When each and every minute counts, preparation and precision can imply the adaptation between disruption and crisis
03 Nov 2025
•
,
5 min. learn

Community defenders are feeling the warmth. The choice of information breaches Verizon investigated ultimate 12 months, as a proportion of total incidents, used to be up 20 proportion issues at the earlier 12 months. This needn’t be as catastrophic because it sounds, so long as groups are ready to reply unexpectedly and decisively to intrusions. However the ones first mins and hours are essential.
Preparation is the important thing to efficient incident reaction (IR). Even supposing each and every group (and incident) is other, you don’t wish to be making stuff up at the fly as soon as the alarm bells have begun ringing. If everybody within the incident reaction staff is aware of precisely what to do, there’s extra likelihood of a swift, adequate and low cost solution.
The will for pace
As soon as danger actors get within your community, the clock is ticking. Whether or not they’re after delicate information to thieve and ransom, or wish to deploy ransomware or different malicious payloads, the hot button is to forestall them ahead of they’re ready to succeed in your crown jewels. That is turning into tougher.
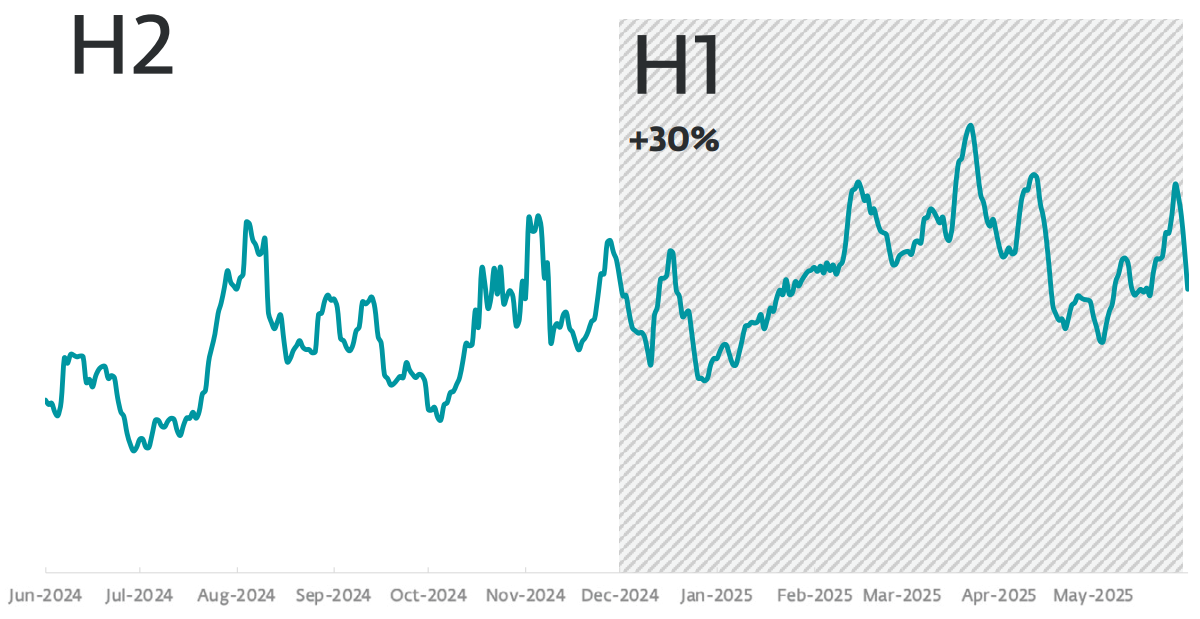
The newest analysis claims that adversaries improved from preliminary get admission to to lateral motion (aka “breakout time”) 22% quicker in 2024 than the former 12 months. The typical breakout time used to be 48 mins, even though the quickest recorded assault used to be virtually part that: simply 27 mins. May you reply to a safety breach in beneath part an hour?
In the meantime, the typical time it takes international organizations to stumble on and include a breach is 241 days, in step with IBM. There’s a significant monetary incentive for buying IR proper. Breaches with a lifecycle beneath 200 days noticed prices drop through round 5% this 12 months to US$3.9 million, whilst the ones over 200 days value over US$5 million, the file claims.
5 steps to take following a breach
No group is 100% breach-proof. In the event you endure an incident and suspect unauthorized get admission to, paintings all of a sudden, but in addition methodically. Those 5 steps can assist information your first 24 to 48 hours. Remember too that a few of these steps must occur similtaneously. The focal point must be on pace but in addition thoroughness, with out compromising accuracy or proof.
1. Accumulate knowledge and perceive scope
Step one is to grasp precisely what simply took place and got to work on a reaction. That implies activating your pre-built IR plan and notifying the staff. This workforce must come with stakeholders from around the industry, together with HR, PR and communications, prison and government management. All of them have the most important section to play post-incident.
Subsequent, figure out the blast radius of the assault:
- How did your adversary get within the company community?
- Which techniques were compromised?
- What malicious movements have attackers accomplished already?
You’ll want to record each and every step and accumulate proof no longer simply to evaluate the have an effect on of the assault, but in addition for forensic investigation, and perhaps prison functions. Keeping up chain of custody guarantees credibility if legislation enforcement or courts want to be concerned.
2. Notify related 3rd events
While you’ve established what has took place, it can be crucial to tell the related government.
- Regulators: If individually identifiable knowledge (PII) has been stolen, touch related government beneath information coverage or sector-specific rules. Within the U.S., this will likely come with notification beneath SEC cybersecurity disclosure laws or state-level breach rules.
- Insurers: Maximum insurance coverage insurance policies will stipulate that your insurance coverage supplier is knowledgeable once there was a breach.
- Consumers, companions and workers: Transparency builds agree with and is helping save you incorrect information. It’s higher that they don’t in finding out what took place from social media or the TV information.
- Regulation enforcement: Reporting incidents, particularly ransomware, can assist determine greater campaigns and every now and then yield decryption equipment or intelligence strengthen.
- Exterior mavens: Exterior prison and IT experts might also want to be contacted, particularly should you don’t have this sort of useful resource to be had in space.
3. Isolate and include
Whilst outreach to related 3rd events is ongoing, you’ll want to paintings rapid to forestall the unfold of the assault. Isolate impacted techniques from the web, however don’t flip off gadgets should you break proof. In different phrases, the objective is to restrict the attacker’s achieve with out destroying precious proof.
Any backups must be offline and disconnected so your attackers can’t hijack them and ransomware can’t corrupt them. All far off get admission to must be disabled, VPN credentials reset, and safety equipment used to dam any incoming malicious site visitors and command-and-control connections.
4. Take away and get better
As soon as containment is in position, transition to eradication and restoration. Habits forensic research to grasp your attacker’s techniques, ways and procedures (TTPs), from preliminary access to lateral motion and (if related) information encryption or exfiltration. Take away any lingering malware, backdoors, rogue accounts and different indicators of compromise.
Now it’s time to get better and repair. Key movements come with:
- disposing of malware and unauthorized accounts.
- verifying the integrity of essential techniques and knowledge
- restoring blank backups (after confirming they’re no longer compromised).
- tracking carefully for indicators of re-compromise or endurance mechanisms.
Use the restoration segment to harden techniques, no longer simply rebuild them. That can surround tightening privilege controls, imposing more potent authentication, and imposing community segmentation. Enlist the assistance of companions to boost up recovery or imagine equipment like ESET’s Ransomware Remediation to hurry up the method.
5. Evaluation and toughen
As soon as the speedy risk has handed, your paintings is a long way from over. Paintings thru your responsibilities to regulators, shoppers and different stakeholders (e.g., companions and providers). Up to date communications can be important as soon as you realize the level of the breach, probably together with a regulatory submitting. Your PR and prison advisors must be taking the lead right here.
A post-incident overview is helping turn out to be a painful tournament right into a catalyst for resilience. As soon as the mud has settled, it’s additionally a good suggestion to figure out what took place and what courses can also be discovered as a way to save you a identical incident going on one day. Read about what went fallacious, what labored, and the place detection or verbal exchange lagged. Replace your IR plan, playbooks, and escalation procedures accordingly. Any tweaks to the IR plan, or suggestions for brand new safety controls and worker coaching pointers, can be helpful.
A robust post-incident tradition treats each and every breach as a coaching workout for the following one, bettering defenses and decision-making beneath rigidity.
Past IT
It is not at all times imaginable to forestall a breach, however it’s imaginable to attenuate the wear. If your company doesn’t have the sources to watch for threats 24/7, imagine a controlled detection and reaction (MDR) carrier from a relied on 3rd birthday celebration. No matter occurs, take a look at your IR plan, after which take a look at it once more. As a result of a hit incident reaction isn’t only a topic for IT. It calls for various stakeholders from around the group and externally to paintings in combination in solidarity. The type of muscle reminiscence you all want generally calls for quite a lot of follow to broaden.