
Palo Alto Networks warned consumers that suspected state-sponsored hackers had been exploiting a critical-severity PAN-OS firewall zero-day vulnerability for almost a month.
Tracked as CVE-2026-0300, this far off code execution safety flaw was once discovered within the PAN-OS Consumer-ID Authentication Portal (sometimes called the Captive Portal) and stems from a buffer overflow vulnerability that permits unauthenticated attackers to execute arbitrary code with root privileges on Web-exposed PA-Sequence and VM-Sequence firewalls.
“We’re conscious about handiest restricted exploitation of CVE-2026-0300 right now. Unit 42 is monitoring CL-STA-1132, a cluster of most likely state-sponsored danger task exploiting CVE-2026-0300. The attacker at the back of this task exploited CVE-2026-0300 to succeed in unauthenticated far off code execution (RCE) in PAN-OS device,” the corporate stated.
“Beginning April 9, 2026, there have been unsuccessful exploitation makes an attempt towards a PAN-OS tool. Every week later, the attackers effectively accomplished RCE towards the tool and injected shellcode. Following the compromise, the attackers in an instant performed log cleanup to mitigate detection by way of clearing crash kernel messages, deleting nginx crash entries and nginx crash data, in addition to casting off crash core unload information.”
After compromising the sufferers’ firewalls, the attackers deployed the open-source Earthworm and ReverseSocks5network tunneling equipment, which can be utilized to create SOCKS v5 servers and proxy tunnels on compromised units, respectively.
The EarthWorm device lets in danger actors to arrange covert verbal exchange throughout limited networks, whilst ReverseSocks5 permits them to circumvent NAT and firewalls by way of developing an outbound connection from a goal system to a controller. EarthWorm has up to now been utilized in assaults connected to the CL-STA-0046, Volt Hurricane, UAT-8337, and APT41 Chinese language-speaking danger teams.
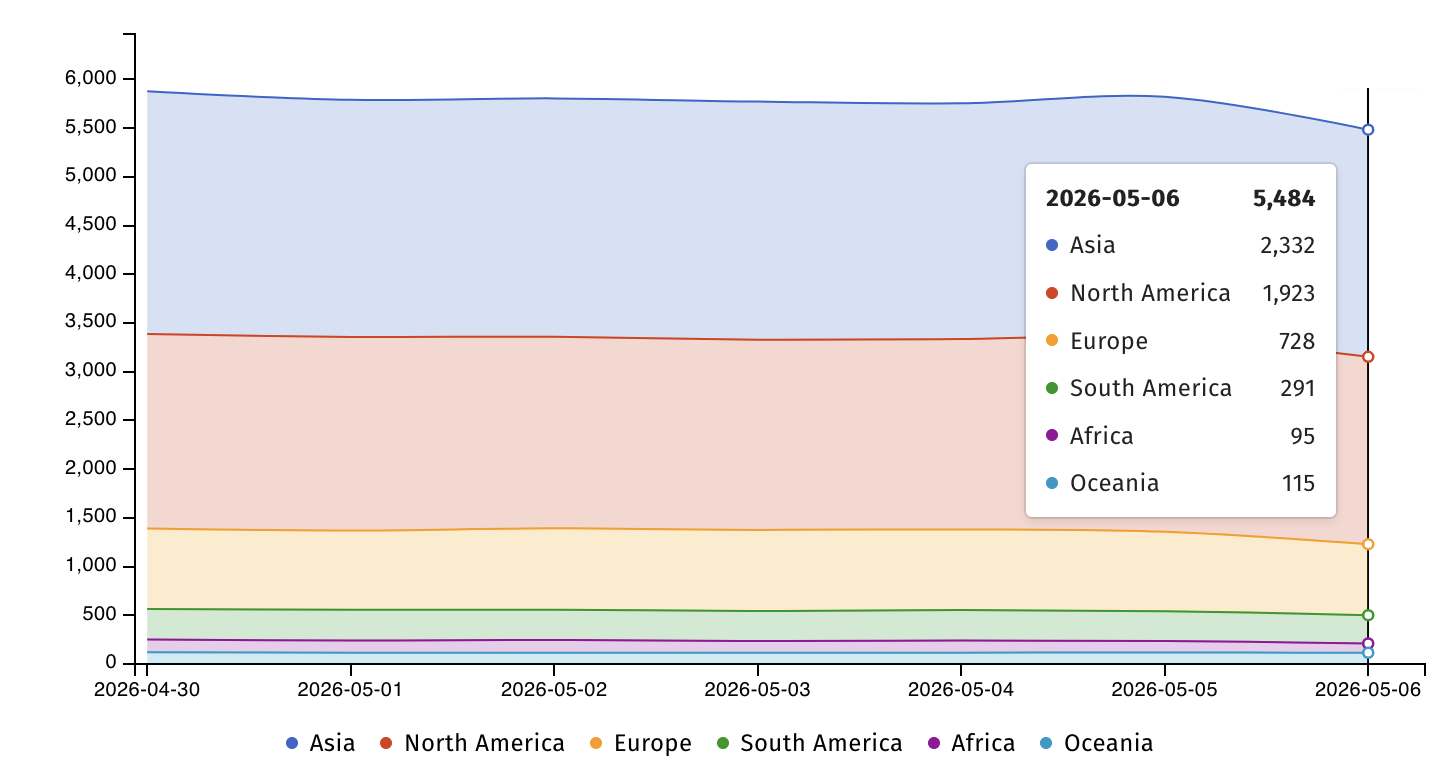
Web danger watchdog Shadowserver now tracks over 5,400 PAN-OS VM-series firewalls uncovered at the Web, maximum of them in Asia (2,466) and North The united states (1,998).
Palo Alto Networks instructed BleepingComputer the day gone by that the flaw does not have an effect on Cloud NGFW or Landscape home equipment and that it is nonetheless running on liberating patches, with the primary ones anticipated to roll out subsequent Wednesday, Would possibly 13.
Till safety updates are to be had, the corporate “strongly” instructed consumers to protected get admission to to the PAN-OS Consumer-ID Authentication Portal by way of limiting get admission to to relied on zones handiest, or by way of disabling the portal if that is not imaginable, which mitigates the chance of this factor.
Admins can temporarily take a look at whether or not their firewalls are configured to make use of the prone carrier from the Consumer-ID Authentication Portal Settings web page, discovered underneath Tool > Consumer Id > Authentication Portal Settings -> Allow Authentication Portal.
On Wednesday, the U.S. Cybersecurity and Infrastructure Safety Company (CISA) additionally added the CVE-2026-0300 zero-day to its Recognized Exploited Vulnerabilities (KEV) Catalog and ordered Federal Civilian Government Department (FCEB) companies to protected prone firewalls by way of Saturday middle of the night, Would possibly 9.
Those CVE-2026-0300 zero-day assaults are a part of a broader development by which danger teams are concentrated on edge community units (e.g., firewalls, hypervisors, routers, and VPN device), which ceaselessly lack the logging and safety device that give protection to endpoints.
In February, CISA additionally issued Binding Operational Directive 26-02, which calls for U.S. executive companies to take away community edge units that now not obtain safety updates from producers.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Self sufficient Validation Summit (Would possibly 12 & 14), see how self reliant, context-rich validation unearths what is exploitable, proves controls grasp, and closes the remediation loop.
Declare Your Spot



