
The MuddyWater Iranian hackers disguised their operations as a Chaos ransomware assault, depending on Microsoft Groups social engineering to achieve get right of entry to and identify endurance.
Even supposing the assault concerned credential robbery, endurance, far flung get right of entry to, knowledge exfiltration, extortion emails, and an access at the Chaos leak portal, the attackers used infrastructure and strategies related to the MuddyWater assaults.
Rapid7 researchers consider that the ransomware part was once most probably used to hide the true cyber-espionage operation and to complicate attribution.
“The method highlights the convergence between state-sponsored intrusion job and legal tradecraft, the place a large “inform” lies within the ways that had been deployed – and those who weren’t. This technique suggests the main purpose was once now not monetary acquire,” explains Rapid7.
In spite of the facade, Rapid7 has reasonable self assurance in attributing the incident to MuddyWater, a danger crew often referred to as Static Kitten, Mango Sandstorm, and Seedworm.
The realization is according to infrastructure overlap, a particular code-signing certificates that the state-sponsored crew used to signal Stagecomp and Darkcomp malware attributed to the danger actor, and quite a lot of operational tradecraft.
MuddyWater is an Iranian state-sponsored cyber-espionage crew, infamous for long-term community intrusion campaigns that align with the rustic’s Ministry of Intelligence and Safety (MOIS).
The Chaos is a ransomware-as-a-service (RaaS) operation that emerged in 2025 and is understood for big-game searching assaults, double-extortion techniques, and social engineering campaigns most commonly concentrated on organizations in america.
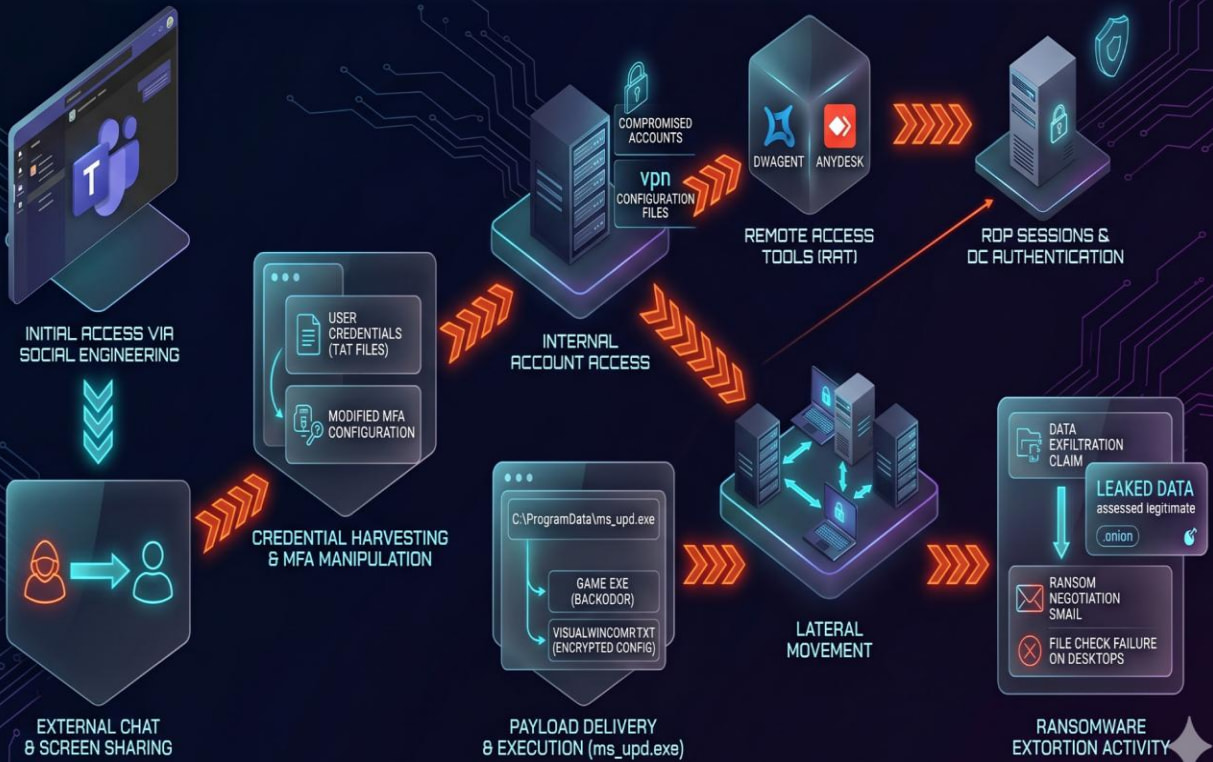
Assault development
The intrusion Rapid7 tested began thru Microsoft Groups social engineering, the place the attackers initiated chats with workers, established screen-sharing classes, harvested credentials, manipulated multi-factor authentication (MFA) settings, and, in some instances, deployed AnyDesk for far flung get right of entry to.
Credential robbery befell both by means of phishing pages masquerading as Microsoft Fast Help or by means of tricking sufferers into typing their passwords into native textual content information.
After compromising accounts, the attackers authenticated to inside methods, together with a website controller, and established endurance the usage of RDP, DWAgent, and AnyDesk.
Subsequent, they leveraged a malware loader (ms_upd.exe) to drop a customized backdoor (Sport.exe), disguised as a Microsoft WebView2 software.
The malware options anti-analysis and anti-VM tests, and helps 12 instructions, together with PowerShell and CMD command execution, record add and deletion, and chronic shell get right of entry to.
Supply: Rapid7
Rapid7 notes that MuddyWater has used ransomware previously to masks its cyber-espionage operations. In overdue 2025, the danger actor deployed Qilin ransomware in an assault towards an Israeli group.
The researchers counsel that the danger crew would possibly have pivoted to another ransomware branding following the attribution of that overdue 2025 to MOIS operatives.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Independent Validation Summit (Might 12 & 14), see how self reliant, context-rich validation reveals what is exploitable, proves controls grasp, and closes the remediation loop.
Declare Your Spot



