
A SystemBC proxy malware botnet of greater than 1,570 hosts, believed to be company sufferers, has been came upon following an investigation right into a Gents ransomware assault performed via a gang associate.
The Gents ransomware-as-a-service (RaaS) operation emerged round mid-2025 and offers a Cross-based locker that may encrypt Home windows, Linux, NAS, and BSD techniques, and a C-based locker for ESXi hypervisors.
Ultimate December, it compromised one among Romania’s biggest power suppliers, the Oltenia Power Advanced. Previous this month, The Adaptavist Team disclosed a breach that Gents ransomware indexed on its knowledge leak web site.

Despite the fact that the RaaS operation has publicly claimed round 320 sufferers, many of the assaults going on this yr, Test Level researchers came upon that the Gents ransomware associates are increasing their assault toolkit and infrastructure.
All through an incident reaction engagement, the researchers discovered that an associate for the ransomware operation attempted to deploy the proxy malware for covert payload supply.
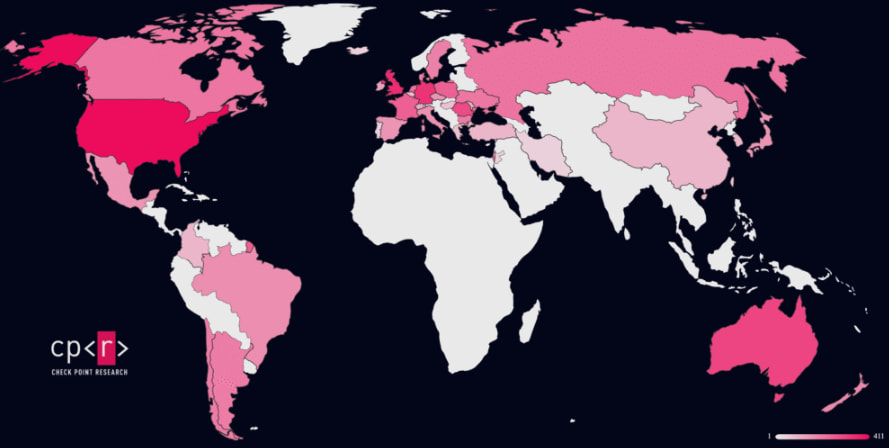
“Test Level Analysis noticed sufferer telemetry from the related SystemBC command‑and‑keep watch over server, revealing a botnet of over 1,570 sufferers, with the an infection profile strongly suggesting a focal point on company and organizational environments somewhat than opportunistic client concentrated on,” the researchers say in a record these days.
SystemBC has been round since no less than 2019 and is used for SOCKS5 tunneling. Because of its capacity to ship malicious payloads, it was once temporarily followed and likewise to ship malicious payloads. It capacity to introduce payloads onto inflamed techniques was once temporarily followed via ransomware gangs.
In spite of a regulation enforcement operation that affected it in 2024, the botnet stays energetic, and final yr Black Lotus Labs reported that it was once infecting 1,500 industrial digital non-public servers (VPS) each day to funnel malicious site visitors.
Consistent with Test Level, many of the sufferers related to Gents’s deployment of SystemBC are situated in the US, the UK, Germany, Australia, and Romania.
Supply: Test Level
“The precise Command and Keep an eye on server that was once used for the verbal exchange had inflamed a lot of sufferers around the globe. It’s most likely that almost all of the ones sufferers are corporations and organizations, for the reason that SystemBC is most often deployed as a part of human‑operated intrusion workflows somewhat than huge concentrated on,” Test Level says.
The researchers are not sure how SystemBC suits into Gents ransomware’s ecosystem and may just no longer decide if the malware was once utilized by a couple of associates.
An infection chain and encryption scheme
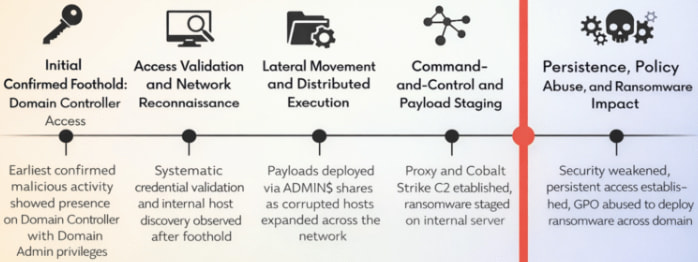
Despite the fact that Test Level may just no longer decide the preliminary get entry to vector within the noticed assaults, the researchers say that the Gents danger actor operated from a Area Controller with Area Admin privileges.
From there, the attacker checked which credentials labored and performed reconnaissance prior to deploying Cobalt Strike payloads to far off techniques by the use of RPC.
Lateral motion was once supported via credential harvesting the usage of Mimikatz and far off execution. The attackers staged the ransomware from an inside server and leveraged integrated propagation and Team Coverage (GPO) to cause near-simultaneous execution of the encryptor throughout domain-joined techniques.
Supply: Test Level
Consistent with the researchers, the malware makes use of a hybrid scheme in response to X25519 (Diffie–Hellman) and XChaCha20, with a random ephemeral key pair generated for each and every document.
Information below 1 MB are totally encrypted, whilst with higher recordsdata handiest chunks of knowledge of about 9%, 3%, or 1% had been encrypted.
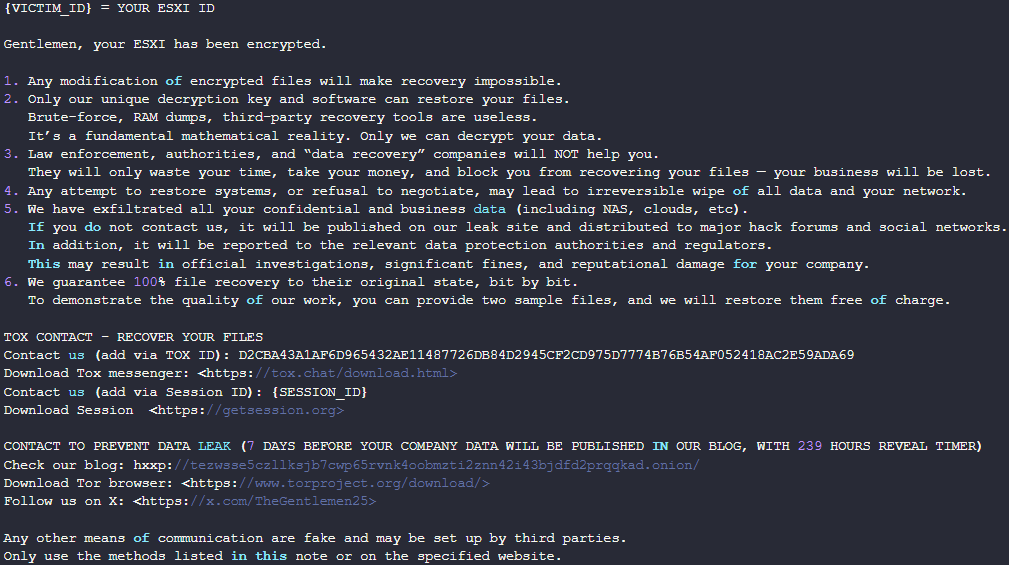
Ahead of encryption, Gents ransomware terminates databases, backup tool, and virtualization processes, and deletes Shadow copies and logs. The ESXi variant additionally shuts down VMs to make sure the disks may also be encrypted.
Supply: Test Level
The Gents ransomware doesn’t make headlines incessantly however Test Level warns that the RaaS is readily rising, promoting to recruit new ransomware associates by the use of underground boards.
The researchers consider that the usage of SystemBC with Cobalt Strike and the botnet of one,570 hosts might point out that the Gents ransomware gang is now running at the next degree, “actively integrating right into a broader toolchain of mature, submit‑exploitation frameworks and proxy infrastructure.”
With the exception of signs of compromise (IoCs) amassed from the investigated incident, Test Level additionally supplies signature-based detection within the type of a YARA rule to lend a hand defenders give protection to in opposition to such assaults.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Independent Validation Summit (Would possibly 12 & 14), see how self sufficient, context-rich validation reveals what is exploitable, proves controls cling, and closes the remediation loop.



