
A cybersecurity researcher has printed proof-of-concept (PoC) exploits for 2 unpatched Microsoft Home windows vulnerabilities named YellowKey and GreenPlasma, that are a BitLocker bypass and a privilege-escalation flaw.
Referred to as Chaotic Eclipse or Nightmare Eclipse, the researcher describes the BitLocker bypass factor as functioning like a backdoor for the reason that inclined element is provide solely within the Home windows Restoration Atmosphere (WinRE), which is used to fix boot-related problems in Home windows.
The most recent exploits apply the researcher’s earlier disclosure of the BlueHammer (CVE-2026-33825) and RedSun (no identifier) native privilege escalation (LPE) as zero-day flaws, either one of which started to be exploited within the wild in a while after being publicly disclosed.
As in earlier instances, the researcher mentioned that the verdict to publicly expose the YellowKey and GreenPlasma vulnerabilities, together with steering on how you can leverage them, used to be pushed by way of dissatisfaction with Microsoft’s dealing with of malicious program reviews.
Chaotic Eclipse, or Nightmare-Eclipse on GitHub, stated that they are going to stay leaking exploits for undocumented Home windows vulnerabilities, even promising “a large wonder” for the following Patch Tuesday.
The YellowKey BitLocker bypass
The researcher says that YellowKey is a BitLocker bypass that is affecting Home windows 11 and Home windows Server 2022/2025. It comes to putting specifically crafted ‘FsTx’ recordsdata on a USB pressure or EFI partition, rebooting into WinRE, and triggering a shell by way of preserving down the CTRL key.
Moreover, the BitLocker bypass will have to additionally paintings with out an exterior garage by way of copying the recordsdata to the EFI partition at the goal pressure.
Consistent with Chaotic/Nightmare Eclipse, the spawned shell positive aspects unrestricted get right of entry to to the garage quantity safe by way of BitLocker.
Unbiased safety researcher Kevin Beaumont showed that the YellowKey exploit is legitimate and agreed that BitLocker has a backdoor. He really useful the usage of a BitLocker PIN and a BIOS password as a mitigation.
In an replace as of late, Chaotic Eclipse stated that “the actual root motive continues to be no longer unknown [sic] by way of most people” and that the vulnerability is exploitable even in a TPM (Relied on Platform Module) and PIN setting. Alternatively, the exploit for this model has no longer been launched.
“I feel it is going to take some time even for MSRC to seek out the actual root explanation for the problem. I simply by no means controlled to know why this vulnerability is sooo neatly hidden,” the researcher stated.
“No, TPM+PIN does no longer assist, the problem continues to be exploitable regardless, I requested myself this query, can it nonetheless paintings in a TPM+PIN setting ? Sure it does, I am simply no longer publishing the PoC, I feel what is available in the market is already unhealthy sufficient.”
Will Dormann, major vulnerability analyst at Tharros Labs, additionally showed that the YellowKey exploit labored with the FsTx recordsdata on a USB pressure however may just no longer reproduce the malicious program the usage of the EFI partition.
He defined to BleepingComputer that “YellowKey exploits NTFS transactions together with the Home windows Restoration symbol. This PIN steered occurs sooner than Home windows Restoration is entered.”
Dormann clarified the exploit procedure, announcing that in addition Home windows Restoration, “Home windows appears to be like for Machine Quantity InformationFsTx directories on connected drives, and can replay any NTFS logs.”
“The results of that is that the X:WindowsSystem32winpeshl.ini is deleted, and when Home windows Restoration is entered, slightly than launching the true Home windows Restoration setting, it pops up a CMD.EXE. With the disk nonetheless unlocked” – Will Dormann
By way of default, TPM-only BitLocker configurations release encrypted drives mechanically with out requiring person interplay. If a gadget can transparently decrypt a disk for comfort, it’s affordable to be expecting that attackers might ultimately to find techniques to abuse that procedure.
“YellowKey is an instance of an exploit for this sort of weak spot,” Dormann stated, explaining that as it leverages the car release characteristic on boot, the present YellowKey exploit does no longer paintings in a TMP+PIN setting.
It’s value noting that checking out YellowKey with a BitLocker-protected pressure should be carried out at the unique software, the place the TPM shops the encryption keys.
As such, Chaotic Eclypse’s present YellowKey exploit does no longer paintings with stolen drives however lets in get right of entry to to disks which are safe with TPM-only BitLocker without having credentials.
The GreenPlasma exploit
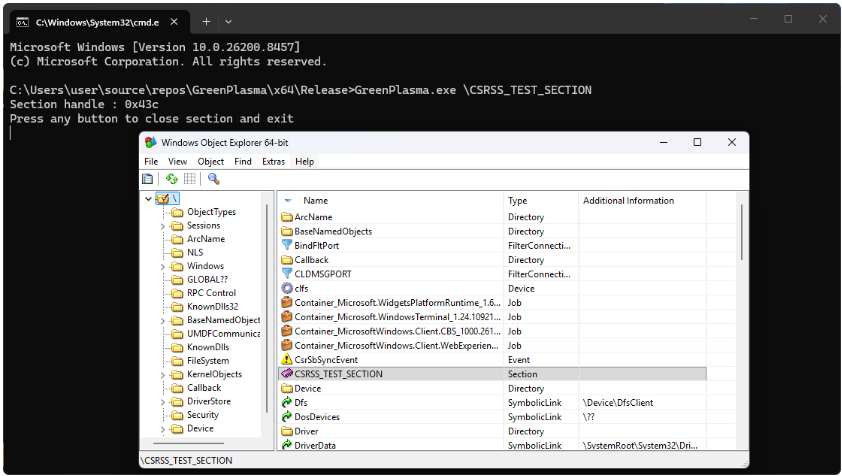
GreenPlasma is a privilege escalation safety factor which may be exploited to acquire a shell with SYSTEM permissions. Chaotic Eclipse describes it as a “Home windows CTFMON Arbitrary Segment Advent Elevation of Privileges Vulnerability.”
An unprivileged person can create arbitrary memory-section gadgets inside listing gadgets writable by way of SYSTEM, doubtlessly permitting manipulation of privileged products and services or drivers that believe the ones places.
The leaked PoC is incomplete, regardless that, and lacks the element wanted to succeed in a complete SYSTEM shell. Nonetheless, “if you are sensible sufficient, you’ll be able to flip this right into a complete privilege escalation,” Chaotic Eclipse says.
The disgruntled researcher added that the newly created part may well be influenced to govern information and more than a few products and services, together with kernel-mode drivers, into trusting particular paths that normal customers can not get right of entry to.
Supply: GitHub
Whilst the precise cases that prompted Chaotic Eclipse’s spree of exploit leaks stay unclear, the researcher has hinted at “a large wonder” for Microsoft on subsequent month’s Patch Tuesday.
Moreover, they stated that “Microsoft silently patched the RedSun vulnerability” and criticized the corporate for the hushed process and no longer assigning an identifier for the vulnerability, as used to be the case with BlueHammer.
BleepingComputer has contacted Microsoft for a touch upon Chaotic Eclipse’s newest exploit leaks, and a spokesperson mentioned that the corporate is dedicated to investigating reported safety problems, “and replace impacted gadgets to give protection to consumers once imaginable.”
“We additionally make stronger coordinated vulnerability disclosure, a extensively followed business follow that is helping be sure that problems are in moderation investigated and addressed sooner than public disclosure, supporting each buyer coverage and the safety analysis neighborhood,” a Microsoft spokesperson advised BleepingComputer.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Self reliant Validation Summit (Might 12 & 14), see how self sustaining, context-rich validation unearths what is exploitable, proves controls hang, and closes the remediation loop.
Declare Your Spot



