
Palo Alto Networks warned shoppers lately {that a} critical-severity unpatched vulnerability within the PAN-OS Consumer-ID Authentication Portal is being exploited in assaults.
Sometimes called the Captive Portal, the Consumer-ID Authentication Portal is a PAN-OS safety function that authenticates customers whose identities can’t be robotically mapped through the firewall.
Tracked as CVE-2026-0300, this zero-day computer virus stems from a buffer overflow weak point that permits unauthenticated attackers to execute arbitrary code with root privileges on Web-exposed PA-Sequence and VM-Sequence firewalls by the use of specifically crafted packets.
“Restricted exploitation has been seen focused on Palo Alto Networks Consumer-ID™ Authentication Portals which can be uncovered to untrusted IP addresses and/or the general public information superhighway,” Palo Alto Networks mentioned in a Wednesday advisory.
“Shoppers following usual safety absolute best practices, comparable to limiting delicate portals to relied on interior networks are at a a great deal lowered possibility.”
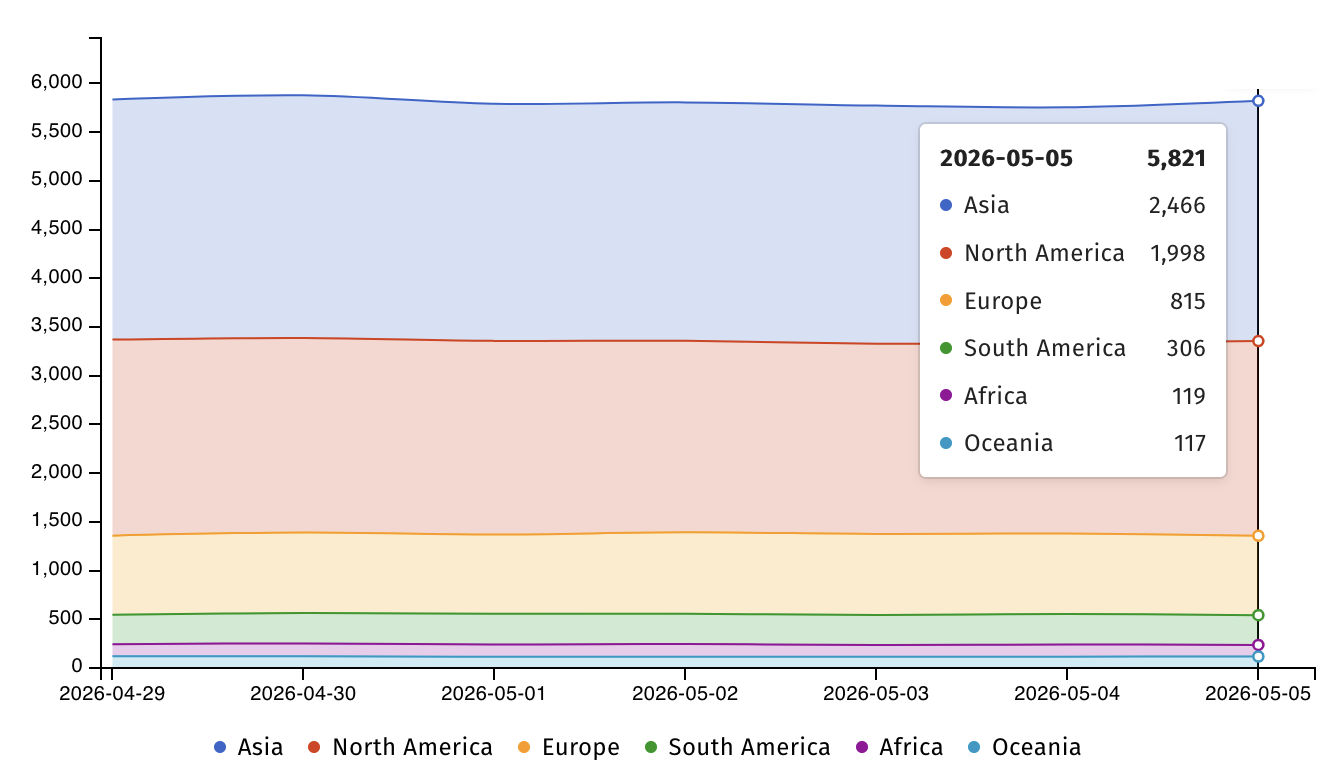
This present day, Web danger watchdog Shadowserver is monitoring over 5,800 PAN-OS VM-series firewalls uncovered on-line, maximum of them in Asia (2,466) and North The usa (1,998).
The corporate has additionally flagged the vulnerability because the best possible conceivable severity and says that admins can temporarily take a look at whether or not their firewalls are configured to make use of the prone carrier from the Consumer-ID Authentication Portal Settings web page, discovered below Instrument > Consumer Identity > Authentication Portal Settings -> Allow Authentication Portal.
Palo Alto Networks continues to be operating to deal with the zero-day, and till a patch is to be had, it “strongly” recommends that consumers protected the Consumer-ID Authentication Portal through limiting get right of entry to to relied on zones handiest or disabling the portal if that is not conceivable.
PAN-OS firewalls have often been focused in assaults, steadily exploiting zero-day safety vulnerabilities. For example, in November 2024, Shadowserver published that hundreds of firewalls have been compromised (even supposing the corporate mentioned the assaults impacted handiest “an overly small quantity”) in assaults that chained two PAN-OS firewall zero-days.
One month later, Palo Alto Networks warned that hackers have been exploiting any other PAN-OS DoS flaw to focus on PA-Sequence, VM-Sequence, and CN-Sequence firewalls, forcing them to reboot and disable firewall protections. Quickly after, in February, attackers switched to abusing 3 different PAN-OS flaws to compromise Palo Alto Networks firewalls with internet-facing control interfaces.
Palo Alto Networks says its services are utilized by greater than 70,000 shoppers international, together with 90% of Fortune 10 corporations and many of the greatest U.S. banks.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Independent Validation Summit (Might 12 & 14), see how self sufficient, context-rich validation unearths what is exploitable, proves controls cling, and closes the remediation loop.
Declare Your Spot



