Hackers received get right of entry to to an API for the CPUID undertaking and modified the obtain hyperlinks at the respectable web page to serve malicious executables for the preferred CPU-Z and HWMonitor equipment.
The 2 utilities have hundreds of thousands of customers who depend on them for monitoring the bodily well being of inside laptop {hardware} and for complete specs of a device.
Customers who downloaded both software reported on Reddit not too long ago that the respectable obtain portal issues to the Cloudflare R2 garage carrier and fetches a trojanized model of HWiNFO, some other diagnostic and tracking software from a distinct developer.

The identify of the malicious record is HWiNFO_Monitor_Setup, and working it launches a Russian installer with an Inno Setup wrapper, which is peculiar and extremely suspicious.
Customers reported that downloading the blank hwmonitor_1.63.exe from the direct URL used to be nonetheless conceivable, indicating that the unique binaries have been intact, however the distribution hyperlinks seem to have been poisoned.
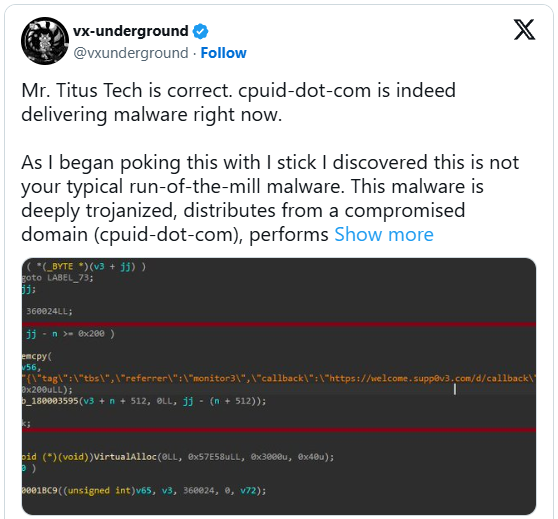
The externalized obtain chain used to be additionally showed via Igor’s Labs and @vxunderground, who reported {that a} reasonably complicated loader the usage of recognized ways, techniques, and procedures (TTPs) is concerned.
“As I started poking this with a stick, I found out this isn’t your conventional run-of-the-mill malware,” said vxunderground.
“This malware is deeply trojanized, distributes from a compromised area (cpuid-dot-com), plays record masquerading, is multi-staged, operates (nearly) fully in-memory, and makes use of some attention-grabbing find out how to evade EDRs and/or AVs reminiscent of proxying NTDLL capability from a .NET meeting.”
The researcher claims that the similar danger team centered customers of the FileZilla FTP answer ultimate month, suggesting that the attacker is specializing in extensively used utilities.
The downloaded ZIP is flagged via 20 antivirus engines on VirusTotal, even supposing no longer obviously recognized. Some classify it as Tedy Trojan, and others as Artemis Trojan.
Some researchers on Virustotal say that the faux HWiNFO variant is an infostealer malware.
BleepingComputer has contacted CPUID to be told extra about what took place, the date of the compromise, the affected variations, and what impacted customers must do. A spokesperson has equipped the next observation.
“Investigations are nonetheless ongoing, however it sounds as if {that a} secondary characteristic (mainly a facet API) used to be compromised for about six hours between April 9 and April 10, inflicting the primary web page to randomly show malicious hyperlinks (our signed unique information weren’t compromised). The breach used to be discovered and has since been fastened.” – CPUID
The similar particular person advised us that the hackers hit them at a time when the primary developer used to be away on vacation.
Recently, it sounds as if that CPUID has fastened the issue and now serves blank variations for each CPU-Z and HWMonitor.

Computerized pentesting proves the trail exists. BAS proves whether or not your controls forestall it. Maximum groups run one with out the opposite.
This whitepaper maps six validation surfaces, displays the place protection ends, and offers practitioners with 3 diagnostic questions for any software analysis.