This blogpost introduces our newest white paper, introduced at Virus Bulletin 2025, the place we element the operations of the North Korea-aligned danger actor we name DeceptiveDevelopment and its connections to North Korean IT employee campaigns. The white paper supplies complete technical main points, together with malware research, infrastructure, and OSINT findings. Right here, we summarize the important thing insights and spotlight the wider implications of this hybrid danger.
Key issues of this blogpost:
- The discovery and center of attention of the operations are at the social-engineering strategies.
- DeceptiveDevelopment’s toolset is most commonly multiplatform and is composed of preliminary obfuscated malicious scripts in Python and JavaScript, elementary backdoors in Python and Cross, and a gloomy internet venture in .NET.
- We offer insights into operational main points of North Korean IT staff, like paintings assignments, schedules, conversation with purchasers, and so on., amassed from public resources.
- Local, extra advanced Home windows backdoors are an occasional addition within the execution chain and are most probably shared by way of different North Korea-aligned actors.
- DeceptiveDevelopment and North Korean IT staff have other goals and method, however we believe them as tightly attached.
Creation
On this blogpost, we read about the DeceptiveDevelopment workforce and the WageMole task cluster as two tightly attached North Korea-aligned entities. WageMole is a label that we’ve got followed for actions related to North Korean IT staff. Whilst the campaigns of each are pushed by way of monetary acquire, every performs a definite and complementary function in terms of the opposite:
- DeceptiveDevelopment operators pose as recruiters, the usage of fraudulent task provides to compromise the techniques of task seekers.
- North Korean IT staff then use the tips received by way of the DeceptiveDevelopment operators to pose as task seekers. To protected an actual task place, they are going to make use of a number of ways, together with proxy interviewing, the usage of stolen identities, and fabricating artificial identities with AI-driven gear.
First, we offer a list of multiplatform gear utilized by DeceptiveDevelopment, from easy however obfuscated scripts like BeaverTail and InvisibleFerret to a fancy toolkit, TsunamiKit, focused round a .NET backdoor. We additionally expose explicit hyperlinks between extra advanced backdoors utilized by DeceptiveDevelopment, AkdoorTea and Tropidoor, and different, extra APT-oriented North Korea-aligned operations. Subsequent, we describe attention-grabbing facets of North Korean IT staff’ modus operandi, acquired from public resources, most commonly from accidentally uncovered records, testimonials of sufferers, and investigations of impartial researchers..
DeceptiveDevelopment
DeceptiveDevelopment is a North Korea-aligned workforce energetic since a minimum of 2023, fascinated by monetary acquire. Its actions overlap with Contagious Interview, DEV#POPPER, and Void Dokkaebi. The crowd goals device builders on all main techniques – Home windows, Linux, and macOS – and particularly the ones in cryptocurrency and Web3 initiatives. Preliminary get admission to is accomplished completely by way of more than a few social engineering tactics like ClickFix, and faux recruiter profiles very similar to Lazarus’s Operation DreamJob, to ship trojanized codebases throughout staged task interviews. Its commonest payloads are the BeaverTail, OtterCookie, and WeaselStore infostealers, and the InvisibleFerret modular RAT.
Concentrated on technique
DeceptiveDevelopment operators use more than a few compromise their sufferers, depending on suave social engineering methods. By means of each faux and hijacked profiles, they pose as recruiters on platforms like LinkedIn, Upwork, Freelancer, and Crypto Jobs Checklist. They provide faux profitable task alternatives to draw their goals’ pastime. Sufferers are asked to take part in a coding problem or a pre-interview job. The duty comes to downloading a venture from non-public GitHub, GitLab, or Bitbucket repositories. Those repositories include trojanized code, frequently hidden cleverly in lengthy feedback displayed well past the right-hand fringe of a code browser or editor window. Participation within the job triggers the execution of BeaverTail, the first-stage malware.
But even so those faux recruiter accounts, the addition of a brand new social engineering methodology referred to as ClickFix was once noticed. ClickFix in terms of DeceptiveDevelopment was once first reported by way of Sekoia.io in March 2025, when it was once utilized by the gang because the preliminary get admission to approach on macOS and Home windows techniques; in September 2025, GitLab noticed it getting used on Linux techniques too. The attackers direct the sufferer to a pretend task interview web site, containing an software shape that they’re requested to finish. The applying shape comprises a couple of long questions associated with the applicant’s id and {qualifications}, main the sufferer to place vital effort and time into filling within the shape and making them really feel like they’re nearly finished, and due to this fact much more likely to fall for the lure. Within the ultimate step of the appliance, the sufferer is requested to document a video of them answering the general query. The website triggers a pop-up asking the sufferer to permit digital camera get admission to, however the digital camera isn’t in reality accessed. As an alternative, an error message seems announcing that get admission to to the digital camera or microphone is these days blocked and gives a “How one can repair” hyperlink. That hyperlink results in a pop-up using the ClickFix social engineering methodology. The sufferer is prompt, in response to their working machine, to open a terminal and replica and paste a command that are supposed to resolve the problem. On the other hand, as an alternative of enabling the sufferer’s digital camera, the command downloads and executes malware.
Toolset
BeaverTail and InvisibleFerret
The primary indication of DeceptiveDevelopment task got here in November 2023, when Unit 42 reported the Contagious Interview marketing campaign; we later related this marketing campaign with the gang. Unit 42 coined the names BeaverTail and InvisibleFerret for the 2 malware households used on this marketing campaign. We documented this marketing campaign in additional element in our WeLiveSecurity blogpost from February 2025, dissecting how the danger actor makes use of those two malware households.
BeaverTail is an easy infostealer and downloader that collects records from cryptocurrency wallets, keychains, and stored browser logins. We now have noticed variants of this malware written in JavaScript, hidden in faux task demanding situations, and likewise in C++, the usage of the Qt framework and disguised as conferencing device. Its number one serve as is downloading the second-stage malware InvisibleFerret. On the finish of 2024, a brand new malware circle of relatives with capability very similar to BeaverTail emerged – it was once named OtterCookie by way of NTT Safety. OtterCookie is written in JavaScript and makes use of very equivalent obfuscation tactics. We consider that OtterCookie is an evolution of BeaverTail and is utilized by some groups inside of DeceptiveDevelopment as an alternative of the older BeaverTail, whilst different groups proceed the usage of and editing the unique codebase.
InvisibleFerret is modular malware written in Python with extra information-stealing features than BeaverTail, additionally in a position to offering faraway keep watch over to attackers. It generally comes with the next 4 modules:
- a browser-data stealer module (extracts and exfiltrates records stored by way of browsers and cryptocurrency wallets),
- a payload module (faraway get admission to trojan),
- a clipboard module (containing keylogging and clipboard logging features) – in some circumstances disbursed as a part of the payload module, and
- an AnyDesk module (which deploys the AnyDesk faraway get admission to software to permit direct attacker get admission to to the compromised gadget).
WeaselStore
As DeceptiveDevelopment developed and began to incorporate extra groups in its operations, the ones groups began editing the codebase to satisfy their very own wishes and presented new malware tooling. One such instance is a marketing campaign that ESET researchers investigated in August 2024. Along with the traditional BeaverTail and InvisibleFerret malware, the crew accountable for the marketing campaign deployed what we consider is its personal new malware – which we named WeaselStore.
WeaselStore (also known as GolangGhost and FlexibleFerret) is a multiplatform infostealer written in Cross, regardless that in Would possibly 2025, Cisco Talos reported about WeaselStore being rewritten in Python; they known as that malware PylangGhost. Because the implementation is the same, for simplicity, we discuss with each implementations as WeaselStore on this blogpost.
WeaselStore’s capability is slightly very similar to each BeaverTail and InvisibleFerret, with the primary center of attention being exfiltration of delicate records from browsers and cryptocurrency wallets. As soon as the information has been exfiltrated, WeaselStore, not like conventional infostealers, continues to keep in touch with its C&C server, serving as a RAT in a position to executing more than a few instructions.
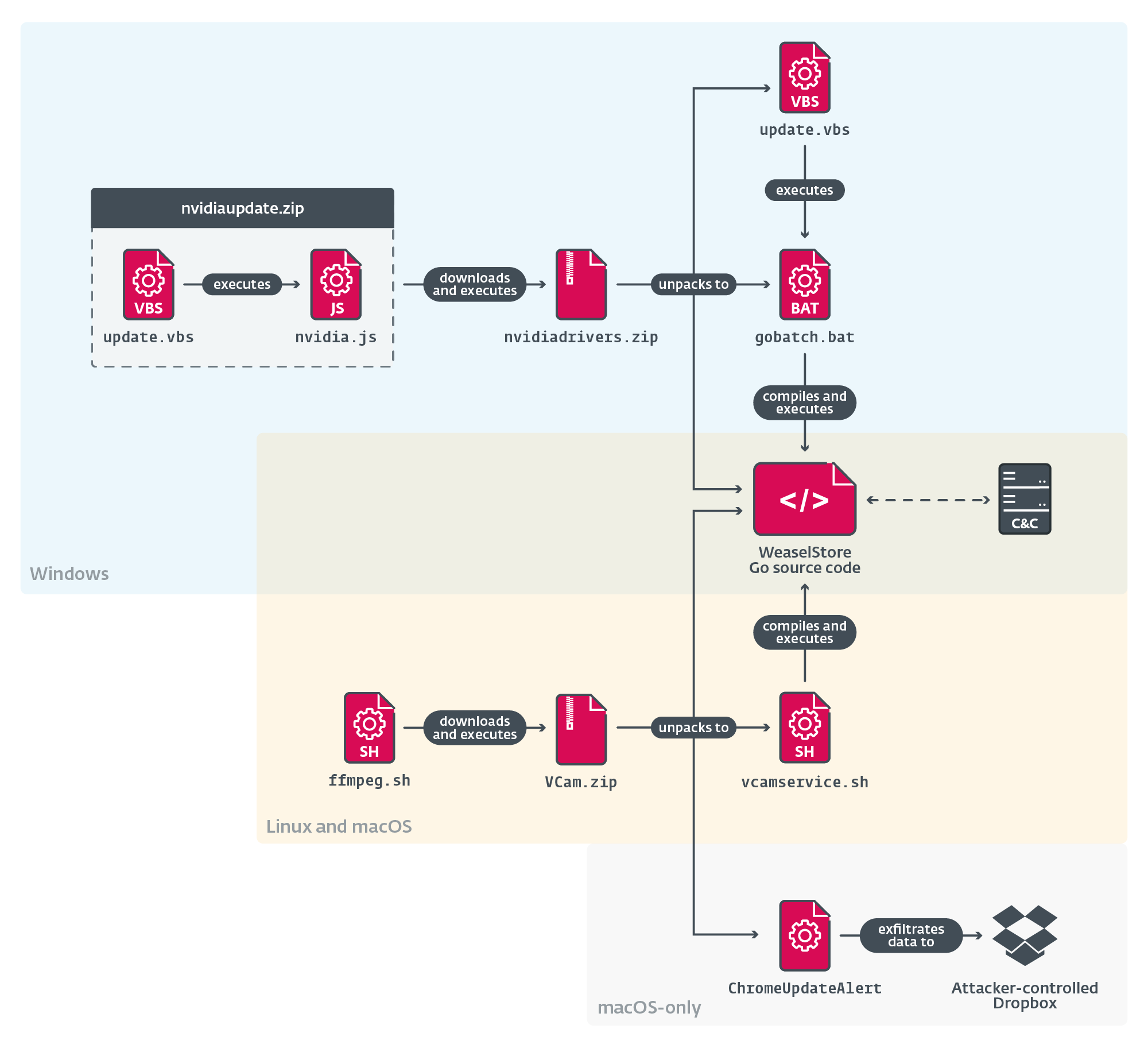
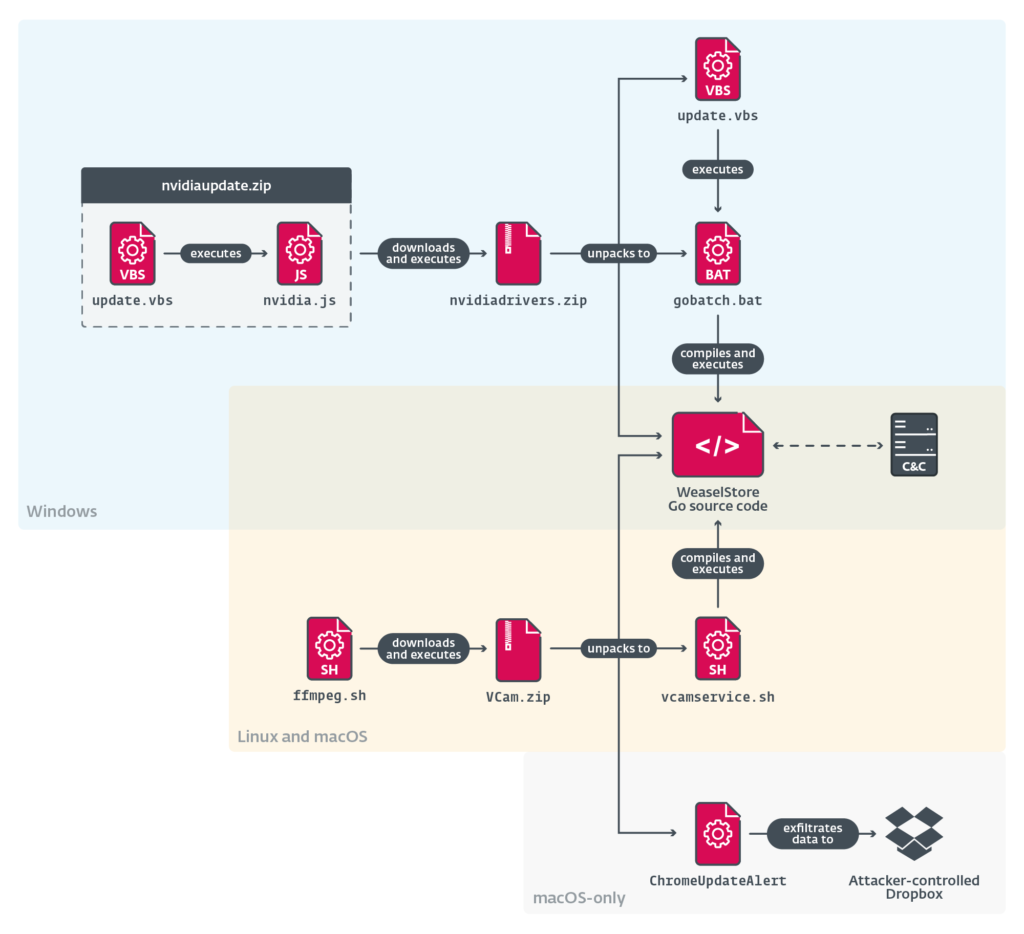
Essentially the most attention-grabbing side of WeaselStore in Cross is that it is dropped at the sufferer’s machine within the type of Cross supply code, in conjunction with the Cross atmosphere binaries essential to construct and execute it, permitting the malware to focus on 3 primary working techniques – Home windows, Linux, and macOS (see Determine 1). The set up mechanism differs in response to the sufferer’s working machine, however in all circumstances the chain ends with downloading the WeaselStore Cross supply code after which compiling and executing it the usage of a Cross construct atmosphere, which could also be supplied along.
TsunamiKit
In November 2024, a brand new model of the InvisibleFerret malware delivered a changed browser-data stealer module. This module, along with its commonplace capability, comprises a prior to now unseen, huge, encoded block with the 1st degree of the execution chain deploying a fully new malware toolkit, additionally meant for info and cryptocurrency robbery. We named this toolkit TsunamiKit, in response to the developer’s repeated use of “Tsunami” within the names of its parts (see Desk 1). The danger being publicly reported by way of Alessio Di Santo in November 2024 and by way of Bitdefender in February 2025; our white paper provides context by way of putting it within the total DeceptiveDevelopment modus operandi. The paper additionally dives into the main points of TsunamiKit’s advanced execution chain.
Desk 1. Parts of the TsunamiKit execution chain
| Part identify | Description |
| TsunamiLoader | The preliminary degree, obfuscating and losing TsunamiInjector. It comprises a quote Infrequently you by no means know the price of a second till it turns into a reminiscence, frequently attributed to Dr. Seuss. |
| TsunamiInjector | Downloader of TsunamiInstaller. Additionally drops TsunamiHardener. |
| TsunamiHardener* | Known as TsunamiPayload within the code. Units up endurance for TsunamiClient, and Microsoft Defender exclusions for TsunamiClient and the XMRig miner (considered one of TsunamiClient’s parts). |
| TsunamiInstaller | .NET dropper of TsunamiClientInstaller and a Tor proxy. |
| TsunamiClientInstaller* | Fingerprints the machine; downloads and executes TsunamiClient. |
| TsunamiClient | Complicated .NET spy ware; drops XMRig and NBMiner. |
* Those parts had been at the beginning each named TsunamiPayload; we have now renamed them to steer clear of any confusion.
PostNapTea and Tropidoor
Over the process our analysis, we noticed a captivating piece of proof, additional linking DeceptiveDevelopment to North Korea. In April 2025, Ahnlab researchers reported about trojanized Bitbucket initiatives containing BeaverTail and a 64‑bit downloader named automotive.dll or img_layer_generate.dll. Whilst BeaverTail, as anticipated, downloaded InvisibleFerret, this new downloader retrieved an in-memory payload that was once named Tropidoor by way of Ahnlab. We learned that Tropidoor stocks huge parts of code with PostNapTea, a Lazarus RAT disbursed by way of exploitation towards South Korean goals in 2022. Desk 2 comprises a comparability of each payloads.
Desk 2. Comparability of Tropidoor (DeceptiveDevelopment) and PostNapTea (Lazarus) payloads (asterisks point out the rustic of a VirusTotal submission)
| Tropidoor | PostNapTea | |
| First noticed | 2024-11-28 | 2022-02-25 |
| Focused nations | Kenya*, Colombia*, Canada* | South Korea |
| Preliminary Get admission to | Social engineering | Exploitation |
| Hash-based solution of Home windows APIs | Fowler–Noll–Vo | Fowler–Noll–Vo |
| String encryption | Undeniable + XOR-based | XOR-based |
| Encryption for community conversation | Base64 + AES-128 | Base64 + AES-128 |
| Undertaking | C DLL | MFC C++ DLL |
| Form of instructions | Interior implementation of Home windows instructions | Interior implementation of Home windows instructions |
| Construction atmosphere | Visible Studio 2019, v16.11 | Visible Studio 2017, v15.9 |
| Configuration layout | Binary | JSON |
| Consumer-Agent (variations in reversed colour) | Mozilla/5.0 (Home windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/112.0.0.0 Safari/537.36 Edg/112.0.1722.64 | Mozilla/5.0 (Home windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/91.0.4472.114 Safari/537.36 |
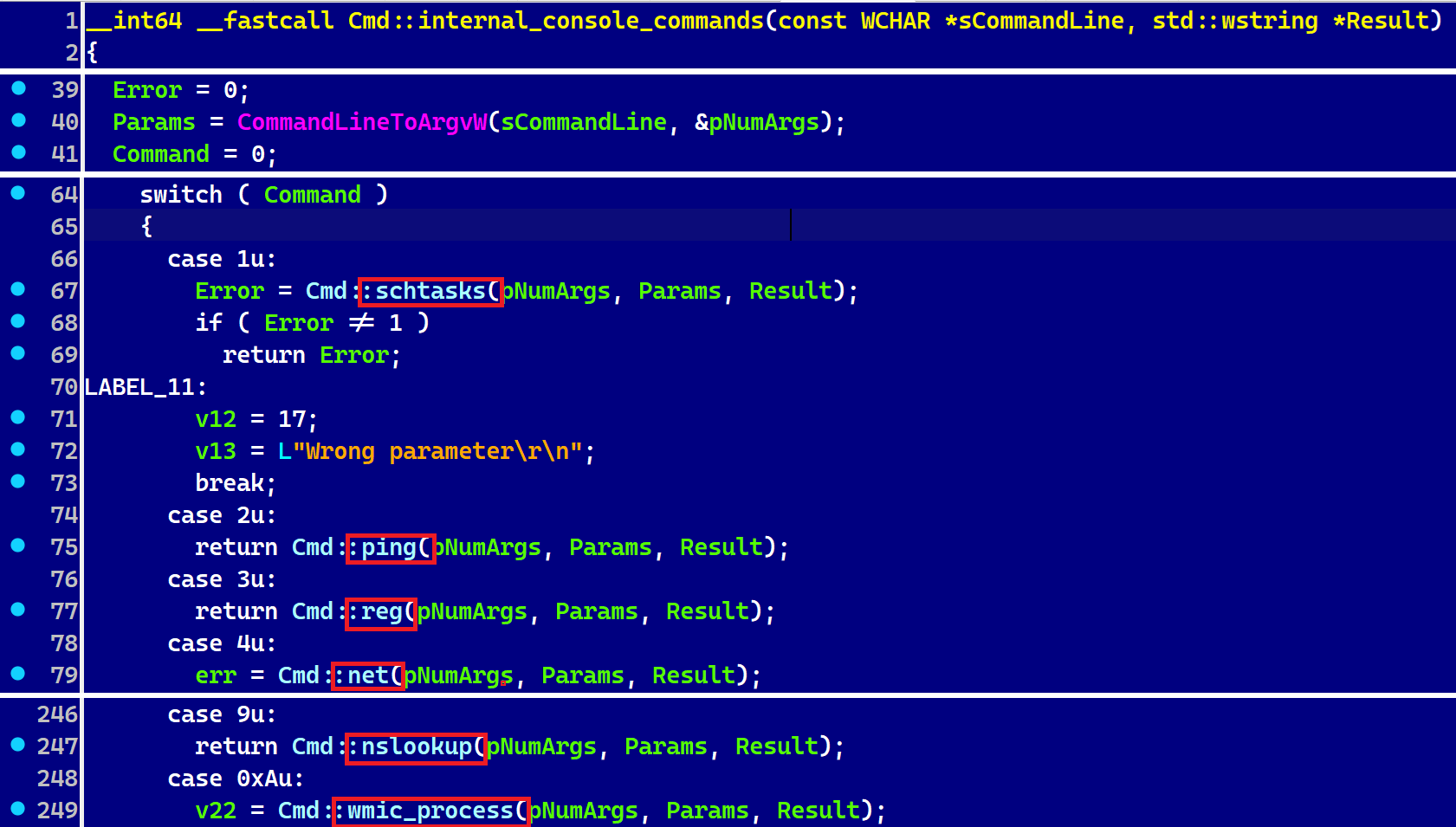
Tropidoor is essentially the most subtle payload but connected to the DeceptiveDevelopment workforce, most likely as a result of it’s in response to malware evolved by way of the extra technically complicated danger actors below the Lazarus umbrella. Probably the most supported instructions are proven in Determine 2.
New findings
Since our white paper’s submission, we have now exposed new findings that additional reinforce the hyperlink between the task of DeceptiveDevelopment and different North Korea-aligned cyberattacks.
We found out that the TsunamiKit venture dates again a minimum of to December 2021, when it was once submitted to VirusTotal below the identify Nitro Labs.zip. Some of the parts comprises the PDB trail E:ProgrammingThe Tsunami ProjectMalwareC#C# Tsunami Dist Model 3.0.0CTsunamiobjReleasenetcoreapp3.1win-x64Device Runtime Track.pdb. We conclude that TsunamiKit is most probably a amendment of a gloomy internet venture quite than a brand new introduction by way of the attackers, in response to TsunamiKit in large part predating the approximate get started of DeceptiveDevelopment task in 2023, equivalent TsunamiKit payloads with none indicators of BeaverTail having been noticed in ESET telemetry, and cryptocurrency mining being a core characteristic of TsunamiKit.
AkdoorTea
In August 2025, a BAT report named ClickFix-1.bat and a ZIP archive named nvidiaRelease.zip had been uploaded to VirusTotal. The BAT report simply downloads the archive and executes run.vbs from it. The archive comprises more than a few reputable JAR applications for the NVIDIA CUDA Toolkit, along side the next malicious information:
- shell.bat, a trojanized installer for Node.js, which is carried out later on.
- primary.js, an obfuscated BeaverTail script, robotically loaded by way of Node.js.
- drvUpdate.exe, a TCP RAT, to which we assign the codename AkdoorTea, as it’s very similar to Akdoor reported by way of AlienVault in 2018 (see Desk 3). Akdoor is a detection root identify by way of Ahnlab and generally identifies a North Korea-aligned payload.
- run.vbs, a VBScript that executes the trojanized installer and AkdoorTea.
Desk 3. Comparability of variants of AkdoorTea and Akdoor
| AkdoorTea 2025 | Akdoor 2018 | |
| Distribution identify | drvUpdate.exe | splwow32.exe, MMDx64Fx.exe |
| Encryption | Base64 + XOR with 0x49 | Base64 + RC4 |
| Selection of supported instructions | 5 | 4 |
| C&C | 103.231.75[.]101 | 176.223.112[.]74 164.132.209[.]191 |
| Model | 01.01 | 01.01 |
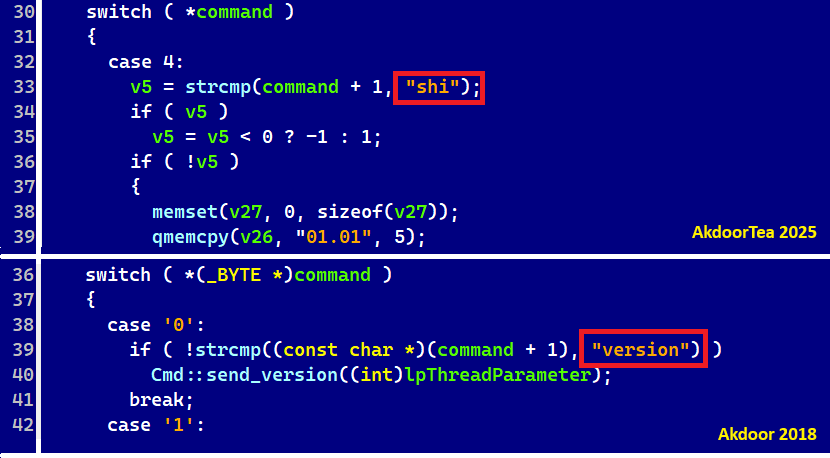
Some of the variations between AkdoorTea from 2025 and Akdoor from 2018 is the numbering of instructions; see Determine 3. Additionally, the command identify “model” is named “shi” now.
North Korean IT staff (aka WageMole)
Whilst our analysis into DeceptiveDevelopment is based mostly on records from our telemetry and reverse-engineering the gang’s toolset, it’s attention-grabbing to indicate DeceptiveDevelopment’s members of the family to fraud operations by way of North Korean IT staff, overlapping with the task of the UNC5267 and Jasper Sleet danger teams.
IT employee campaigns were ongoing since a minimum of April 2017, in line with an FBI sought after poster, and feature been increasingly more outstanding lately. A joint advisory launched in Would possibly 2022 describes IT employee campaigns as a coordinated effort by way of North Korea-aligned people to realize employment at in another country corporations, whose salaries are then used to lend a hand fund the rustic. They have got additionally been recognized to scouse borrow interior corporate records and use it to extort corporations, as mentioned in a statement by way of the FBI in January 2025.
Along with the usage of AI to accomplish their task duties, they depend closely on AI for manipulating pictures of their profile photos and CVs, or even carry out face swaps in real-time video interviews to appear to be the personality they’re these days the usage of, as described in additional element in a blogpost by way of Unit 42 in April 2025.
A methodological perception was once supplied by way of a DTEX record in Would possibly 2025. The IT staff reportedly function in a scattered method, with a large number of groups of staff, generally founded in overseas nations like China, Russia, and nations in Southeast Asia. Each and every crew works in a relatively other method, however their finish targets and modus operandi are the similar – posing as overseas faraway staff with faux paperwork and CVs, and in search of faraway employment or freelance paintings to assemble finances from the salaries.
Inspecting OSINT records
More than one researchers have noticed ties and circumstances of data alternate between those IT staff and DeceptiveDevelopment. In August 2024, the cybersecurity researcher Heiner García printed an investigation of ways each teams percentage e-mail accounts or are mutually adopted between the GitHub profiles of faux recruiters and IT staff. In November 2024, Zscaler showed that identities stolen from compromised sufferers are utilized by scammers to protected faraway jobs. This leads us to say with medium self belief that even supposing those actions are performed by way of two other teams, they’re possibly attached and participating.
Moreover, we controlled to assemble publicly to be had records detailing the internal workings of one of the crucial IT employee groups. We amassed this data from more than one resources (with vital lend a hand from @browsercookies on X), amongst them GitHub profiles belonging to the IT staff, containing publicly obtainable interior records and content material shared publicly by way of researchers. Those come with main points in their paintings assignments, schedules, conversation with purchasers and every different, emails, more than a few photos used for on-line profiles (each genuine and faux), faux CVs, and textual content templates used when task looking; because of news sharing agreements, we don’t seem to be disclosing the particular resources of the information utilized in our research. We dive into those main points in our white paper, and supply a compact abstract under.
Research of faux CVs and interior fabrics displays that IT staff to begin with centered jobs in the USA, however have lately shifted center of attention to Europe, together with France, Poland, Ukraine, and Albania.
Each and every crew is led by way of a “boss” who units quotas and coordinates paintings. Individuals spend 10–16 hours day-to-day obtaining jobs, finishing duties, and self-educating – basically in internet programming, blockchain, English, and AI integration.
They meticulously observe their paintings and use faux identities, CVs, and portfolios to use for jobs. Conversation with employers follows scripted responses to look certified.
Moreover, they use premade scripts to recruit genuine folks as proxies, providing them a percentage of the wage to wait interviews or host paintings gadgets in much less suspicious nations. In a single case, Ukrainian builders had been centered because of perceived hiring benefits.
Conclusion
DeceptiveDevelopment’s TTPs illustrate a extra disbursed, volume-driven fashion of its operations. Regardless of frequently missing technical sophistication, the gang compensates thru scale and artistic social engineering. Its campaigns exhibit a realistic method, exploiting open-source tooling, reusing to be had darkish internet initiatives, adapting malware most likely rented from different North Korea-aligned teams, and leveraging human vulnerabilities thru faux task provides and interview platforms.
The actions of North Korean IT staff represent a hybrid danger. This fraud-for-hire scheme combines classical legal operations, reminiscent of id robbery and artificial id fraud, with virtual gear, which classify it as each a conventional crime and a cybercrime (or eCrime). Proxy interviewing poses a critical chance to employers, since an illegitimate worker employed from a sanctioned nation won’t best be irresponsible or underperforming, however may just additionally evolve into a perilous insider danger.
Our findings additionally spotlight the blurred traces between centered APT task and cybercrime, in particular within the overlap between malware campaigns by way of DeceptiveDevelopment and the operations of North Korean IT staff. Those dual-use ways – combining cybertheft and cyberespionage with non-cyberspace employment-fraud schemes – underscore the will for defenders to believe broader danger ecosystems quite than remoted campaigns..
For any inquiries about our analysis printed on WeLiveSecurity, please touch us at threatintel@eset.com.ESET Analysis provides non-public APT intelligence experiences and knowledge feeds. For any inquiries about this carrier, discuss with the ESET Risk Intelligence web page.
IoCs
Information
A complete checklist of signs of compromise (IoCs) and samples may also be present in our GitHub repository.
| SHA-1 | Filename | Detection | Description |
| E34A43ACEF5AF1E5197D |
nvidiadrivers |
WinGo/DeceptiveDeve |
A trojanized venture containing WeaselStore. |
| 3405469811BAE511E62C |
VCam1.replace | WinGo/DeceptiveDeve |
A trojanized venture containing WeaselStore. |
| C0BAA450C5F3B6AACDE2 |
VCam2.replace | WinGo/DeceptiveDeve |
A trojanized venture containing WeaselStore. |
| DAFB44DA364926BDAFC7 |
nvidia.js | JS/Undercover agent.DeceptiveDeve |
WeaselStore downloader for Home windows. |
| 015583535D2C8AB710D1 |
ffmpeg.sh | OSX/DeceptiveDeve |
WeaselStore downloader for OSX/Linux. |
| CDA0F15C9430B6E0FF1A |
DriverMinUpdate | OSX/DeceptiveDeve |
Pretend steered soliciting for consumer’s login on macOS. |
| 214F0B10E9474F0F5D32 |
nvidiaupdate |
WinGo/DeceptiveDeve |
Compiled WeaselStore binary for Home windows. |
| 4499C80DDA6DBB492F86 |
bow | Python/DeceptiveDeve |
InvisibleFerret. |
| B20BFBAB8BA732D428AF |
N/A | Python/DeceptiveDeve |
Browser-data stealer module of InvisibleFerret. |
| C6888FB1DE8423D9AEF9 |
Home windows Replace |
Python/TsunamiKit.A | TsunamiInjector. |
| 4AAF0473599D7E3A5038 |
Runtime Dealer |
MSIL/DeceptiveDeve |
TsunamiInstaller. |
| 251CF5F4A8E73F8C5F91 |
Tsunami Payload |
MSIL/DeceptiveDeve |
TsunamiClientInstaller. |
| D469D1BAA3417080DED7 |
Tsunami Payload |
MSIL/DeceptiveDeve |
TsunamiClient. |
| 0C0F8152F3462B662318 |
Runtime Dealer |
Win64/Riskware.Tor.A | Tor Proxy. |
| F42CC34C1CFAA826B962 |
autopart.zip |
Win64/DeceptiveDeve JS/Undercover agent.DeceptiveDeve |
A trojanized venture containing BeaverTail and a downloader of Tropidoor. |
| 02A2CD54948BC0E2F696 |
hoodygang.zip |
Win64/DDeceptiveDeve JS/Undercover agent.DeceptiveDeve |
A trojanized venture containing BeaverTail and a downloader of Tropidoor. |
| 6E787E129215AC153F3A |
tailwind.con |
JS/Undercover agent.DeceptiveDeve |
A trojanized JavaScript containing BeaverTail. |
| FE786EAC26B61743560A |
tailwind.con |
JS/Undercover agent.DeceptiveDeve |
A trojanized JavaScript containing BeaverTail. |
| 86784A31A2709932FF10 |
img_layer_gen |
Win64/DeceptiveDeve |
A downloader of the Tropidoor RAT. |
| 90378EBD8DB757100A83 |
N/A | Win64/DeceptiveDeve |
Tropidoor RAT. |
| C86EEDF02B73ADCE0816 |
drivfixer.sh | OSX/DeceptiveDeve |
A trojanized macOS installer and launcher of Node.js. |
| 4E4D31C559CA16F8B7D4 |
ClickFix-1 |
PowerShell/Decepti |
An preliminary degree on Home windows: BAT downloading a malicious nvidiaRelease.zip archive. |
| A9C94486161C07AE6935 |
driv.zip |
JS/Undercover agent.DeceptiveDeve OSX/DeceptiveDeve |
A ZIP archive containing BeaverTail. |
| F01932343D7F13FF1094 |
nvidiaRelease |
JS/Undercover agent.DeceptiveDeve Win32/DeceptiveDeve VBS/DeceptiveDeve BAT/DeceptiveDeve |
A ZIP archive containing BeaverTail and AkdoorTea. |
| BD63D5B0E4F2C72CCFBF |
mac-v-j1722 |
OSX/DeceptiveDeve |
An preliminary degree on macOS: a bash script that downloads a malicious driv.zip archive. |
| 10C967386460027E7492 |
primary.js | JS/Undercover agent.DeceptiveDeve |
An obfuscated BeaverTail script, robotically loaded by way of Node.js. |
| 59BA52C644370B4D627F |
run.vbs | VBS/DeceptiveDeve |
A VBScript that executes AkdoorTea and shell.bat. |
| 792AFE735D6D356FD30D |
drvUpdate.exe | Win32/DeceptiveDeve |
AkdoorTea, a TCP RAT. |
Community
| IP | Area | Web hosting supplier | First noticed | Main points |
| 199.188.200[.]147 | driverservice |
Namecheap, Inc. | 2025‑08‑08 | Far flung garage for DeceptiveDevelopment. |
| 116.125.126[.]38 | www.royalsevr |
SK Broadband Co Ltd | 2024‑06‑25 | Far flung garage for DeceptiveDevelopment. |
| N/A | n34kr3z26f3jz |
N/A | 2023‑10‑06 | TsunamiClient C&C server. |
| 103.231.75[.]101 | N/A | THE-HOSTING-MNT | 2025‑08‑10 | AkdoorTea C&C server. |
| 45.159.248[.]110 | N/A | THE-HOSTING-MNT | 2025‑06‑29 | BeaverTail C&C server. |
| 45.8.146[.]93 | N/A | STARK INDUSTRIES SOLUTIONS LTD | 2024‑10‑26 | Tropidoor C&C server. |
| 86.104.72[.]247 | N/A | STARK INDUSTRIES SOLUTIONS LTD | 2024‑10‑31 | Tropidoor C&C server. |
| 103.35.190[.]170 | N/A | STARK INDUSTRIES SOLUTIONS LTD | 2024‑06‑24 | Tropidoor C&C server. |
MITRE ATT&CK tactics
This desk was once constructed the usage of model 17 of the MITRE ATT&CK framework.
| Tactic | ID | Identify | Description |
| Reconnaissance | T1589 | Acquire Sufferer Identification Data | DeceptiveDevelopment steals sufferers’ credentials for use by way of WageMole in consequent social engineering. |
| Useful resource Construction | T1585.001 | Determine Accounts: Social Media Accounts | Pretend recruiter accounts created on LinkedIn, Upwork, Freelancer.com, and so on. |
| T1586 | Compromise Accounts | Hijacked GitHub and social media accounts used to distribute malware. | |
| Preliminary Get admission to | T1566.001 | Phishing: Spearphishing Attachment | Pretend task provides come with attachments or hyperlinks to malicious initiatives. |
| T1566.002 | Phishing: Spearphishing Hyperlink | ClickFix methodology makes use of misleading hyperlinks to faux troubleshooting guides. | |
| Execution | T1204.001 | Consumer Execution: Malicious Hyperlink | Sufferers are lured to faux task interview websites (e.g., ClickFix) that start up malware obtain. |
| T1204.002 | Consumer Execution: Malicious Document | Trojanized coding demanding situations include variants of BeaverTail. | |
| T1059 | Command and Scripting Interpreter | DeceptiveDevelopment makes use of VBS, Python, JavaScript, and shell instructions for execution. | |
| Protection Evasion | T1078 | Legitimate Accounts | WageMole reuses stolen identities and credentials, particularly for faux recruiter and GitHub accounts. |
| T1027 | Obfuscated Information or Data | Obfuscated malicious scripts are hidden in lengthy feedback or out of doors IDE view. | |
| T1055 | Procedure Injection | TsunamiKit makes use of injection tactics in its execution chain. | |
| T1036 | Masquerading | Malware disguised as reputable device (e.g., conferencing gear, NVIDIA installers). | |
| T1497 | Virtualization/Sandbox Evasion | TsunamiKit contains atmosphere exams and obfuscation to evade research. | |
| Assortment | T1056.001 | Enter Seize: Keylogging | InvisibleFerret contains clipboard and keylogging modules. |
| Command and Regulate | T1071.001 | Utility Layer Protocol: Internet Protocols | AkdoorTea, BeaverTail, and Tropidoor keep in touch with C&C servers over HTTP/S. |
| T1105 | Ingress Software Switch | BeaverTail downloads second-stage payloads like InvisibleFerret, TsunamiKit, or Tropidoor. |