Growth Device warned shoppers to patch a vital authentication bypass vulnerability in its MOVEit Automation enterprise-grade controlled document switch (MFT) utility.
MOVEit Automation automates advanced information workflows with out requiring handbook scripting and serves as a central automation orchestrator to agenda and organize document transfers between other programs, together with native servers, cloud garage, and exterior companions.
Tracked as CVE-2026-4670, the protection flaw impacts MOVEit Automation variations ahead of 2025.1.5, 2025.0.9, and 2024.1.8. Far off risk actors can exploit it with out privileges at the focused programs in low-complexity assaults that do not require consumer interplay.
“We’ve got addressed the vulnerability and the Growth MOVEit Automation group strongly recommends acting an improve to the most recent model,” the corporate says in a Thursday advisory. “Upgrading to a patched unencumber, the usage of the total installer, is the one technique to remediate this factor. There shall be an outage to the machine whilst the improve is working.”
The similar day, Growth additionally launched safety updates to deal with a high-severity privilege escalation vulnerability (CVE-2026-5174) stemming from an unsuitable enter validation weak point in the similar tool.
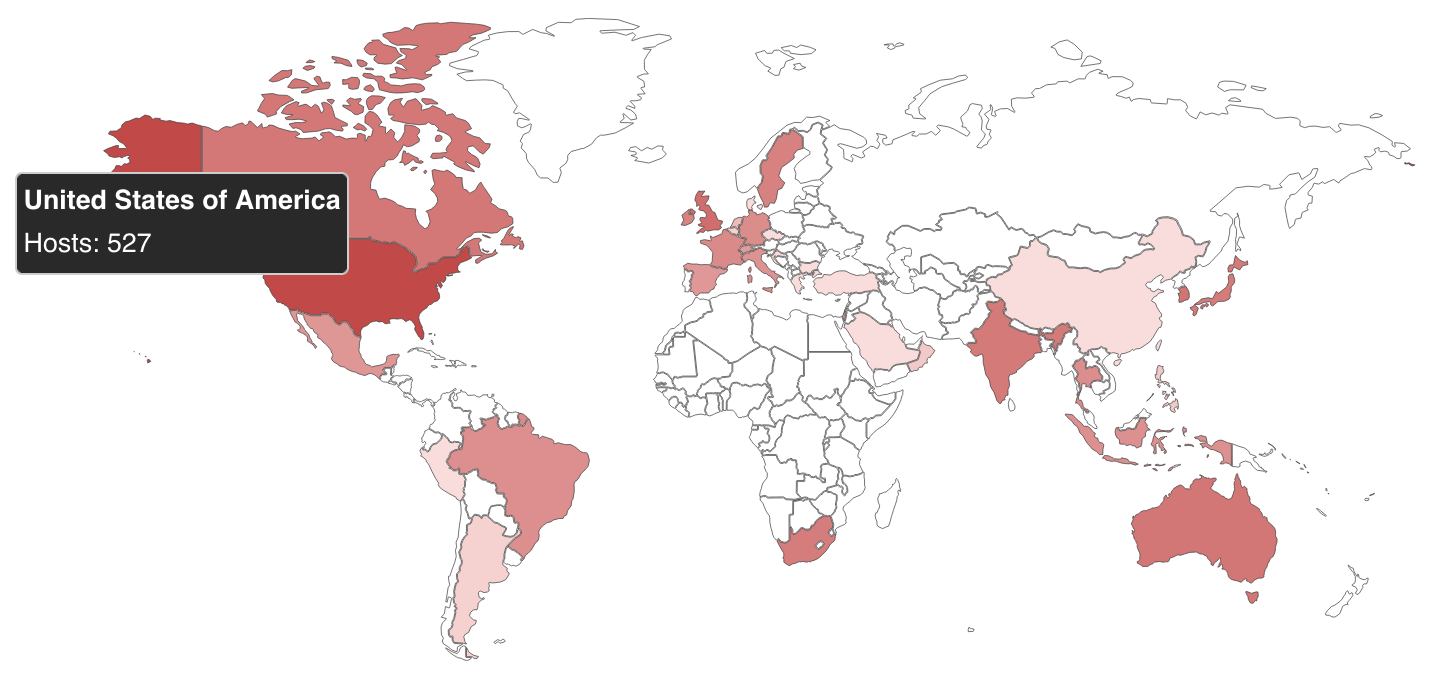
In keeping with a Shodan seek shared via PwnDefend cybersecurity consultant Daniel Card, over 1,400 MOVEit Automation circumstances are uncovered on-line, and over a dozen are related to U.S. native and state govt companies.
Alternatively, there’s no data referring to what number of of those programs have already been secured towards CVE-2026-4670 assaults.
Whilst the corporate has but to flag those safety problems as exploited within the wild, different MoveIT MFT vulnerabilities had been focused in assaults lately.
For example, the Clop ransomware gang exploited a zero-day within the MOVEit Switch safe document switch platform in an in depth collection of knowledge robbery assaults in 2023 that affected greater than 2,100 organizations and over 62 million people, in step with Emsisoft estimates.
MFT tool is a beautiful goal for ransomware actors, as observed in earlier Clop data-theft campaigns focused on safety flaws in Accellion FTA, SolarWinds Serv-U, Gladinet CentreStack, GoAnywhere MFT, and Cleo.
Growth Device says its MOVEit MFT answers are utilized by greater than 3,000 venture organizations and over 100,000 customers international.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Independent Validation Summit (Might 12 & 14), see how self sustaining, context-rich validation reveals what is exploitable, proves controls cling, and closes the remediation loop.
Declare Your Spot



