
Hackers are exploiting a vital vulnerability in Marimo reactive Python pocket book to deploy a brand new variant of NKAbuse malware hosted on Hugging Face Areas.
Assaults leveraging the far flung code execution flaw (CVE-2026-39987) began closing week for credential robbery, not up to 10 hours after technical main points have been disclosed publicly, in step with knowledge from cloud-security corporate Sysdig.
Sysdig researchers persisted to observe task associated with the protection factor recognized further assaults, together with a marketing campaign that began on April 12 that abuses the Hugging Face Areas platform for showcasing AI programs.

Hugging Face serves as an AI construction and gadget learning-focused platform, appearing as a hub for AI property corresponding to fashions, datasets, code, and equipment, shared some of the neighborhood.
Hugging Face Areas we could customers deploy and percentage interactive internet apps without delay from a Git repository, usually for demos, equipment, or experiments round AI.
Within the assaults that Sysdig noticed, the attacker created a Area named vsccode-modetx (an intentional typosquat for VS Code) that hosts a dropper script (install-linux.sh) and a malware binary with the title kagent, additionally an try to mimic a valid Kubernetes AI agent software.
After exploiting the Marimo RCE, the danger actor ran a curl command to obtain the script from Hugging Face and execute it. As a result of Hugging Face Areas is a valid HTTPS endpoint with a blank recognition, it’s much less prone to cause indicators.
The dropper script downloads the kagent binary, installs it in the neighborhood, and units up patience by way of systemd, cron, or macOS LaunchAgent.
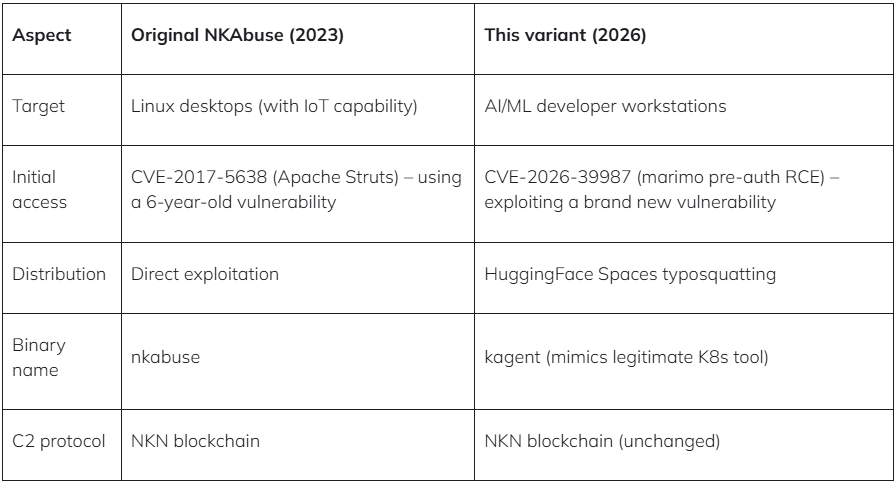
Consistent with the researchers, the payload is a in the past undocumented variant of the DDoS-focused malware NKAbuse. Kaspersky researchers reported the malware in overdue 2023 and highlighted its novel abuse of the NKN (New Roughly Community) decentralized peer-to-peer community era for knowledge alternate.
Sysdig says that the brand new variant purposes as a far flung get entry to trojan that may execute shell instructions at the inflamed device and ship the output again to the operator.
“The binary references NKN Consumer Protocol, WebRTC/ICE/STUN for NAT traversal, proxy control, and structured command dealing with – matching the NKAbuse circle of relatives first of all documented through Kaspersky in December 2023,” mentions Sysdig within the record.
Sysdig additionally noticed different notable assaults exploiting CVE-2026-39987, together with a Germany-based operator who tried 15 reverse-shell ways throughout more than one ports.
They then pivoted to lateral motion through extracting database credentials from setting variables and connecting to PostgreSQL, the place they all of a sudden enumerated schemas, tables, and configuration knowledge.
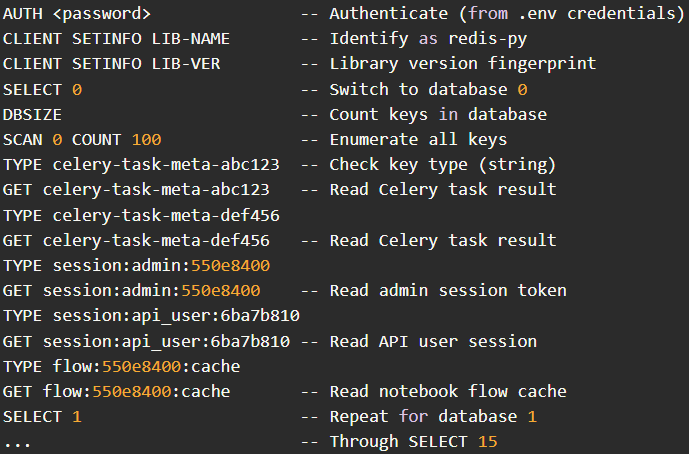
Any other actor from Hong Kong used stolen .env credentials to focus on a Redis server, systematically scanning all 16 databases and dumping saved knowledge, together with consultation tokens and alertness cache entries.
The full takeaway is that exploitation of CVE-2026-39987 within the wild has greater in quantity and techniques, and it’s the most important that customers improve to model 0.23.0 or later straight away.
If upgrading isn’t conceivable, it is suggested to dam exterior get entry to to the ‘/terminal/ws’ endpoint by way of a firewall, or block it totally.

Computerized pentesting proves the trail exists. BAS proves whether or not your controls forestall it. Maximum groups run one with out the opposite.
This whitepaper maps six validation surfaces, presentations the place protection ends, and offers practitioners with 3 diagnostic questions for any software analysis.



