
Cybersecurity companies within the U.S. and U.Ok. are caution a couple of customized malware known as Firestarter persisting on Cisco Firepower and Protected Firewall units working Adaptive Safety Equipment (ASA) or Firepower Danger Protection (FTD) tool.
The backdoor has been attributed to a danger actor that Cisco Talos tracks internally as UAT-4356, identified for cyberespionage campaigns, together with ArcaneDoor.
The U.S. Cybersecurity and Infrastructure Safety Company (CISA) and the U.Ok. Nationwide Cyber Safety Middle (NCSC) consider that the adversary acquired preliminary get right of entry to by means of exploiting a lacking authorization factor (CVE-2025-20333) and/or a buffer overflow trojan horse (CVE-2025-20362).

In a single incident at a federal civilian govt department company, CISA seen the danger actor first deploying the Line Viper malware, a user-mode shellcode loader, after which the use of Firestarter, which permits endured get right of entry to even after patching.
“CISA has no longer showed the precise date of preliminary exploitation however assesses the compromise passed off in early September 2025, and sooner than the company carried out patches in line with ED 25-03,” the company notes in an alert.
Line Viper is used to determine VPN periods and get right of entry to all configuration main points, together with administrative credentials, certificate, and personal keys on compromised Firepower units.
Subsequent, the ELF binary for the Firestarter backdoor is deployed for endurance, permitting the danger actor to regain get right of entry to when wanted.
As soon as Firestarter nests at the units, it maintains endurance throughout reboots, firmware updates, and safety patches. Moreover, the backdoor relaunches routinely if terminated.
Patience is accomplished by means of hooking into LINA, the core Cisco ASA procedure, and the use of sign handlers that cause reinstallation routines.
A joint malware research record from the 2 cybersecurity companies explains that Firestarter modifies the CSP_MOUNT_LIST boot/mount report to make sure execution on startup, retail outlets a duplicate of itself in /decide/cisco/platform/logs/var/log/svc_samcore.log, and restores it to /usr/bin/lina_cs, the place it runs within the background.
Cisco Talos additionally revealed its research of the malware, announcing that the endurance mechanism is prompted when a procedure termination sign is gained, often referred to as a swish reboot.
The researchers famous within the Firestarter record that the backdoor used the instructions under to set endurance for itself:
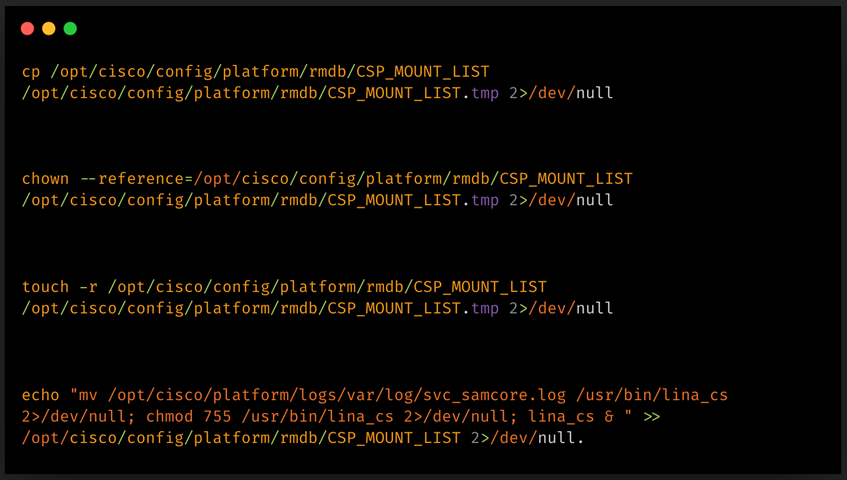
Supply: Cisco
The implant’s core serve as is to behave as a backdoor for far flung get right of entry to, whilst it will probably additionally execute attacker-provided shellcode.
That is accomplished via a mechanism through which Firestarter hooks into LINA by means of editing an XML handler and injecting shellcode into reminiscence, making a managed execution trail.
This shellcode is prompted by means of a specifically crafted WebVPN request, which, after validating a hardcoded identifier, a lot and executes attacker-supplied payloads at once in reminiscence.
Then again, CISA didn’t supply any main points at the explicit payloads seen in assaults.
Cisco revealed a safety advisory about Firestarter that comprises mitigations and workarounds for doing away with the endurance mechanism, in addition to signs of compromise for locating the Firestarter implant.
The seller “strongly recommends reimaging and upgrading the software the use of the mounted releases,” which covers each compromised and non-compromised circumstances.
To resolve a compromise, directors will have to run the ‘display kernel procedure | come with lina_cs’ command. For any ensuing output, the software will have to be regarded as compromised.
If software re-imaging isn’t these days conceivable, Cisco says {that a} chilly restart (disconnecting the software energy) eliminates the malware. Then again, this selection isn’t advisable because it carries the danger of database or disk corruption, resulting in boot issues.
CISA has additionally shared two YARA regulations that may come across the Firestarter backdoor when carried out to a disk symbol or a core sell off from a tool.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Self sustaining Validation Summit (Might 12 & 14), see how self sufficient, context-rich validation reveals what is exploitable, proves controls dangle, and closes the remediation loop.
Declare Your Spot



