
Fraudulent telephone calls have develop into a day by day fact for tens of millions of folks international. From pretend cops to financial institution representatives and impersonated tech improve brokers, sufferers are more and more focused thru direct, real-time conversations designed to create urgency accompanied by means of prime mental power to extract delicate knowledge or cash robbery.
Reviews display that this kind of cybercrime considerably affects society each financially and emotionally. Consistent with the FBI, US aged voters (60+) misplaced $3.4B in 2023. Any other record presentations that vishing greater by means of 449% in 2025 and the common loss in line with rip-off name is $3,690.
On this article, we shine a gentle on what may also be described as “Caller-as-a-Provider”, which is an under-explored but hastily evolving aspect of recent cybercrime. We read about how, similar to official gross sales organizations, risk actors have followed structured, business-like working fashions, whole with specialization, scalability, and performance-driven execution.
Those ecosystems are now not advert hoc. They’re composed of distinct roles and purposes, with other actors specializing in explicit phases of the assault lifecycle: from infrastructure and tooling to social engineering execution.
We discover how those networks function, together with their recruitment methods, explained roles and obligations, or even adapted reimbursement fashions—all of which carefully replicate official marketplace dynamics.
The result’s a extremely arranged, service-driven economic system that professionalizes fraud at scale, reducing the barrier to access whilst expanding each potency and affect.
A Structured Arranged Marketplace
The rip-off name ecosystem has develop into extremely professionalized and segmented, mirroring official enterprise operations. Distinct roles now exist around the worth chain, together with malware builders, vendors, phishing package developers, infrastructure operators, log dealers, information analysts, sufferer listing buyers, and in the end, rip-off callers who execute the assaults.
This department of work lets in each and every player to specialize. For callers, who’re only considering interacting with sufferers, the emphasis shifts towards recruitment high quality and operational professionalism quite than technical capacity.
In consequence, the barrier to access is considerably diminished. Folks now not want to broaden malware or organize infrastructure, and they are able to focal point on refining verbal exchange talents, persuasion ways, and social engineering techniques.
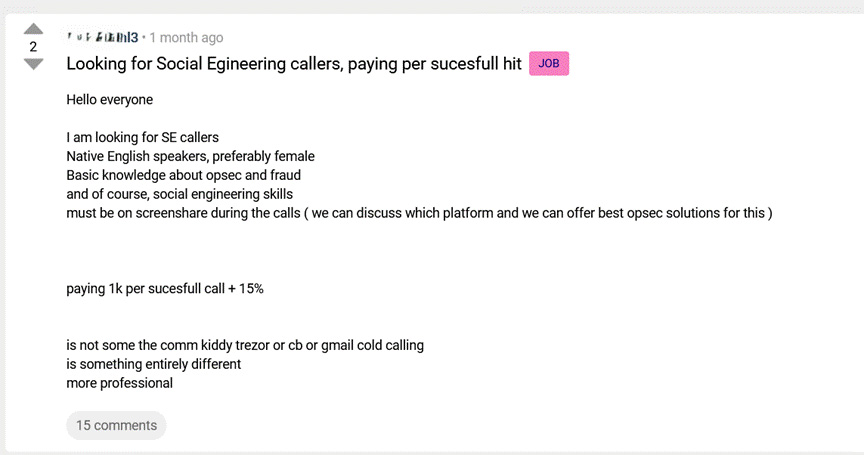
Recruitment posts mirror this specialization. They normally define transparent necessities similar to local English skillability, familiarity with operational safety (OPSEC), and prior fraud revel in. Significantly, some roles require individuals to stay on display proportion all through reside calls.
This requirement is especially revealing. It signifies that operators aren’t merely outsourcing duties, however actively supervising functionality in genuine time. This introduces a degree of high quality keep an eye on and operational oversight extra usually related to official name facilities than with conventional cybercrime.
Such supervision serves more than one functions: making sure adherence to scripts, making improvements to conversion charges, and combating inside fraud or information leakage. In the long run, this layered and regulated fashion highlights how trendy fraud operations are controlled with the similar common sense, construction, and potency as official companies.
Structured fraud operations depend on leaked credentials and sufferer lists sourced from underground markets.
Flare displays 1000’s of darkish internet boards, Telegram channels, and marketplaces, so your workforce can come across uncovered information sooner than it fuels the following rip-off marketing campaign.
Stay alongside of risk actors free of charge.
Underground Recruitment Ways
When official firms need to draw in possible staff, they illustrate robust monetary spine, buyer testimonials, or even glad staff footage.
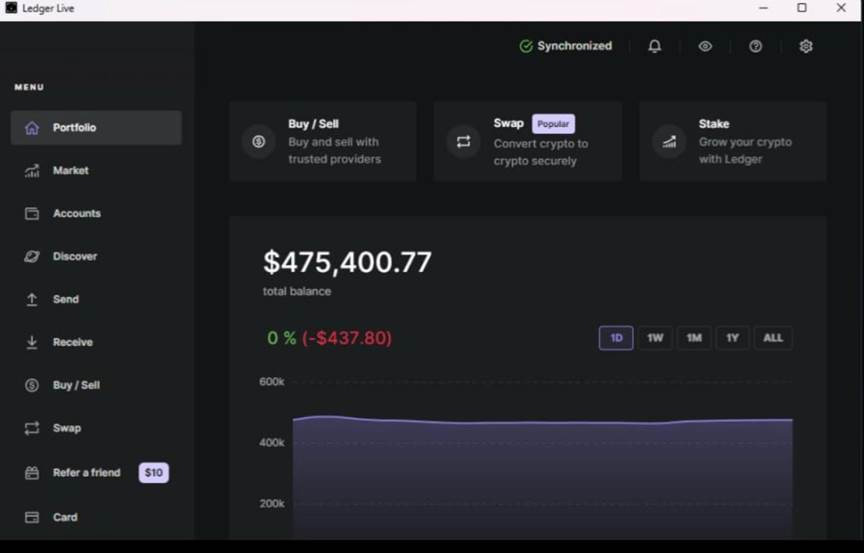
Within the underground, a screenshot of a prime steadiness of the corporate’s cryptocurrency pockets is sufficient. A steadiness of roughly $475,000 serves as a recruitment help designed to draw recruitments. Such “proof-of-profit” visuals are usually utilized in underground communities to determine credibility and reveal possible income. Whether or not unique or fabricated, their objective is to scale back skepticism and inspire participation.
This tactic displays broader traits in cybercriminal ecosystems, the place recognition and perceived achievement play a vital position in recruitment and collaboration.
Rip-off Callers Reimbursement Fashions
Flare’s research signifies that more than a few reimbursement fashions exist together with fastened bills, success-based bills and a hybrid way that mixes each fastened bills and success-based bills.
In a single fashion, callers obtain a share of extracted price range, with upper percentages awarded for greater payouts. In every other fashion, operators be offering a set cost of $1,000 in line with a hit name, supplemented by means of an extra share.
Conversations between risk actors supply insights concerning the reimbursement fashion. One operator explains that a hit social engineering does no longer all the time translate into rapid monetization, thus the reimbursement may be behind schedule or conditioned.
This difference is vital. It signifies that the fraud procedure extends past the preliminary name, involving further steps to transform get right of entry to or knowledge into monetary achieve. In consequence, operators compensate callers for a hit engagement whilst maintaining keep an eye on over downstream monetization processes.
Contributors do not merely settle for phrases. They ask questions, examine provides, and weigh reimbursement sooner than committing. It is a dynamic indistinguishable from any official activity marketplace.
Rip-off Callers Activity Necessities, Roles and Duties
Just like activity postings on LinkedIn, underground operators craft well-defined and extremely focused recruitment commercials. Those postings are a long way from generic, they usually obviously define the specified characteristics, obligations, and revel in for each and every position, reflecting a degree of adulthood normally related to official organizations.
For rip-off callers, the emphasis is going past technical capacity. Applicants are anticipated to reveal robust comfortable talents, together with transparent verbal exchange, emotional intelligence, and complex mental manipulation ways. At their core, those roles revolve across the skill to construct consider, create urgency, and convince sufferers into movements that result in monetary loss or account compromise.
A notable trend is the choice for local English audio system, indicating planned focused on of explicit geographic areas. This highlights the significance put on cultural alignment and linguistic fluency to maximise achievement charges.
When mixed with real-time supervision and function comments, those operations resemble structured gross sales flooring, the place social engineering isn’t just finished, however ceaselessly subtle and optimized for upper conversion.
Shift Towards Industrialized Social Engineering
The convergence of recruitment, supervision, structured incentives, and modular workflows displays a broader shift towards industrialized fraud operations. This fashion mirrors trends noticed in ransomware-as-a-service (RaaS) and preliminary get right of entry to brokerage, the place specialization and department of work pressure potency.
On the other hand, on this case, the main assault vector is human interplay, making it each available and tough to come across.
Implications for Defenders and Folks
Those threats mirror a transparent shift towards structured, scalable fraud operations, posing rising demanding situations for each organizations and people.
The decentralized nature of those ecosystems makes disruption inherently tough. Eliminating particular person callers has restricted affect, as important elements (sufferer information, operators, and monetization channels) are disbursed and resilient.
On the similar time, the reliance on compromised information assets reinforces a key fact: upstream breaches at once gasoline downstream fraud.
Compounding that is the expanding stage of professionalism. With parts similar to real-time supervision, explained workflows, and structured reimbursement fashions, those operations are turning into extra constant, environment friendly, and tougher to come across.
To counter this, defenders must prioritize:
- More potent identification verification mechanisms
- Behavioral anomaly detection
- Person consciousness considering real-time social engineering eventualities
For people, it’s vital to keep in mind that fraudulent calls are hardly random, they’re incessantly a part of coordinated, data-driven campaigns.
Be wary of unsolicited calls that:
- Create a way of urgency
- Request delicate or monetary knowledge
- Power you into rapid motion
Even though a caller seems credible, by no means proportion passwords, verification codes, or monetary main points over the telephone.
If one thing feels off, the most secure way is unassuming: cling up and phone the group at once thru legit channels.
After all, enabling multi-factor authentication (MFA) can considerably cut back the affect of compromised credentials, including a important layer of coverage towards account takeover.
How Flare Can Assist
Flare supplies early visibility into fraud operations sooner than they succeed in sufferers. By way of tracking underground boards, Telegram channels, and marketplaces, Flare detects leaked information, sufferer lists, and recruitment task tied to Caller-as-a-Provider campaigns.
This permits organizations to proactively reply (reset credentials, alert customers, and make stronger defenses) sooner than attackers strike, decreasing each possibility and affect.
Be informed extra by means of signing up for our unfastened trial.
Backed and written by means of Flare.



