Lengthy recognized to be a candy spot for cybercriminals, small companies are much more likely to be victimized by way of ransomware than massive enterprises
18 Sep 2025
•
,
5 min. learn

Suppose your small business is simply too small to be singled out for virtual extortion? Suppose once more. Certainly, in case you’re an SMB proprietor, you’d higher think you’re a possible goal. Verizon knowledge unearths that, whilst ransomware incorporates 39% of knowledge breaches at massive organizations, the determine rises to 88% for SMBs. Huge enterprises is also extra ready to pay multimillion-dollar ransoms, however they’re incessantly additionally much more likely to have the gear and insurance policies in position to stop, locate and comprise breach chance.
In the meantime, SMB are, similar to massive firms, totally depending on their knowledge and IT infrastructure to function. The specter of everlasting knowledge loss and a complete industry shutdown has incessantly been an impressive motivator for paying the ransom price, even with none make sure that the industry will in fact get its knowledge again.
Making issues worse, attackers all the time search for extra levers to pressure cost, for instance by way of double-extortion assaults the place they each scouse borrow delicate knowledge and encrypt and threaten to put up it. Except for stealing and perilous to leak or wipe delicate inside knowledge, they may threaten DDoS assaults, regulatory court cases and, oddly sufficient, even bodily violence in some circumstances. In reality, attackers even fortunately regulate their ransom calls for to extend the percentages of a cost, as discovered by way of Verizon.
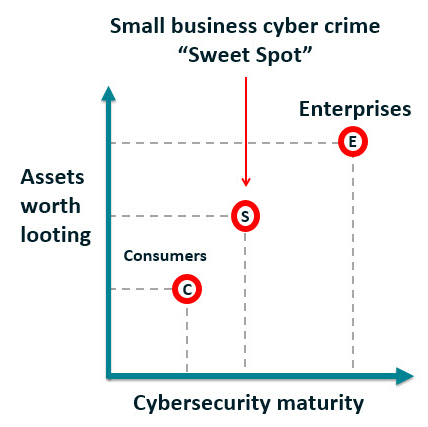
To position it bluntly, less-well defended SMBs are a juicy goal for attackers. Certainly, by way of having extra virtual belongings and cash than shoppers and less cybersecurity protections than enterprises, those companies have for lengthy been in a “cybercrime candy spot”. For those who’re prepared to stay your corporate’s knowledge protected and techniques safe, the excellent news is that it’s achievable with out breaking the financial institution.
How ransomware teams are evolving
To take on the risk, you additionally want to perceive who or what’s riding it, and the way it’s converting. For something, the ransomware-as-a-service (RaaS) industrialization of cybercrime has decreased the limitations to access and facilitated the proliferation of ransomware. In the meantime, the turnover of ransomware manufacturers additionally continues apace, led to partly by way of intensifying regulation enforcement efforts. Once a bunch is taken down, a brand new one incessantly emerges with equivalent or different ways and gear in a bid to flee scrutiny. Moreover, fast-evolving TTPs make it tougher to mitigate chance.
Then again, ransomware rebrands will also be a mirrored image of the difficulties many teams are having in turning a benefit. An research of cryptocurrency ransom bills unearths a 35% lower between 2023 and 2024. But confronted with doubtlessly fewer sufferers prepared to pay, ransomware teams seem to be doubling down on those that do, as proven by way of a find out about claiming that 55% of organizations that paid a ransom final yr did so more than one occasions; with 29% paying 3 or extra occasions.
How AI is reworking ransomware
As era advances, ransomware teams also are converting tack to extend their possibilities of luck. The standard tactics to succeed in preliminary get entry to into sufferer networks stay vulnerability exploitation, phishing and far off get entry to compromise; reminiscent of by way of credentials bought by way of infostealer malware. But AI gear may just supercharge all of those efforts.
The United Kingdom’s Nationwide Cyber Safety Centre (NCSC) warned just lately that over the following two years AI use will result in “an build up in frequency and depth of cyber threats.” Scanning for inclined sufferers (reconnaissance), vulnerability exploitation, and social engineering specifically will change into extra democratized at the cybercrime underground.
In the meantime, ESET just lately found out what’s believed to be the sector’s first AI-powered ransomware, “PromptLock.” It makes use of a sound style from OpenAI to generate malicious scripts. “The possibility of AI-powered malware that may, amongst different issues, adapt to the surroundings and alter its ways at the fly would possibly in most cases constitute a brand new frontier in cyberattacks,” ESET warns.
A separate ESET record highlights different new traits together with the semblance of “EDR killers” – designed to terminate, blind, or crash endpoint detection and reaction (EDR) tooling put in on sufferer techniques. Teams have additionally been noticed the use of “ClickFix” social engineering ways to trick customers into putting in malware on their machines.
How to give protection to your small business
A handful of SMBs know to their value what can occur following a ransomware breach. Even though already beneath monetary force sooner than a 2023 assault, British logistics company KNP therefore fell into management with the lack of 700 jobs.
To stop your small business going the similar means, undertake a prevention-first mindset by way of:
- Deploying powerful patch control to verify vulnerabilities deemed the very best chance are patched, to additional restrict the chance for preliminary get entry to and lateral motion.
- Updating identification and get entry to control insurance policies and tooling consistent with a 0 Agree with means. This implies assuming breach, steady verification of customers, least privilege insurance policies, and multi-factor authentication.
- Making sure safety device from a depended on supplier is put on all units, from endpoints, servers to far off employee laptops.
- Backing up delicate recordsdata in keeping with trade easiest practices, in order that despite the fact that recordsdata are encrypted they are able to be restored, decreasing your adversary’s leverage.
- Devising an incident reaction plan in collaboration with key stakeholders from around the industry. It must even be examined periodically to verify it’s have compatibility for objective in serving to to boost up containment following an intrusion.
- Frequently tracking your networks, endpoints and different portions of the IT surroundings for indicators of suspicious habits. Those early caution indicators must lend a hand to attenuate attacker live time.
- Updating coaching and consciousness lessons to incorporate simulation workouts that includes the most recent phishing ways, together with voice-based phishing (vishing). Your staff are each your easiest asset and your weakest hyperlink.
Importantly, you’ll want to correctly evaluation your belongings, sources and dangers, together with the ones emanating from provide chains. Stay a list of all open-source and proprietary off-the-shelf gear utilized by your company. Extra widely, asset visibility is the basis of any chance control program. In different phrases, attackers are recognized to rely on blind spots. For those who don’t know a gadget exists or what knowledge it holds, you’ll’t offer protection to it.
Because the ESET SMB Virtual Safety Sentiment 2022 has proven, many SMBs are more and more acutely aware of ransomware and different dangers dealing with their industry, however they don’t have the arrogance of their in-house cybersecurity experience. It is sensible then that a lot of them, particularly the ones with fewer sources, are more and more turning to controlled detection and reaction (MDR) services and products to and hand off the tracking to knowledgeable spouse who then plays 24/7/365 risk looking, detection and reaction, decreasing the operational burden for your in-house crew whilst making sure any ransomware task is abruptly recognized, contained and eradicated. Ransomware actors want to be despatched packing sooner than they have got a possibility to motive any harm.