
The ShinyHunters extortion crew stole the non-public data of five.5 million folks after breaching the techniques of house safety massive ADT previous this month, consistent with knowledge breach notification carrier Have I Been Pwned.
Based in 1874 as American District Telegraph, ADT is the oldest and biggest house safety corporate in america, these days offering monitored safety and sensible house answers to over 6 million residential and small-business consumers.
ADT has in the past disclosed two different knowledge breaches in August 2024 and October 2024 that revealed worker and buyer data.

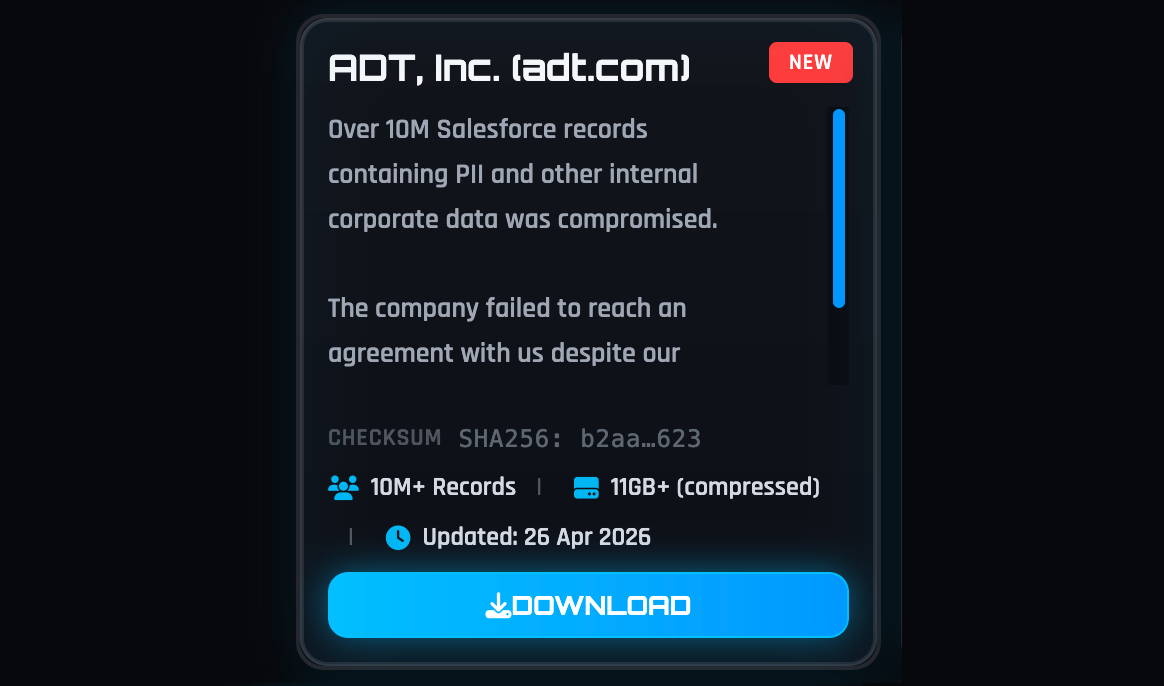
Have I Been Pwned’s record comes after ShinyHunters claimed remaining week that they’d stolen over 10 million information containing individually identifiable data (PII) and ADT company knowledge.
When requested to substantiate the cybercrime crew’s claims, ADT advised BleepingComputer that it detected the breach on April 20 and {that a} follow-up investigation discovered the intrusion was once restricted however allowed the attackers to get admission to some folks’ private data.
“The investigation showed that the tips concerned was once restricted to names, telephone numbers, and addresses. In a small proportion of circumstances, dates of beginning and the remaining 4 digits of Social Safety numbers or Tax IDs had been integrated,” ADT advised BleepingComputer.
“Seriously, no fee data — together with financial institution accounts or bank cards — was once accessed, and buyer safety techniques weren’t affected or compromised by any means.”
The cybercrime crew has since leaked an 11GB archive of stolen knowledge on its darkish internet leak website after failing to extort the corporate.
Whilst ADT has but to divulge the overall selection of affected folks, Have I Been Pwned analyzed the stolen knowledge and stated the breach uncovered the knowledge of five.5 million other people, together with distinctive e-mail addresses, names, dates of beginning, telephone numbers, bodily addresses, and partial government-issued IDs.
The extortion crew advised BleepingComputer that they’d allegedly breached the corporate after compromising an worker’s Okta unmarried sign-on (SSO) account in a voice phishing (vishing) assault. The usage of this worker account, the attackers stated they won get admission to and stole knowledge from the corporate’s Salesforce example.
ShinyHunters has been in the back of popular vishing campaigns that started remaining yr and goal workers’ and Trade Procedure Outsourcing (BPO) brokers’ Microsoft Entra, Okta, and Google SSO accounts.
After breaching company SSO accounts, they thieve knowledge from hooked up SaaS programs akin to Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, Dropbox, and others.
Final week, ShinyHunters additionally claimed to have stolen greater than 9 million information from Medtronic, the arena’s biggest clinical instrument maker via income, with operations in 150 international locations.
Different firms that the extortion claimed to have breached in contemporary weeks come with the Ecu Fee, Rockstar Video games, edtech massive McGraw Hill, and, extra lately, comfort retailer chain 7-11, cruise line operator Carnival, rapid style store Zara, and on-line coaching corporate Udemy.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Independent Validation Summit (Would possibly 12 & 14), see how self sufficient, context-rich validation unearths what is exploitable, proves controls hang, and closes the remediation loop.
Declare Your Spot



