In case your knowledge is at the darkish internet, it’s most definitely just a topic of time earlier than it’s abused for fraud or account hijacking. Right here’s what to do.
13 Jan 2026
•
,
6 min. learn

Opposite to widespread trust, a lot of the darkish internet isn’t the den of virtual iniquity that some commentators declare. In reality, there are many valid websites and boards there providing privacy-enhanced content material and services and products to lend a hand folks keep away from censorship and oppression. On the other hand, actually, it’s additionally a magnet for cybercriminals, who can discuss with its boards, marketplaces and different websites with out worry of being tracked and unmasked.
Many of those exist to facilitate the business in stolen private and monetary knowledge. Incessantly, private knowledge is purchased and offered along different pieces like narcotics, hacking equipment and exploits. So what will have to you do in case you in finding out your knowledge is up on the market on any such websites?
How did my knowledge get there?
There are more than a few tactics for my part identifiable knowledge (PII), credentials and monetary knowledge can finally end up within the palms of cybercriminals:
- Knowledge breaches contain the large-scale robbery of purchaser/worker knowledge, which then normally seems on the market at the darkish internet. America used to be not off course for a report yr on this space, having already recorded 1,732 incidents within the first part of 2025, resulting in over 165.7 million breach notifications. All of us do trade with such a lot of organizations on-line this present day, the chance of being stuck up in a breach is rising at all times. Maximum people may have skilled a minimum of one notification electronic mail in our lives. That chance additionally will increase due to the proliferation of double extortion ransomware assaults, the place knowledge is stolen to be able to extort a sufferer group.
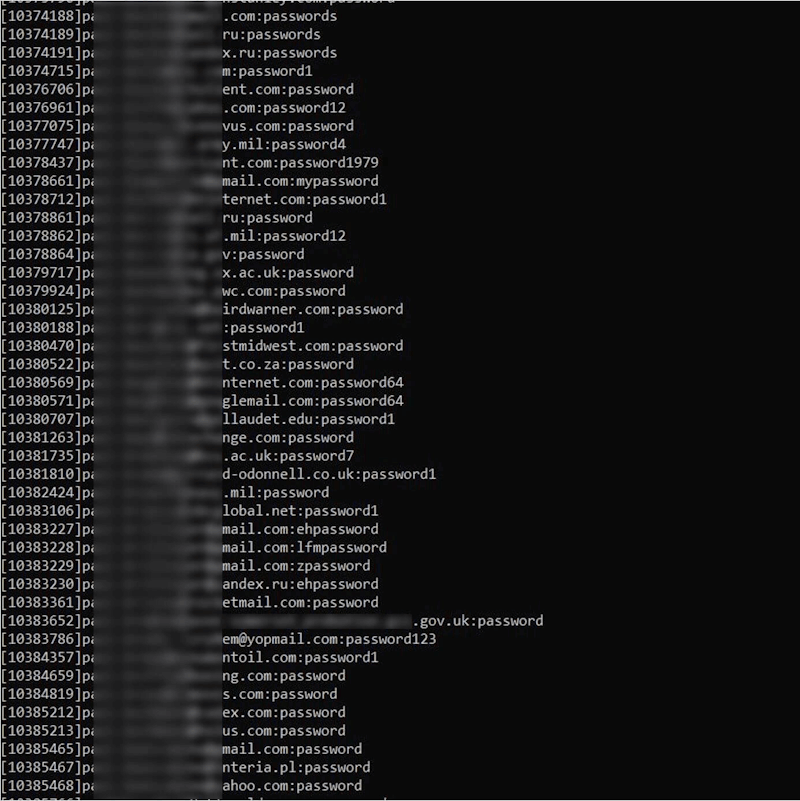
- Infostealer malware does what the title suggests. It has develop into extremely widespread due to “as-a-service” kits like RedLine and Lumma Stealer. The malware can also be hidden in legitimate-looking cell apps, on internet pages, in malicious advertisements, and phishing hyperlinks/attachments, amongst different puts. The information it collects is then assembled by way of risk actors and offered at the darkish internet. Incessantly, each credentials and consultation cookies are stolen, making it more uncomplicated for hackers to avoid even multi-factor authentication (MFA).
- Phishing has all the time been a well-liked method to scouse borrow knowledge from a sufferer. However the creation of generative AI (GenAI) equipment has made it more uncomplicated for risk actors to scale assaults, whilst additionally personalizing them, and writing in flawless native language to extend their probabilities of luck. In case you unwittingly click on thru and input your knowledge on a phishing web page, it might finally end up being offered at the darkish internet.
- Unintended leaks are a not unusual incidence on the web due frequently to misconfiguration of cloud methods, comparable to failing to require a password to get entry to on-line databases. This may depart knowledge uncovered to any individual who is aware of the place to appear (or has been scanning for misconfigured cases). If it’s left open for lengthy sufficient, a database might be stolen and offered at the darkish internet. Risk actors may just additionally delete the unique database to be able to extort their company sufferer.
- Provide chain assaults are very similar to common knowledge breaches, however as a substitute of the corporate you shared your knowledge with being hacked, this can be a provider or spouse group. Those firms were granted permission to get entry to and use that knowledge, however frequently don’t have the similar powerful safety posture. They’re a beautiful goal for risk actors as only one assault may just lend a hand them to get entry to knowledge on a couple of, company purchasers. Every so often, those providers are virtual suppliers, like Development Tool. When a zero-day vulnerability in its widespread MOVEit report switch device used to be exploited in 2023, hundreds of organizations and over 90 million downstream consumers have been compromised. Knowledge agents are every other attainable vulnerable hyperlink. They harvest knowledge legally by way of internet scraping and monitoring, however would possibly not stay it neatly secure.
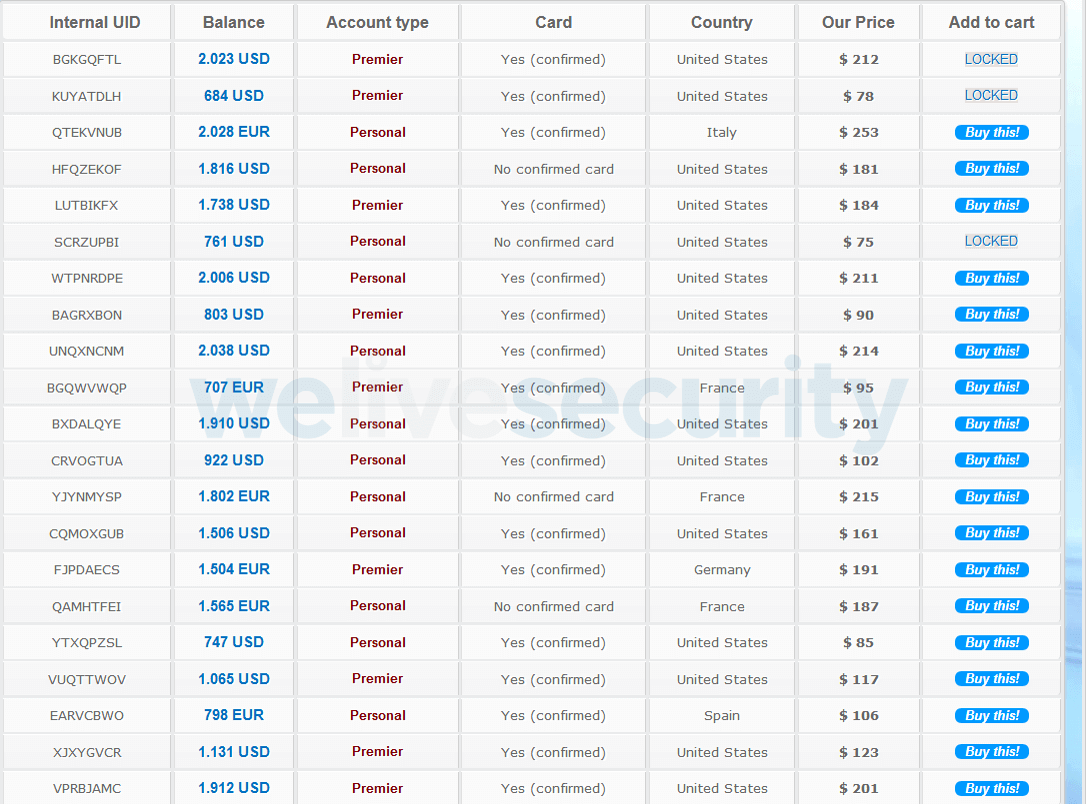
What do they would like?
The stuff that cybercriminals truly need is your monetary knowledge (checking account numbers, card main points and logins), PII, and account logins. With this, they are able to hijack accounts to empty them of information and finances, and most likely get entry to saved card knowledge, or else use your PII in follow-on phishing makes an attempt designed to pay money for monetary knowledge. However, they might use that PII in identification fraud, comparable to making use of for brand new traces of credit score, clinical remedy or welfare advantages.
Biometric knowledge is especially delicate as it could actually’t be “reissued” or reset like a password. And consultation tokens/cookies also are helpful for risk actors as those can lend a hand them to avoid MFA.
This may have a vital monetary have an effect on. A contemporary ITRC record claims that 20% of US fraud sufferers over a unmarried yr reported losses of over $100,000 and over 10% misplaced a minimum of $1m.
What to do in case you in finding your knowledge at the darkish internet
In case you’re alerted to the illusion of a few private and/or monetary knowledge at the darkish internet, take the next motion (relying at the knowledge in peril):
- Exchange any compromised passwords, and be sure you most effective use sturdy, distinctive credentials saved in a password supervisor.
- Transfer on MFA for all accounts, and use both an authenticator app or a {hardware} safety key, fairly than SMS (which can also be intercepted).
- Signal out of all gadgets, to forestall hackers who will have stolen your consultation cookies.
- Touch your financial institution, freeze your playing cards and feature them reissued.
- Freeze your credit score with every of the primary bureaus. This may save you any fraudster from opening a brand new line of credit score to your title.
- Scan your PC/gadgets for infostealer malware.
- Record the leak to the FTC (US), Record Fraud (UK) or related Eu government.
Lengthy-term steps to stay your PII protected
As soon as the mud has settled, there are issues you’ll do to mitigate the chance of delicate knowledge finishing up at the darkish internet. Believe services and products like Cover My E mail to scale back the quantity private knowledge firms retailer. It additionally can pay to stay a watch open for suspicious job to your financial institution accounts. It’s additionally a good suggestion to checkout as a visitor and not save any card information while you store with a third-party web page.
Subsequent, respected safety device on all your gadgets and PCs will cross some distance against lowering the probabilities of putting in infostealer compromise and phishing. Best obtain apps from authentic retail outlets. And be cautious of any unsolicited emails/texts/social media messages containing hyperlinks or attachments.
Scale back the quantity of information to be had to agents by way of making sure all your social accounts are set to “personal.” Use encrypted comms services and products and privacy-enhanced browsers and engines like google. Additionally, believe sending “proper to be forgotten” requests to knowledge agents, most likely by way of services and products with the considered necessary experience.
In spite of everything, some identification coverage services comparable to HaveIBeenPwned can scour the darkish internet on your main points to peer if they have got already been breached and/or warn you when any PII seems at the darkish internet. If there’s a fit, it might provide you with time to cancel playing cards, alternate passwords and take different precautions.
The breach of private knowledge and logins can also be emotionally frightening, in addition to financially harmful. And in case you reuse logins throughout paintings accounts, it might also have a detrimental have an effect on in your occupation, if it allows hackers to get entry to company sources. On the finish of the day, all of us wish to be proactive to be able to make our virtual lives more secure.




