
The North Korean hacker team APT37 has been turning in an Android model of a backdoor known as BirdCall in a supply-chain assault thru a online game platform.
Whilst BirdCall is a identified backdoor for Home windows programs, APT37, often referred to as ScarCruft and Ricochet Chollima, has evolved a variant for Android that doubles as adware.
In line with researchers at cybersecurity corporate ESET, the risk actor created BirdCall for Android round October 2024 and evolved no less than seven variations.
The assaults that ESET seen delivered the malware thru sqgame[.]internet, a Chinese language web page webhosting video games for Android, iOS, and Home windows. Then again, the researchers discovered that simplest Android and Home windows are centered by means of the ScarCruft assaults.
The specific platform caters to Koreans within the self sustaining Yanbian area in China, which acts as a crossing level for North Korean defectors and refugees.

Supply: ESET
BirdCall adware
BirdCall is a identified malware circle of relatives related to ScarCruft and documented since 2021. The Home windows model can file keystrokes, take screenshots, scouse borrow from the clipboard, exfiltrate recordsdata, and execute instructions.
The marketing campaign known by means of ESET introduces a up to now undocumented model of BirdCall evolved for Android, which was once delivered by means of trojanizing APKs on sqgame[.]internet.
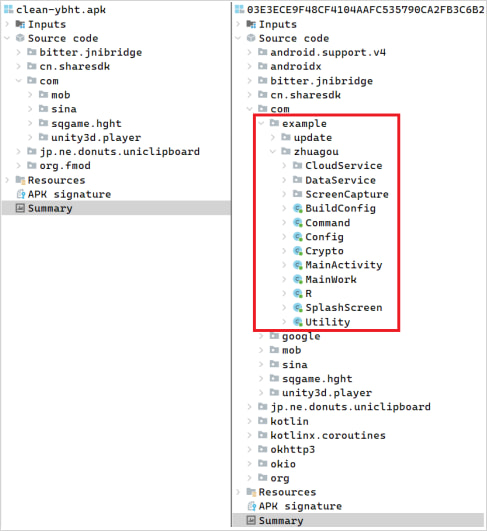
Supply: ESET
The Android variant of BirdCall has the next functions:
- Extracts IP geolocation data
- Collects touch listing, name log, and SMS
- Collects tool OS, kernel, rooted standing, IMEI quantity, MAC deal with, IP deal with, and community data
- Sends to C2 data about battery temperature, RAM, and garage, cloud configuration, backdoor model, and report extensions of pastime (.jpg, .document, .docx, .xls, .xlsx, .ppt, .pptx, .txt, .hwp, .pdf, .m4a, and .p12)
- Periodically takes screenshots
- Information audio by the use of the microphone from 7 pm to ten pm native time
- Performs a silent MP3 in a loop to forestall the suspension of its procedure
- Exfiltrates recordsdata from a specified listing
ESET’s research presentations that the Android model of BirdCall does no longer characteristic the entire instructions provide within the Home windows model but.
Lacking functions on Android come with shell command execution, visitors proxying, focused on information from browsers and messenger apps, report deletion and losing, and procedure killing.
On Home windows programs, the an infection chain starts with the set up of a trojanized DLL (mono.dll) that downloads and executes RokRAT, which then deploys the Home windows model of BirdCall.
ScurCraft is infamous for the usage of a wide vary of customized malware, together with THUMBSBD, which goals air-gapped Home windows programs, the KoSpy Android malware that in the past infiltrated Google Play, the M2RAT malware utilized in centered espionage assaults, and the Dolphin cellular backdoor.
To reduce the chance of malware infections, customers are recommended to just obtain instrument from professional marketplaces and relied on writer websites.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Self sustaining Validation Summit (Would possibly 12 & 14), see how self sustaining, context-rich validation reveals what is exploitable, proves controls grasp, and closes the remediation loop.
Declare Your Spot



