
The TeamPCP hacker team is threatening to leak supply code from the Mistral AI mission except a purchaser is located for the knowledge.
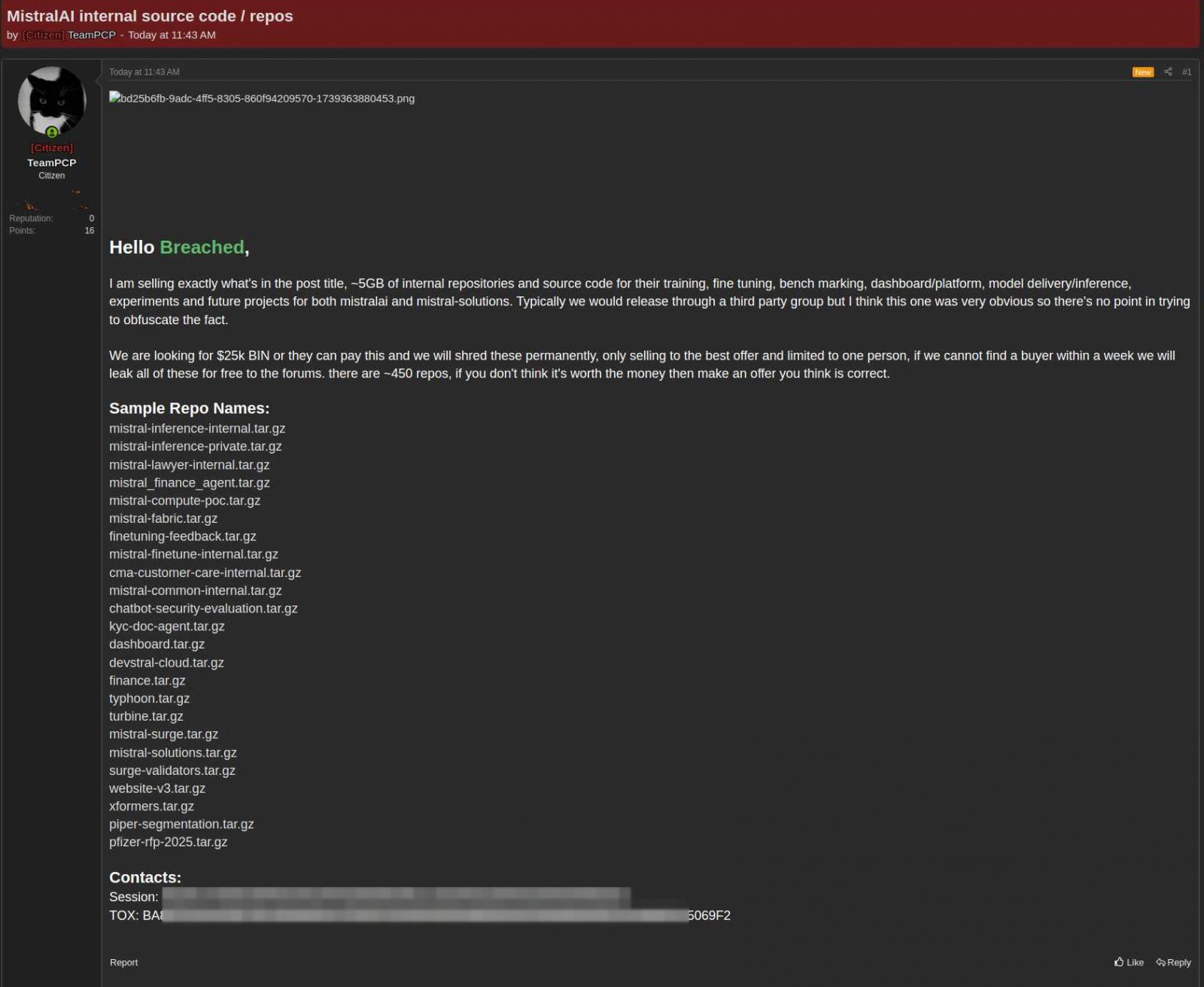
In a publish on a hacker discussion board, the danger actor is calling $25,000 for a collection of just about 450 repositories.
Mistral AI is a French synthetic intelligence corporate based by way of former researchers from Google’s DeepMind and Meta, which gives open-weight massive language fashions (LLMs), each open supply and proprietary.
In a remark to BleepingComputer, Mistral AI showed that hackers compromised a codebase control device after the Mini Shai-Hulud device supply-chain assault.
The incident began with the compromise of legitimate programs from TanStack and Mistral AI thru stolen CI/CD credentials and bonafide workflows.
Then it unfold to loads of alternative device tasks at the npm and PyPI registries, together with UiPath, Guardrails AI, and OpenSearch.
“They [the hackers] infected a few of our SDK programs for a short lived length,” the corporate stated.
TeamPCP claims to have stolen just about 5 gigabytes “of inner repositories and supply code” that Mistral makes use of for coaching, fine-tuning, benchmarking, type supply, and inference in experiments and long term tasks.
“We’re in search of $25k BIN or they are able to pay this and we will be able to shred those completely, most effective promoting to the most productive be offering and restricted to 1 particular person, if we can’t discover a purchaser inside of per week we will be able to leak all of those without spending a dime to the boards,” the hackers stated.
The danger actor seems open to negotiations, declaring that the asking worth is versatile and that consumers are unfastened to publish what they imagine is a good be offering for the 450 repositories presented on the market.
supply: KELA
Mistral AI advised BleepingComputer that the TeamPCP controlled to infect probably the most corporate’s device building equipment (SDK) programs.
In an advisory printed previous this week, the corporate stated that the breach passed off after a developer software used to be impacted by way of the TanStack supply-chain assault.
On the other hand, Mistral states that the forensic investigation made up our minds that the impacted information used to be now not a part of the core code repositories.
“Neither our hosted services and products, controlled consumer information, nor any of our analysis and trying out environments have been compromised,” Mistral advised BleepingComputer.
Previous as of late, OpenAI additionally showed that the TanStack supply-chain impacted methods of 2 of its staff who had get right of entry to to “a restricted subset of inner supply code repositories.”
A small set of credentials used to be stolen from the repositories, however the investigation discovered no proof that they have been utilized in further assaults.
OpenAI answered by way of rotating the code-signing certificate uncovered within the incident and caution macOS customers that they should replace their OpenAI desktop apps sooner than June 12, or the device might fail to release and forestall receiving updates.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Self reliant Validation Summit (Would possibly 12 & 14), see how self reliant, context-rich validation reveals what is exploitable, proves controls grasp, and closes the remediation loop.
Declare Your Spot



