
The Bitwarden CLI used to be in short compromised after attackers uploaded a malicious @bitwarden/cli bundle to npm containing a credential-stealing payload able to spreading to different tasks.
Consistent with experiences by means of Socket, JFrog, and OX Safety, the malicious bundle used to be dispensed as model 2026.4.0 and remained to be had between 5:57 PM and seven:30 PM ET on April 22, 2026, prior to being got rid of.
Bitwarden showed the incident, mentioning that the breach affected most effective its npm distribution channel for the CLI npm bundle and most effective those that downloaded the malicious model.

“The investigation discovered no proof that finish consumer vault information used to be accessed or in danger, or that manufacturing information or manufacturing techniques have been compromised. As soon as the problem used to be detected, compromised get entry to used to be revoked, the malicious npm unlock used to be deprecated, and remediation steps have been initiated right away,” Bitwarden shared in a remark.
“The problem affected the npm distribution mechanism for the CLI all through that restricted window, now not the integrity of the reliable Bitwarden CLI codebase or saved vault information.”
Bitwarden says it revoked the compromised get entry to and deprecated the affected CLI npm unlock.
The Bitwarden provide chain assault
Consistent with Socket, danger actors seem to have used a compromised GitHub Motion in Bitwarden’s CI/CD pipeline to inject malicious code into the CLI npm bundle.
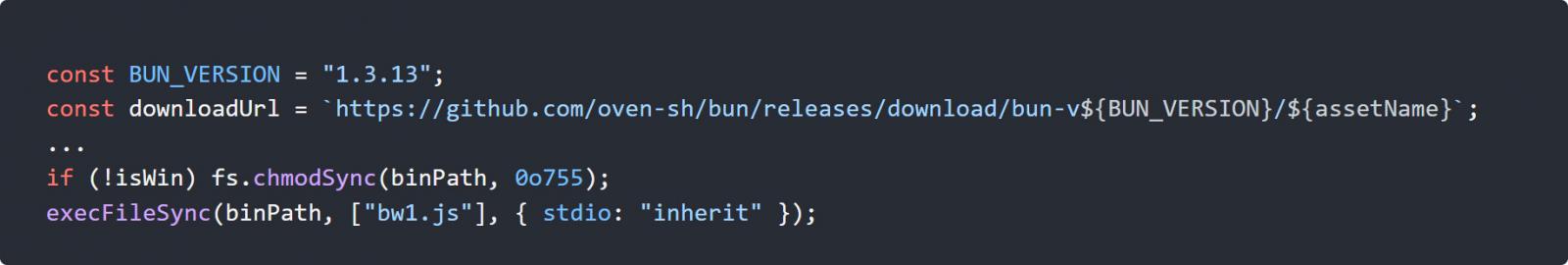
Consistent with JFrog, the bundle used to be changed in order that the preinstall script and the CLI access level use a customized loader named bw_setup.js, which assessments for the Bun runtime and, if it does now not exist, downloads it.
The loader then makes use of the Bun runtime to release an obfuscated JavaScript record named bw1.js, which acts as credential-stealing malware.
Supply: Jfrog
As soon as accomplished, the malware collects a variety of secrets and techniques from inflamed techniques, together with npm tokens, GitHub authentication tokens, SSH keys, and cloud credentials for AWS, Azure, and Google Cloud.
The malware encrypts the gathered information the usage of AES-256-GCM and exfiltrates it by means of growing public GitHub repositories beneath the sufferer’s account, the place the encrypted information is saved.
OX Safety says that those created repositories comprise the string “Shai-Hulud: The 3rd Coming,” a connection with earlier npm provide chain assaults that used a an identical means and textual content string when exfiltrating stolen information.
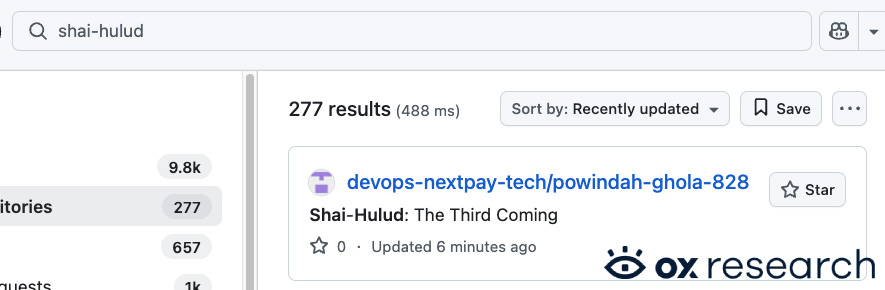
Supply: OX Safety
The malware additionally options self-propagation functions, with OX Safety reporting that it could use stolen npm credentials to spot programs the sufferer can regulate and inject them with malicious code.
Socket additionally noticed that the payload objectives CI/CD environments and makes an attempt to reap secrets and techniques that may be reused to enlarge the assault.
The assault comes after Checkmarx disclosed a separate provide chain incident the day before today that affects its KICS Docker pictures, GitHub Movements, and developer extensions.
Whilst it isn’t identified how the danger actors received get entry to to Bitwarden’s account to post the malicious NPM, Socket informed BleepingComputer that there are overlapping signs between the Checkmarx breach and this assault.
“The relationship is on the malware and infrastructure stage. Within the Bitwarden case, the malicious payload makes use of the similar audit.checkmarx[.]cx/v1/telemetry endpoint that gave the impression within the Checkmarx incident. It additionally makes use of the similar __decodeScrambled obfuscation regimen with the seed 0x3039, and presentations the similar common trend of credential robbery, GitHub-based exfiltration, and provide chain propagation habits,” Socket informed BleepingComputer.
“That overlap is going past a superficial resemblance. The Bitwarden payload incorporates the similar roughly embedded gzip+base64 elements we noticed within the previous malware, together with tooling for credential assortment and downstream abuse.”
Each campaigns were connected to a danger actor referred to as TeamPCP, who prior to now focused developer programs within the huge Trivy and LiteLLM provide chain assaults.
Builders who put in the affected model will have to deal with their techniques and credentials as compromised and rotate all uncovered credentials, particularly the ones used for CI/CD pipelines, cloud garage, and developer environments.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Self sustaining Validation Summit (Might 12 & 14), see how self sustaining, context-rich validation reveals what is exploitable, proves controls cling, and closes the remediation loop.
Declare Your Spot



