together with password-protected ZIP information, weaponized RTF, ISO and PDF information, and even bundled with different malware. Infrequently, SnakeStealer hides inside of pirated instrument or pretend apps, which speaks to the truth that now not each compromise starts with a malicious e mail.
Malware-as-a-service: A winning ‘trade style’
Like many different trendy threats, SnakeStealer follows the malware-as-a-service (MaaS) style. Its operators hire or promote get right of entry to to the malware, whole with technical beef up and updates, which makes it simple for even low-skilled attackers to release their very own campaigns.
SnakeStealer’s contemporary resurgence is not any twist of fate. After Agent Tesla started to say no and lose developer beef up, underground Telegram channels began recommending SnakeStealer as its successor. This endorsement, blended with the ease of its MaaS setup and its ready-made infrastructure, propelled SnakeStealer to the highest of detection charts, such a lot in order that SnakeStealer was once lately accountable for nearly one-fifth of world infostealer detections as tracked by way of ESET telemetry.

Key options
SnakeStealer would possibly not smash new flooring, nevertheless it’s polished, dependable, and simple to deploy. It provides a complete toolkit of functions that’s standard of professional-grade info-stealing malware, and given its modularity, attackers can transfer options on or off to fit their wishes.
- Evasion: As a way to keep below the radar, SnakeStealer can terminate processes related to safety and malware research gear and take a look at for digital environments.
- Endurance: It alters Home windows boot configurations to care for get right of entry to on compromised techniques.
- Credential robbery: It extracts stored passwords from internet browsers, databases, e mail and chat purchasers, together with Discord, and Wi-Fi networks.
- Surveillance: It captures clipboard information, takes screenshots and logs keystrokes.
- Exfiltration: It sends stolen information by the use of FTP, HTTP, e mail, or Telegram bots.
How to give protection to your self
Whether or not you’re a person consumer or a trade, those steps can lend a hand scale back the danger in opposition to infostealers like SnakeStealer:
- Be skeptical of unsolicited messages. Deal with attachments and hyperlinks, particularly from unknown senders, as doable threats, despite the fact that they seem reliable. Examine them with the sender via different channels.
- Stay your machine and apps up to date. Patching identified vulnerabilities in a well timed approach reduces the danger of compromise stemming from instrument loopholes.
- Allow multi-factor authentication (MFA) anywhere conceivable. Although your password is stolen, MFA can forestall unauthorized logins.
- In the event you suspect a compromise: alternate all passwords from a blank software, revoke open periods, and track your accounts for suspicious process.
- Use respected safety instrument on all units, desktop and cellular alike.
Ultimate ideas
SnakeStealer’s upward thrust is a reminder of ways briefly the cybercrime marketplace adapts and as such displays a bigger fact about lately’s danger panorama: cybercrime has industrialized. This professionalization makes it more straightforward than ever for somebody to thieve information at scale. And as one infostealer fades, every other fills the space, armed with in large part the similar tried-and-tested ways. The excellent news is that robust cybersecurity practices will pass a ways in opposition to protecting you protected.