
Microsoft is caution {that a} contemporary Microsoft Edge browser replace presented a computer virus that breaks right-click paste in chats within the Microsoft Groups desktop consumer.
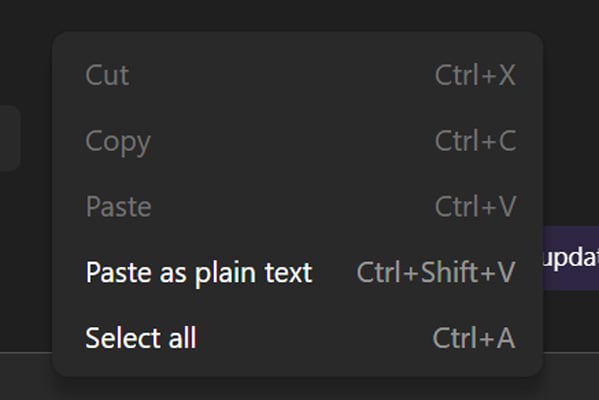
In an advisory printed on April 14, Microsoft says customers are reporting that they’re not able to paste URLs, textual content, or photographs into Groups chats when the usage of right-click context menus, with the “Paste” possibility greyed out.
To paintings across the computer virus, Microsoft says customers can nonetheless replica and paste content material the usage of keyboard shortcuts: Ctrl + C and Ctrl + V on Home windows, or Cmd + C and Cmd + V on macOS.

“Impacted customers record that they’re not able to duplicate and paste URLs, textual content, and pictures in Microsoft Groups desktop consumer chats, because the paste possibility seems greyed out when the usage of the right-click dropdown menu way,” explains Microsoft.
“To avoid affect, we advisable that customers try to replica the meant URLs, textual content, and pictures the usage of Ctrl + C and paste the usage of Ctrl + V for Home windows, and corresponding Cmd + C and Cmd + V for Mac.”
Microsoft says the computer virus is brought about by means of a up to date browser replace that presented a code regression in Microsoft Edge, which Microsoft Groups makes use of for positive capability.
Admins on Reddit and the Microsoft boards record that the issue is affecting customers in company environments in addition to person customers.
“I’ve a couple of customers on model 26072.519.4556.7438 experiencing this factor, together with myself. Can not right-click Paste, however CTRL+V and paste as textual content are allowed,” an admin posted to the Microsoft Boards.
Different customers mentioned that reinstalling Groups or clearing the cache didn’t repair the issue.
Microsoft says it recognized the motive and is rolling out a repair in levels whilst tracking telemetry to substantiate that techniques are improving.
As of the most recent replace on April 16, Microsoft has now not supplied a precise timeline for when the repair can be totally rolled out.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Self sustaining Validation Summit (Might 12 & 14), see how self sustaining, context-rich validation unearths what is exploitable, proves controls grasp, and closes the remediation loop.



