A brand new vulnerability dubbed Pack2TheRoot might be exploited within the PackageKit daemon to permit native Linux customers to put in or take away device programs and acquire root permissions.
The flaw is recognized as CVE-2026-41651 and won a medium-severity ranking of 8.8 out of 10. It has persevered for just about 12 years within the PackageKit daemon, a background provider that manages instrument set up, updates, and removing throughout Linux programs.
Previous this week, some details about the vulnerability has been printed, in conjunction with PackageKit model 1.3.5 that addresses the problem. Then again, technical main points and a demo exploit were no longer been disclosed to permit the patches to propagate.

An investigation from the Deutsche Telekom Purple Workforce exposed that the reason for the malicious program is the mechanism PackageKit makes use of to deal with bundle control requests.
In particular, the researchers discovered that instructions like ‘pkcon set up’ may just execute with out requiring authentication underneath positive stipulations on a Fedora device, letting them set up a device bundle.
The usage of the Claude Opus AI instrument, they additional explored the opportunity of exploiting this conduct and found out CVE-2026-41651.
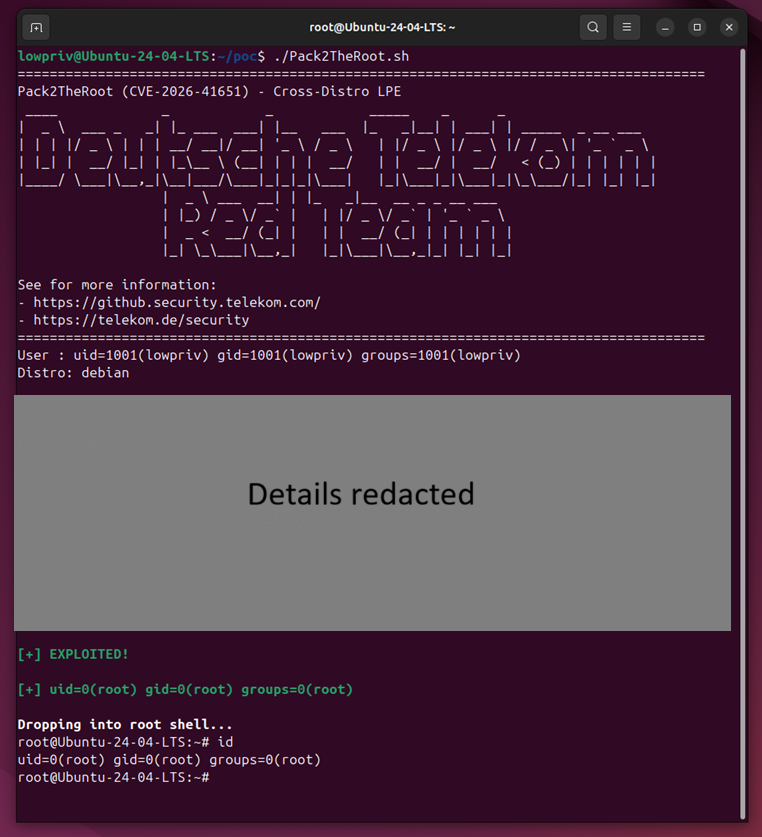
Supply: Deutsche Telekom
Affect and fixes
Deutsche Telekom’s Purple Workforce reported their findings to Purple Hat and PackageKit maintainers on April 8. They state that it’s secure to think that every one distributions that include PackageKit pre-installed and enabled out-of-the-box are at risk of CVE-2026-41651.
The vulnerability has been found in PackageKit model 1.0.2, launched in November 2014, and impacts all variations thru 1.3.4, consistent with the venture’s safety advisory.
Researchers’ checking out have showed that an attacker may just exploit the the CVE-2026-41651 vulnerability within the following Linux distributions:
- Ubuntu Desktop 18.04 (EOL), 24.04.4 (LTS), 26.04 (LTS beta)
- Ubuntu Server 22.04 – 24.04 (LTS)
- Debian Desktop Trixie 13.4
- RockyLinux Desktop 10.1
- Fedora 43 Desktop
- Fedora 43 Server
The record isn’t exhaustive, regardless that, and any Linux distribution the use of PackageKit will have to be handled as probably at risk of assaults.
Customers will have to improve to PackageKit model 1.3.5 once conceivable, and make certain that every other instrument the use of the bundle as a dependency has been moved to a secure unencumber.
Customers can use the instructions underneath to test if they have got a inclined model of the PackageKit put in and if the daemon is operating:
dpkg -l | grep -i packagekit
rpm -qa | grep -i packagekit
Customers can run systemctl standing packagekit or pkmon to test if the PackageKit daemon is to be had and operating, which signifies that the device could also be in peril if left unpatched.
Even though no information about the state of exploitation were shared, the researchers famous that there are robust indicators appearing compromise as a result of exploitation results in the PackageKit daemon hitting an statement failure and crashing.
Even though systemd recovers the daemon, the crash is observable within the device logs.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Self sustaining Validation Summit (Might 12 & 14), see how self reliant, context-rich validation reveals what is exploitable, proves controls hang, and closes the remediation loop.
Declare Your Spot