
A brand new disclosed cPanel flaw tracked as CVE-2026-41940 is being mass-exploited to breach web sites and encrypt information in “Sorry” ransomware assaults.
This week, an emergency replace for WHM and cPanel was once launched to mend a crucial authentication bypass flaw that permits attackers to get admission to regulate panels.
WHM and cPanel are Linux-based internet webhosting regulate panels for server and website online control. Whilst WHM supplies server-level regulate, cPanel supplies administrator get admission to to the website online backend, webmail, and databases.
Quickly after its liberate, it was once reported that the flaw was once being actively exploited within the wild as a zero-day, with exploitation makes an attempt courting again to past due February.
Web safety watchdog Shadowserver now reviews that no less than 44,000 IP addresses working cPanel have since been compromised in ongoing assaults.
cPanel flaw exploited for Sorry ransomware assaults
A lot of resources instructed BleepingComputer that hackers had been exploiting the cPanel flaw since Thursday to breach servers and deploy a Move-based Linux encryptor for the “Sorry” ransomware [VirusTotal].
There were a large number of reviews of web sites impacted by means of the assaults, together with at the BleepingComputer boards, the place a sufferer shared samples of the encrypted information and the contents of the ransom word.
Since then, fashionable exploitation and ransomware assaults had been noticed, with loads of compromised websites already listed in Google.
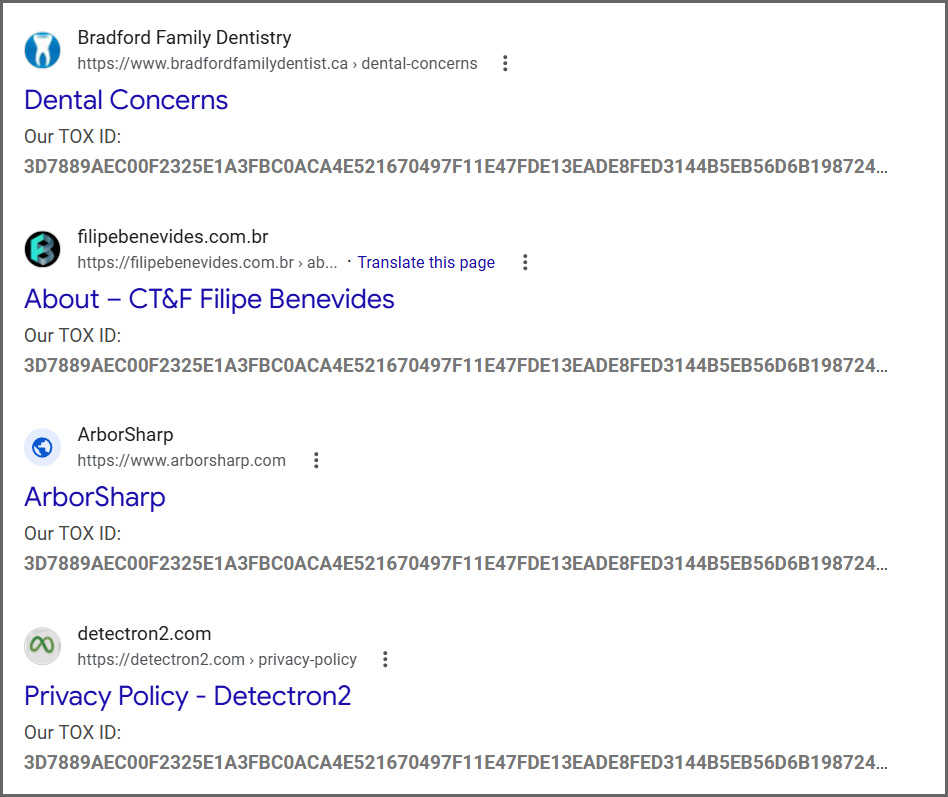
Supply: BleepingComputer
The Sorry ransomware encryptor is designed in particular for Linux and can append the “.sorry” extension to all encrypted information.
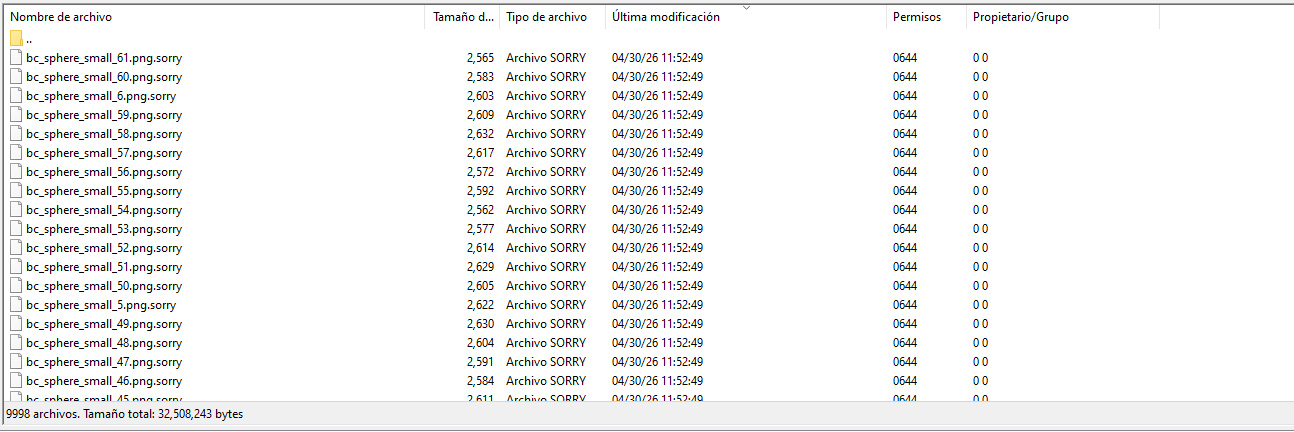
Supply: diozada at the BleepingComputer boards
BleepingComputer was once instructed that the ransomware makes use of the ChaCha20 circulation cipher to encrypt information, with the encryption key secure the usage of an embedded RSA-2048 public key.
Ransomware skilled Rivitna says the one technique to decrypt those information is to procure the corresponding personal RSA-2048 key.
“Decryption is not possible with out an RSA-2048 personal key,” Rivitna posted to our boards.
In every folder, a ransom word named README.md is created, teaching the sufferer to touch the danger actor on Tox to barter a ransom fee.
The ransom word is identical for every sufferer of this ransomware marketing campaign, together with the Tox ID “3D7889AEC00F2325E1A3FBC0ACA4E521670497F11E47FDE13EADE8FED3144B5EB56D6B198724,” which is used to touch the danger actor.
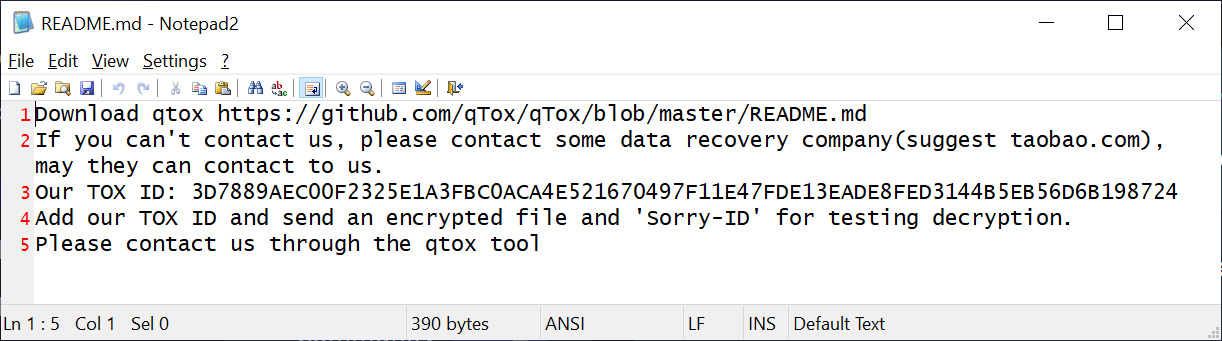
Supply: BleepingComputer
It must be famous {that a} 2018 ransomware campaign applied a HiddenTear encryptor to encrypt information and append the .sorry extension. This present marketing campaign makes use of a unique encryptor and is unrelated.
All cPanel and WHM customers are steered to instantly set up the to be had safety updates to give protection to their web sites from ransomware assaults and information robbery.
The assaults have simply began, and we can most probably see higher exploitation over the approaching days and weeks.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Self reliant Validation Summit (Might 12 & 14), see how independent, context-rich validation unearths what is exploitable, proves controls grasp, and closes the remediation loop.
Declare Your Spot



