
Risk actors throughout underground boards and discussion groups are an increasing number of crafting structured fraud strategies geared toward exploiting weaknesses in paintings processes of economic establishments. Relatively than remoted or opportunistic scams, those discussions replicate an arranged, process-driven way that mixes stolen id knowledge, social engineering, and information of economic workflows.
Inside of those conversations, smaller establishments, specifically small-sized to mid-sized credits unions, are regularly referenced as extra sexy objectives because of perceived gaps in verification methods and restricted fraud prevention sources.
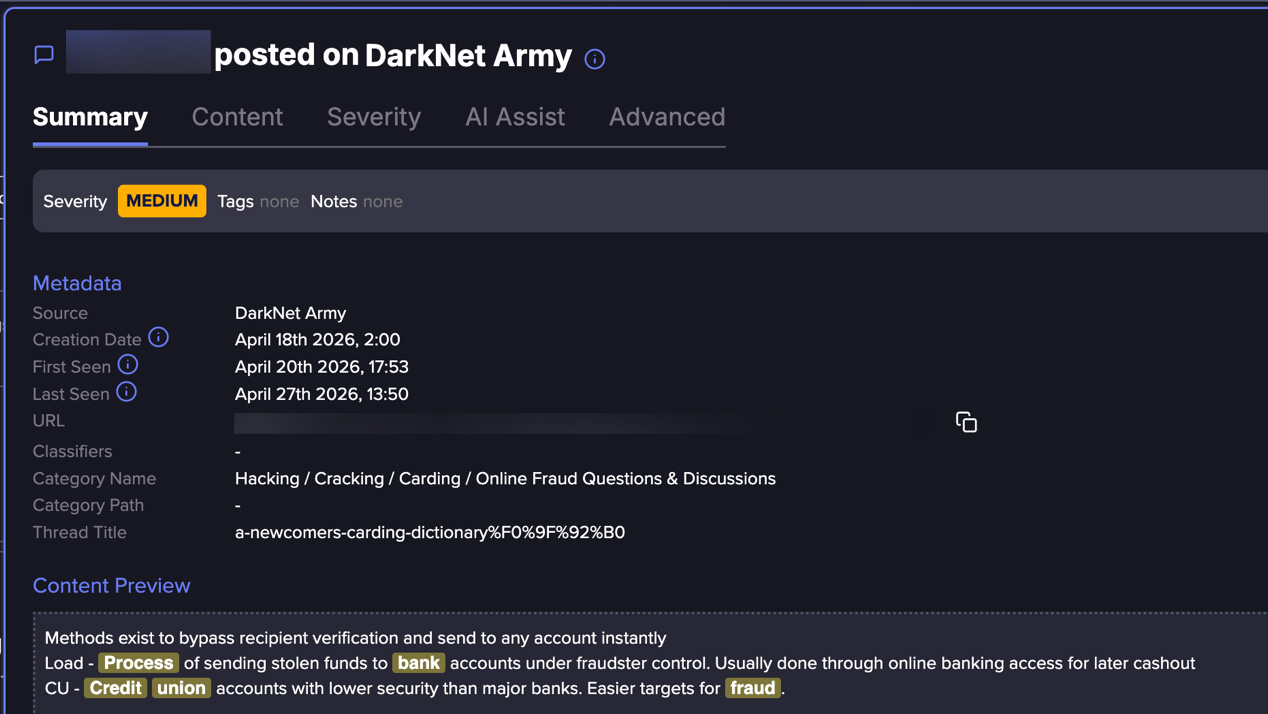
Flare researchers just lately known an in depth mortgage fraud approach circulating inside of one such underground crew, outlining how attackers can transfer via credits tests, id verification, and mortgage approval processes the usage of stolen identities whilst warding off conventional safety triggers.
The way does no longer depend on exploiting device vulnerabilities, however as a substitute makes a speciality of navigating legit onboarding and lending workflows as though the applicant have been authentic.
The construction of the publish displays a methodical way, breaking down the method from id use to mortgage approval in some way that may be constantly replicated, pointing to a extra arranged use of fraud tactics.
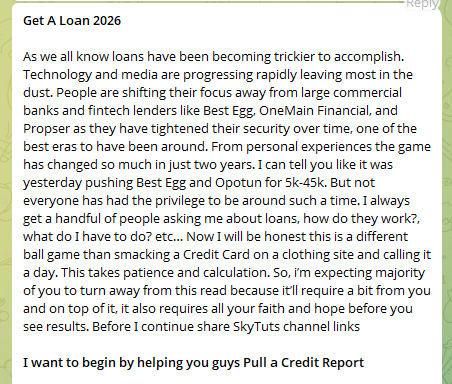
appearing the danger actor’s opening
A Procedure Constructed on Id, No longer Intrusion
At its core, this way is determined by acquiring enough private knowledge to convincingly impersonate a valid borrower. This contains identifiers comparable to names, addresses, dates of start, and in some instances, credit-related main points.
The method is all digitized, and the attacker is the usage of false id to post for a mortgage. This difference is significant: the assault does no longer “destroy the device,” however he exploits the failings in its design.
A central part of the process is the power to move id verification tests, specifically the ones according to knowledge-based authentication (KBA). Those methods generally depend on questions derived from:
In apply, a lot of this data will also be reconstructed or inferred from: publicly to be had knowledge, social media profiles, prior to now leaked datasets, and aggregated id information.
This technique highlights how attackers can look ahead to and get ready for those tests upfront, successfully turning verification right into a predictable step reasonably than a real barrier.
It demonstrates how what used to be as soon as thought to be a robust id keep an eye on can briefly be discovered, tailored to, and in the end exploited through cybercriminals, who evolve their id robbery equipment in particular to gather and bypass those necessities.
By the point a fraudulent software hits your queue, the onerous paintings is already finished. Attackers supply stolen identities, KBA solutions, and monetary histories from darkish internet boards and underground markets—lengthy earlier than they ever touch your establishment.
Flare displays hundreds of those resources incessantly, so you’ll locate uncovered knowledge on the supply, no longer after the wear and tear is finished.
Keep forward of threats and take a look at without cost.
The Fraud Workflow – step-by-step
-
Id Acquisition
Stolen private knowledge is received, together with complete id main points and background knowledge enough to impersonate a valid particular person. -
Credit score Profile Review
The attacker opinions the sufferer’s monetary profile to resolve mortgage eligibility and probability of approval. -
Verification Preparation (KBA Readiness)
Further private main points are accumulated to look ahead to and accurately resolution id verification questions. -
Goal Variety
Small- to mid-sized credits unions are decided on according to perceived weaker verification processes and decrease fraud detection adulthood. -
Mortgage Utility Submission
A mortgage software is submitted the usage of the stolen id, making sure consistency throughout all equipped knowledge. -
Id Verification Handed
KBA and usual tests are effectively finished, organising legitimacy. -
Mortgage Approval and Fund Liberate
The establishment approves the mortgage and releases budget via usual channels. -
Fund Motion and Money-Out
Budget are transferred to managed accounts, moved via intermediaries, and withdrawn or transformed to finish monetization.
Why Small/Mid Credit score Unions Are Extra Focused
Some of the extra notable facets of the process is its focal point on smaller monetary establishments. Relatively than concentrated on huge banks or extremely secured fintech platforms, the way explicitly leans towards small-sized to mid-sized credits unions, which can be perceived as:
-
Extra reliant on conventional id verification strategies
-
Much less provided with complicated behavioral fraud detection
-
Much more likely to prioritize buyer accessibility over strict controls
and thus more uncomplicated to focus on for fraud
Flare hyperlink to publish, join the unfastened trial to get right of entry to in the event you aren’t already a buyer
Whilst no longer universally true, this belief by myself is sufficient to affect attacker habits, riding concentrated on selections towards establishments believed to supply the next luck fee.
Fresh trade reporting helps this pattern. In auto lending by myself, fraud publicity is projected to achieve $9.2 billion in 2025, with smaller and regional lenders dealing with expanding drive from arranged fraud schemes.
Money-Out and Monetization
As soon as a mortgage is licensed, the operation shifts into its most important section – turning get right of entry to into cash. At this level, the attacker has already finished the onerous phase: passing id tests and organising believe beneath a stolen id. From the establishment’s viewpoint, the method seems legit, and budget are launched via usual channels simply as they’d be for an actual buyer.
The focal point then strikes to hurry and separation. Relatively than leaving budget in position, they’re briefly moved clear of the originating account, regularly via middleman accounts that create distance from the supply.
This level overlaps with broader fraud ecosystems, the place get right of entry to to further accounts and monetary channels permits budget to be routed, break up, or repositioned to cut back traceability.
What makes this section specifically efficient (and hard to locate) is that each and every step mirrors commonplace monetary habits. Transfers, withdrawals, and account task don’t seem to be inherently suspicious on their very own.
As a substitute, the danger lies in how those movements are chained in combination inside of a compressed time frame, permitting attackers to finish the cash-out earlier than detection methods or handbook opinions can intrude.
Who’s Maximum at Possibility?
The process supplies oblique perception into which people and establishments are maximum incessantly centered for id robbery.
-
Folks with Established Credit score Histories – Attackers have the benefit of concentrated on people with sturdy or solid credits profiles, expanding the possibility of mortgage approval.
-
Digitally Uncovered Folks – The ones with a vital on-line presence would possibly inadvertently reveal private main points that may lend a hand in passing verification tests.
-
Consumers of Smaller Monetary Establishments – Customers of small-sized to mid-sized credits unions would possibly face greater publicity if their establishments depend on much less complicated fraud detection methods.
This mortgage rip-off approach provides a transparent instance of ways monetary fraud is evolving. As a substitute of concentrated on methods at once, attackers are an increasing number of concentrated on the processes that encompass them, leveraging id, predictability, and believe to reach their objectives.
As those approaches develop into extra structured and out there, the road between legit task and fraud continues to blur, making detection extra advanced and requiring a extra adaptive defensive way.
Be informed extra through signing up for our unfastened trial.
Backed and written through Flare.



