
A prior to now undocumented state-backed risk actor named GopherWhisper is the usage of a Pass-based customized toolkit and legit products and services like Microsoft 365 Outlook, Slack, and Discord in assaults in opposition to executive entities.
Energetic since a minimum of 2023, the hackers were connected to China and are estimated to have compromised dozens of sufferers.
In a marketing campaign known by way of cybersecurity corporate ESET, the risk actor focused a central authority entity in Mongolia and deployed a malware set with more than one backdoors that used Slack, Discord, and the Microsoft Graph API for command-and-control (C2) verbal exchange.

GopherWhisper extensively utilized a customized exfiltration software to compress stolen knowledge and add it to the Document.io file-sharing provider.
In January 2025, ESET detected the primary GopherWhisper backdoor that was once written in Pass and named it LaxGopher. The malware can retrieve instructions from a personal Slack server, execute them the usage of the Command Steered, and obtain new payloads.
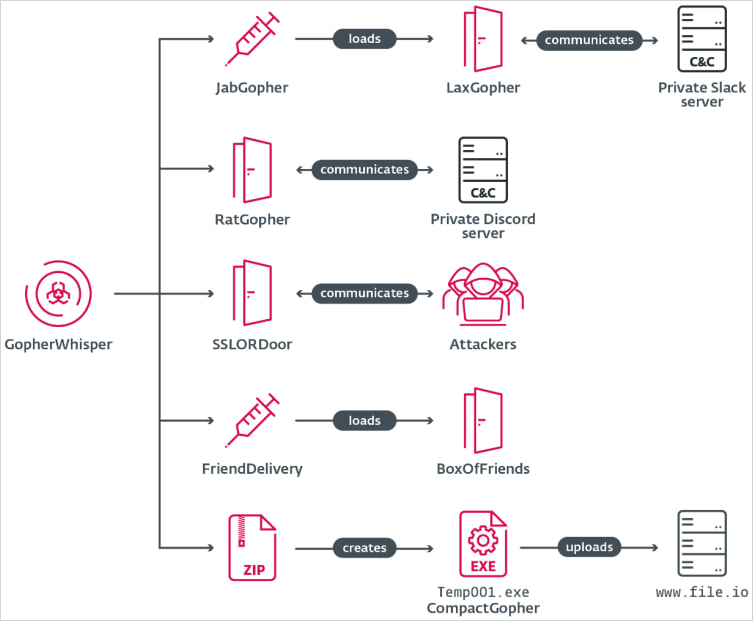
Additional investigation printed that the risk actor had deployed further malicious gear, maximum of them Pass-based:
- RatGopher – Pass-based backdoor that makes use of a personal Discord server for C2, executing instructions and posting effects again to a configured channel.
- BoxOfFriends – Pass-based backdoor that leverages the Microsoft 365 Outlook (Microsoft Graph API) to create and adjust draft emails for C2 verbal exchange.
- SSLORDoor – C++ backdoor the usage of OpenSSL BIO over uncooked sockets (port 443), in a position to executing instructions and appearing dossier operations (learn, write, delete, add) and power enumeration.
- JabGopher – Injector that launches svchost.exe and injects the LaxGopher backdoor (disguised as whisper.dll) into its reminiscence.
- FriendDelivery – Malicious DLL performing as a loader and injector that executes the BoxOfFriends backdoor.
- CompactGopher – Pass-based dossier assortment software that compresses knowledge from the command line and exfiltrates it to the file-sharing provider dossier.io.
Supply: ESET
The use of credentials hardcoded within the Pass-based backdoors, the researchers had been in a position to get right of entry to the attacker’s accounts on Slack, Discord, and Microsoft Outlook, and get better C2 verbal exchange consisting of instructions, uploaded recordsdata, and experimental task.
“We retrieved and analyzed a complete of 6,044 Slack messages going again to August 21, 2024, and three,005 Discord messages with the earliest relationship from November 16, 2023,” ESET says in a technical document as of late.
This get right of entry to, in conjunction with metadata acquired from the C2 server, additionally helped researchers hyperlink the hackers to China.
“Timestamp inspection of those Slack messages confirmed that the instructions had been issued between 12 a.m. and 12 p.m. UTC, whilst Discord message historical past printed instructions being despatched between 12 a.m. and a couple of p.m. UTC.”
Moreover, the researchers mentioned that converting the timezone to UTC+8, which matches the “locale zh-CN discovered within the metadata of the Slack server,” ESET spotted little task outdoor the 8 a.m. and 5 p.m. running hour period, expanding attribution self assurance.
ESET telemetry knowledge signifies that GopherWhister compromised 12 methods in a Mongolian executive establishment, however research of the Discord and Slack C2 site visitors printed that there are “dozens of different sufferers,” even if researchers lack visibility into their geography and task sectors.
A collection of GopherWhister signs of compromise (IoCs) is to be had from ESET to lend a hand defenders determine and block assaults from the brand new risk cluster.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Self sustaining Validation Summit (Might 12 & 14), see how self sustaining, context-rich validation reveals what is exploitable, proves controls hang, and closes the remediation loop.
Declare Your Spot



