If you end up attached to the similar Wi-Fi community, it is beautiful easy to SSH into any tool attached to the similar community. However outdoor that very same community, you can’t do this as a result of your ISP does not assign a novel public IP to your own home community. You may have heard that you want to arrange “port forwarding” to get into your own home servers when you find yourself out. But it surely does not must be so sophisticated. Here is a very easy and protected option to SSH into your own home community when you find yourself away.
What’s Tailscale, and the way does it paintings
The no-config setup for remoting into your servers
Tailscale is a unfastened provider that offers you a protected and personal community which your gadgets can connect with. This non-public community, referred to as a Tailnet, is a mesh community the place your telephone, computer, PC, or house server can hook up with every different with out routing their visitors thru a central server.
After getting arrange a Tailscale account and licensed your gadgets to hook up with it, they are going to act as though they are all nonetheless at the identical community irrespective of the place they’re on the planet or what connection they are the use of. Tailscale assigns every tool a brand new Tailnet IP.
For instance, in case you have a Docker container operating on a house server at this deal with.
http://192.168.1.1:8000
You’ll get right of entry to it at this deal with for your browser so long as you might be attached to the similar community as the house server. Now shall we say you’ve Tailscale operating on that house server and your pc. Irrespective of the place your pc is, it is possible for you to to get right of entry to that container’s internet UI the use of the IP deal with that Tailscale assigned to your own home server. It will glance one thing like this.
http://100.12.13.14:8000
You’ll even get Tailscale to create a MagicDNS. That means, you do not also have to bear in mind the real IP deal with of the tool. You must faraway into your server the use of the easy-to-remember MagicDNS. For instance, an deal with like this would level to that Docker container on your own home server.
http://raspberrypi.orange-wheel.ts.internet:8000
The use of the similar Tailscale IP deal with, you’ll want to additionally SSH into your own home server. So as an alternative of the use of a neighborhood IP deal with like 192.168.1.1, you’ll want to run the similar command with the Tailscale consumer and IP:
ssh raspberrypi@100.12.13.14
You’ll substitute the real IP deal with with the MagicDNS too. You’ll even use Tailscale’s personal SSH server to keep away from password authentication.
Quiz
House lab necessities
Minutiae problem
Assume you realize your hypervisors out of your switches? Put your own home lab wisdom to the take a look at.
NetworkingVirtualization{Hardware}GarageSafety
Which hypervisor kind runs at once on naked steel {hardware} with no host working device?
Right kind! A Kind 1 hypervisor, also known as a bare-metal hypervisor, runs at once at the bodily {hardware}. Standard examples come with Proxmox VE, VMware ESXi, and Microsoft Hyper-V. As a result of there is not any host OS layer in between, Kind 1 hypervisors in most cases be offering higher efficiency and potency.
Now not reasonably. A Kind 1 hypervisor runs at once on naked steel {hardware}, without a underlying host working device. Examples like Proxmox VE and VMware ESXi fall into this class. Kind 2 hypervisors, against this, run on peak of an current OS, like VirtualBox operating on Home windows.
What does VLAN stand for within the context of house lab networking?
Right kind! VLAN stands for Digital Native Space Community. VLANs mean you can logically section a bodily community into more than one remoted broadcast domain names, which is terribly helpful in a house lab for keeping apart visitors like IoT gadgets, servers, and control interfaces.
Now not reasonably. VLAN stands for Digital Native Space Community. This is a networking idea that allows you to logically divide a unmarried bodily transfer into more than one remoted community segments. House lab customers frequently use VLANs to split depended on gadgets from IoT units or visitor networks.
In ZFS, what’s the time period for a gaggle of disks pooled in combination to shape a unmarried garage useful resource?
Right kind! In ZFS, the basic garage container is named a zpool. A zpool is made up of a number of digital gadgets (vdevs), which is able to themselves encompass more than one bodily disks. All record techniques and volumes inside of ZFS are produced from a zpool.
Now not reasonably. In ZFS, the top-level garage container is named a zpool, quick for ZFS pool. Whilst ‘garage pool’ is conceptually shut, the particular ZFS time period is zpool. Zpools are composed of vdevs, and all datasets and volumes reside inside of a zpool.
Which Intel processor platform is broadly fashionable in house labs because of its low energy intake and strengthen for ECC reminiscence?
Right kind! Intel Xeon E-series processors are a staple of house labs due to their strengthen for ECC (Error-Correcting Code) reminiscence, upper core counts, and moderately modest energy intake in comparison to high-end workstation chips. Used undertaking Xeon servers can frequently be discovered cost effectively, making them fashionable price range house lab builds.
Now not reasonably. The Intel Xeon E-series platform is the go-to selection for plenty of house labbers. Xeon processors strengthen ECC reminiscence, which is helping save you silent information corruption, and used Xeon-based servers will also be received very cost effectively at the second-hand marketplace.
What’s the number one distinction between a container and a digital system?
Right kind! Boxes proportion the host working device’s kernel and isolate processes on the OS point, making them extraordinarily light-weight and speedy to spin up. Digital machines, against this, emulate complete {hardware} and run their very own whole working device, which gives more potent isolation however makes use of extra assets.
Now not reasonably. The important thing distinction is that bins proportion the host OS kernel and are a lot more light-weight, while digital machines every run their very own complete working device on peak of a hypervisor. This makes bins quicker to start out and less expensive on assets, however VMs be offering more potent isolation.
What protocol does Proxmox VE use via default for clustering and reside VM migration between nodes?
Right kind! Proxmox VE makes use of Corosync as its cluster conversation and quorum protocol. Corosync handles heartbeat messaging between nodes to discover disasters and handle cluster state. It really works along the Proxmox cluster record device (pmxcfs) to stay configuration synchronized throughout all nodes.
Now not reasonably. Proxmox VE will depend on Corosync for cluster conversation, node heartbeats, and quorum control. Corosync is an open-source cluster engine that guarantees all nodes within the cluster keep in sync and will discover when a node has failed or change into unreachable.
What’s the objective of a DMZ (demilitarized zone) in a house lab community?
Right kind! A DMZ is a community section that sits between your depended on inside community and the untrusted information superhighway. It’s designed to host products and services that want to be obtainable from the outdoor, similar to a internet server or opposite proxy, whilst proscribing what the ones uncovered products and services can succeed in to your inside community if they’re compromised.
Now not reasonably. A DMZ (demilitarized zone) is a community section used to host products and services which can be uncovered to the information superhighway, similar to a opposite proxy or recreation server. It acts as a buffer zone in order that if an internet-facing provider is compromised, attackers nonetheless can not at once succeed in your depended on inside gadgets.
What does the acronym NAS stand for?
Right kind! NAS stands for Community Hooked up Garage. A NAS tool is a devoted record garage device attached to a community, permitting more than one shoppers and gadgets to get right of entry to centralized garage. In a house lab, a NAS is frequently used for backups, media garage, and sharing information throughout digital machines.
Now not reasonably. NAS stands for Community Hooked up Garage. It refers to a garage tool attached at once to a community slightly than to a unmarried pc, enabling more than one customers and gadgets to get right of entry to shared garage. Standard house lab NAS platforms come with TrueNAS, Synology DSM, and OpenMediaVault.
Your Ranking
/ 8
Thank you for taking part in!
Putting in place your non-public Tailscale community
Simply create a Tailscale account and set up Tailscale to your server
Here is how you’ll be able to arrange your personal Tailnet the use of Tailscale. Get started via signing up for Tailscale if you do not have already got an account. You’ll use your Google, GitHub, or Microsoft account for simple enroll, when you like.
Your next step is to put in and arrange Tailscale on all our goal gadgets. For your own home server, you’ll be able to use this easy to fetch and run the legit Tailscale script.
curl -fsSL https://tailscale.com/set up.sh | sh
You must at all times read about scripts downloaded from the information superhighway earlier than operating them.
It is going to routinely establish your device and set up the proper model of Tailscale on it. It is constructed for systemd machines, but when your OS is the use of a distinct init device, you’ll more than likely want to configure it manually.
As soon as it is put in, let’s get the Tailscale provider up and operating. Use this command at the identical server.
sudo tailscale up
It must generate a URL within the terminal. Observe that hyperlink to the Tailscale web site the place you’ll be able to be requested to authenticate and upload this tool for your non-public Tailnet.
Now let’s get a Tailscale SSH server up.
sudo tailscale set --ssh
Subsequent, we’re going to wish to set up Tailscale on our gadgets. It is a platform app which you’ll be able to set up on Home windows, macOS, Linux, iOS, and Android gadgets. In finding the installers at the Tailscale web site.
For Linux computer systems, the setup is similar (curl and run the Bash script, then sudo tailscale as much as attach). On different platforms, the apps have graphical consumer interfaces for simple connectivity. Simply make sure to’re logging into the similar Tailscale account on they all.
- Logo
-
Raspberry Pi
- Garage
-
8GB
- CPU
-
Cortex A7
- Reminiscence
-
8GB
Far flung into your server by means of Tailscale
3 ways to SSH into your server
To test which gadgets are recently attached for your non-public Tailnet, pass to the Tailscale admin console and search for the record of attached machines. Right here, you’ll be able to additionally see the IP deal with that Tailscale assigned to every tool. Be aware that the system with the Tailscale SSH operating has a inexperienced SSH tag.
At the identical admin console, you’ll be able to click on the 3 dots subsequent for your server and click on the SSH button. It is going to display a button to Get started SSH Consultation. Press that button to open faraway into that system (it is going to ask you to log into your Tailscale account once more and open an SSH consultation within a browser window). This browser-based consultation avoids any firewall headaches, and it helps to keep issues easy.
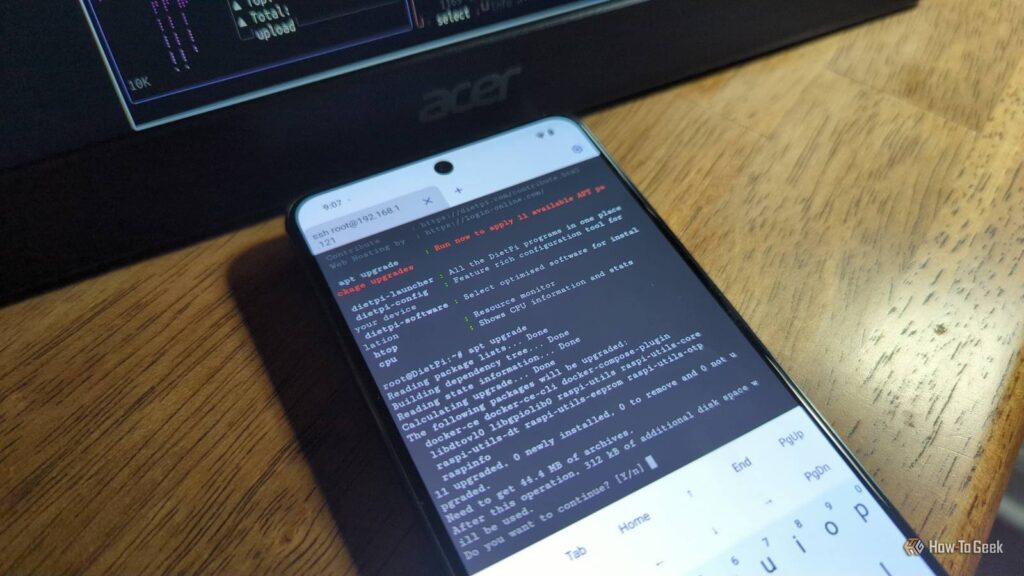
Then again, you’ll be able to SSH into your server in an ordinary terminal the use of its username (indexed underneath “System”) and the Tailnet IP. You will have to reauthorize the use of a hyperlink it generates.
ssh raspberrypi@100.12.13.14
If you wish to keep away from the authentication bother, check out connecting by means of Tailscale SSH.
tailscale ssh raspberrypi@100.12.13.14
This will likely in an instant drop you into the server surroundings.
The handy option to SSH from any tool, any place
Tailscale makes it extremely handy to faraway into your own home servers, even when you find yourself out and about. It really works on any tool, so you’ll want to even SSH into your server from, say, Termux.