An outline of the actions of decided on APT teams investigated and analyzed by means of ESET Analysis in Q2 2025 and Q3 2025
06 Nov 2025
•
,
4 min. learn

ESET APT Job Document Q2 2025–Q3 2025 summarizes notable actions of decided on complex power danger (APT) teams that have been documented by means of ESET researchers from April thru September 2025. The highlighted operations are consultant of the wider panorama of threats we investigated right through this era. They illustrate the important thing traits and tendencies and include just a small fraction of the cybersecurity intelligence information supplied to consumers of ESET APT experiences.
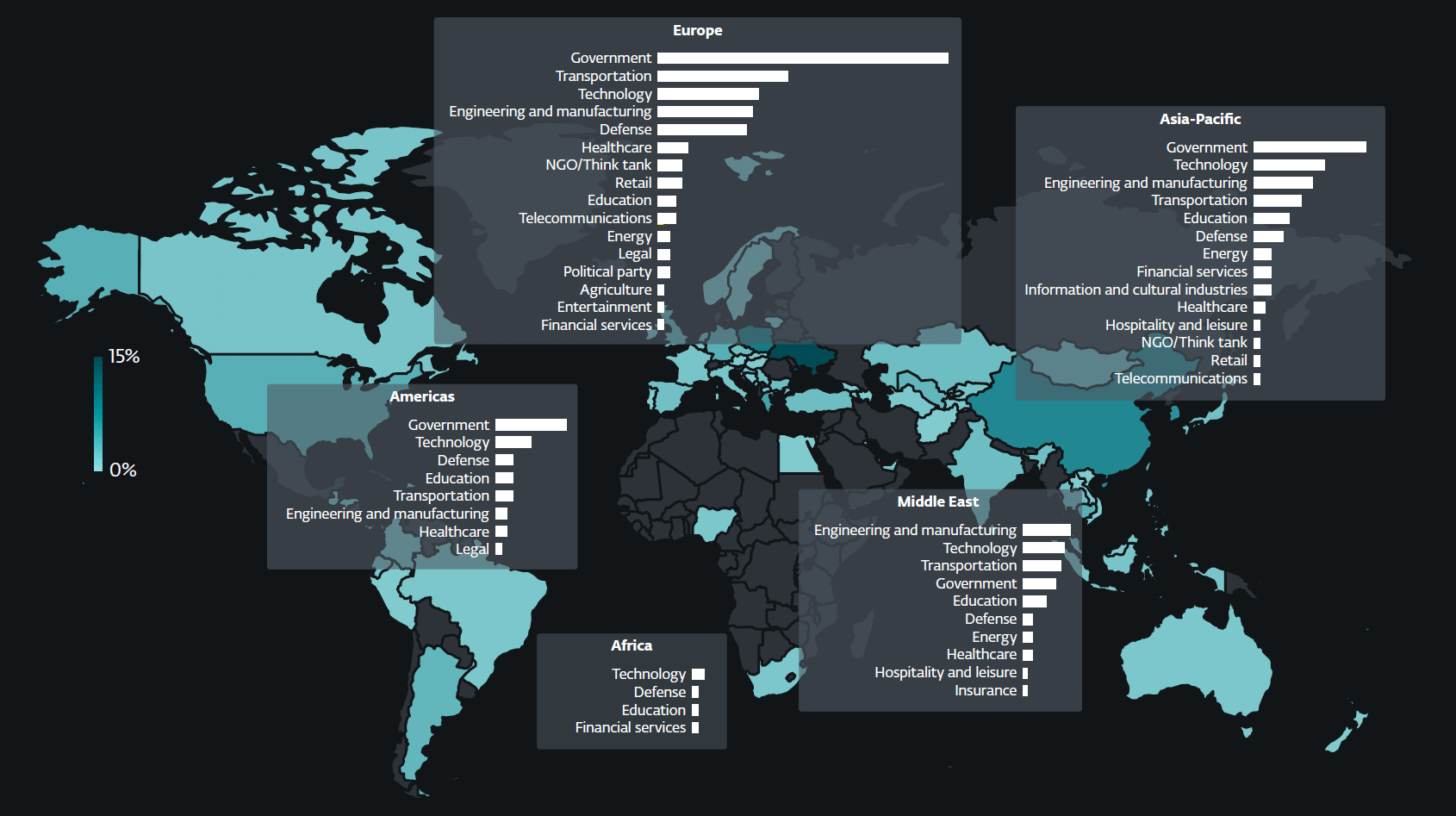
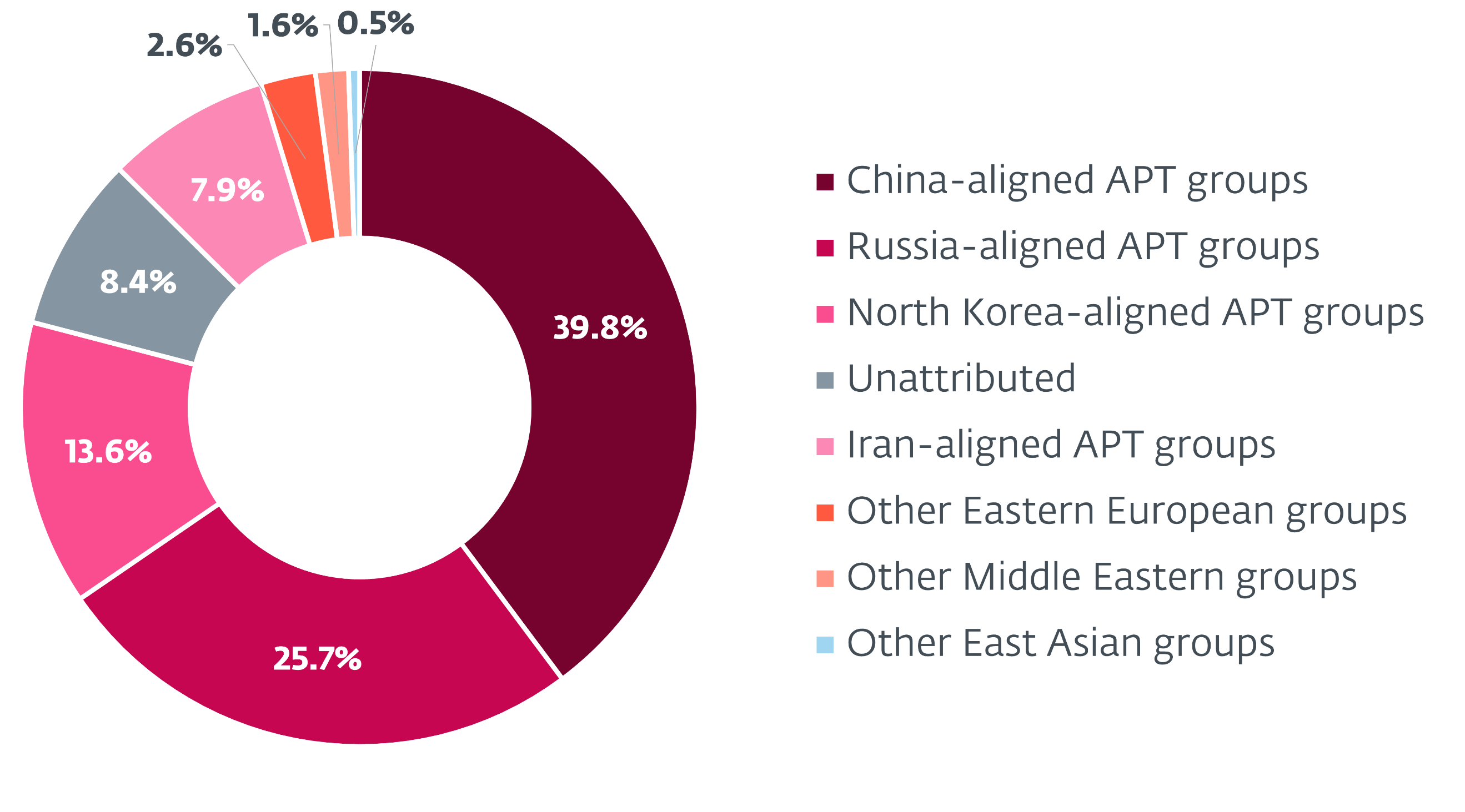
All the way through the monitored length, China-aligned APT teams persisted to advance Beijing’s geopolitical targets. We noticed an expanding use of the adversary-in-the-middle method for each preliminary get admission to and lateral motion, hired by means of teams reminiscent of PlushDaemon, SinisterEye, Evasive Panda, and TheWizards. In what seems to be a reaction to the Trump management’s strategic hobby in Latin The us, and perhaps additionally influenced by means of the continuing US‑China energy fight, FamousSparrow launched into a excursion of Latin The us, concentrated on more than one governmental entities within the area. Mustang Panda remained extremely energetic in Southeast Asia, the US, and Europe, that specialize in the governmental, engineering, and maritime shipping sectors. Flax Storm centered the healthcare sector in Taiwan by means of exploiting public-facing internet servers and deploying webshells to compromise its sufferers. The gang ceaselessly maintains its SoftEther VPN infrastructure, and it additionally began the use of an open-source proxy, BUUT. In the meantime, Speccom centered the power sector in Central Asia with the presumed intention of gaining larger visibility into Chinese language-funded operations and decreasing China’s dependency on maritime imports. One of the crucial backdoors within the team’s toolset, BLOODALCHEMY, seems to be preferred by means of a number of China-aligned danger actors.
We noticed a persisted building up in spearphishing actions of the Iran-aligned MuddyWater. The gang followed the method of sending spearphishing emails internally – from compromised inboxes throughout the goal group – with a particularly top luck price. Different Iran-aligned teams remained energetic: BladedFeline followed new infrastructure, whilst GalaxyGato deployed an advanced C5 backdoor. GalaxyGato additionally presented a fascinating twist to its marketing campaign by means of leveraging DLL-search-order hijacking to thieve credentials.
North Korea-aligned danger actors centered the cryptocurrency sector and, particularly, expanded their operations to Uzbekistan – a rustic no longer up to now noticed of their scope. In fresh months, now we have documented a number of new campaigns performed by means of DeceptiveDevelopment, Lazarus, Kimsuky, and Konni, with the purpose of espionage, advancing Pyongyang’s geopolitical priorities, and producing income for the regime. Kimsuky experimented with the ClickFix option to goal diplomatic entities, and South Korean suppose tanks and academia, whilst Konni used social engineering with an bizarre focal point on macOS programs.
Russia-aligned teams maintained their focal point on Ukraine and international locations with strategic ties to Ukraine, whilst additionally increasing their operations to Ecu entities. Spearphishing remained their number one means of compromise. Significantly, RomCom exploited a zero-day vulnerability in WinRAR to deploy malicious DLLs and ship a number of backdoors. We reported this vulnerability to WinRAR, which promptly patched it. The gang’s task was once most commonly targeted at the monetary, production, protection, and logistics sectors within the EU and Canada. Gamaredon remained probably the most energetic APT team concentrated on Ukraine, with a noticeable building up in depth and frequency of its operations. This surge in task coincided with a unprecedented example of cooperation between Russia-aligned APT teams, as Gamaredon selectively deployed one in all Turla’s backdoors. Gamaredon’s toolset, perhaps additionally spurred by means of the collaboration, persisted to conform, for instance, throughout the incorporation of latest report stealers or tunneling products and services.
Sandworm, very similar to Gamaredon, concerned with Ukraine – albeit with motives of destruction slightly than cyberespionage. The gang deployed information wipers (ZEROLOT, Sting) in opposition to governmental entities, corporations within the power and logistics sectors, and, extra particularly, in opposition to the grain sector – the most likely function being the weakening of the Ukrainian financial system. Some other Russia-aligned danger actor, InedibleOchotense, performed a spearphishing marketing campaign impersonating ESET. This marketing campaign concerned emails and Sign messages handing over a trojanized ESET installer that results in the obtain of a valid ESET product at the side of the Kalambur backdoor.
After all, notable actions by means of lesser-known teams integrated FrostyNeighbor exploiting an XSS vulnerability in Roundcube. Polish and Lithuanian corporations have been centered by means of spearphishing emails that impersonated Polish companies. The emails contained a particular use and mixture of bullet issues and emojis, a construction harking back to AI-generated content material, suggesting conceivable use of AI within the marketing campaign. Delivered payloads integrated a credential stealer and an electronic mail message stealer. We additionally known a up to now unknown Android spy ware circle of relatives in Iraq, which we named Wibag. Masquerading because the YouTube app, Wibag goals messaging platforms reminiscent of Telegram and WhatsApp, in addition to Instagram, Fb, and Snapchat. Its functions come with keylogging and the exfiltration of SMS messages, name logs, location information, contacts, display recordings, and recordings of WhatsApp calls and common telephone calls. Apparently, the login web page for the spy ware’s admin panel presentations the brand of the Iraqi Nationwide Safety Provider.
Malicious actions described in ESET APT Job Document Q2 2025–Q3 2025 are detected by means of ESET merchandise; shared intelligence is primarily based on proprietary ESET telemetry information and has been verified by means of ESET researchers.
ESET APT Job Studies include just a fraction of the cybersecurity intelligence information supplied in ESET Danger Intelligence APT Studies. For more info, discuss with the ESET Danger Intelligence site.




