
Over 1,300 Microsoft SharePoint servers uncovered on-line stay unpatched in opposition to a spoofing vulnerability that was once exploited as a zero-day and remains to be being abused in ongoing assaults.
The protection flaw, tracked as CVE-2026-32201, impacts SharePoint Endeavor Server 2016, SharePoint Server 2019, and SharePoint Server Subscription Version (the newest on-premises model, which makes use of a “steady replace” type).
As Microsoft defined when it patched this safety factor as a part of the April 2026 Patch Tuesday, a hit exploitation lets in risk actors with out privileges to accomplish community spoofing through benefiting from an incorrect enter validation weak spot in low-complexity assaults that do not require person interplay.

“An attacker who effectively exploited the vulnerability may view some delicate knowledge (Confidentiality), make adjustments to disclosed knowledge (Integrity), however can not prohibit get admission to to the useful resource (Availability),” it mentioned.
Whilst Microsoft flagged the vulnerability as a zero-day, it has but to reveal the way it was once exploited in assaults or hyperlink this malicious process to a selected risk actor or hacking staff.
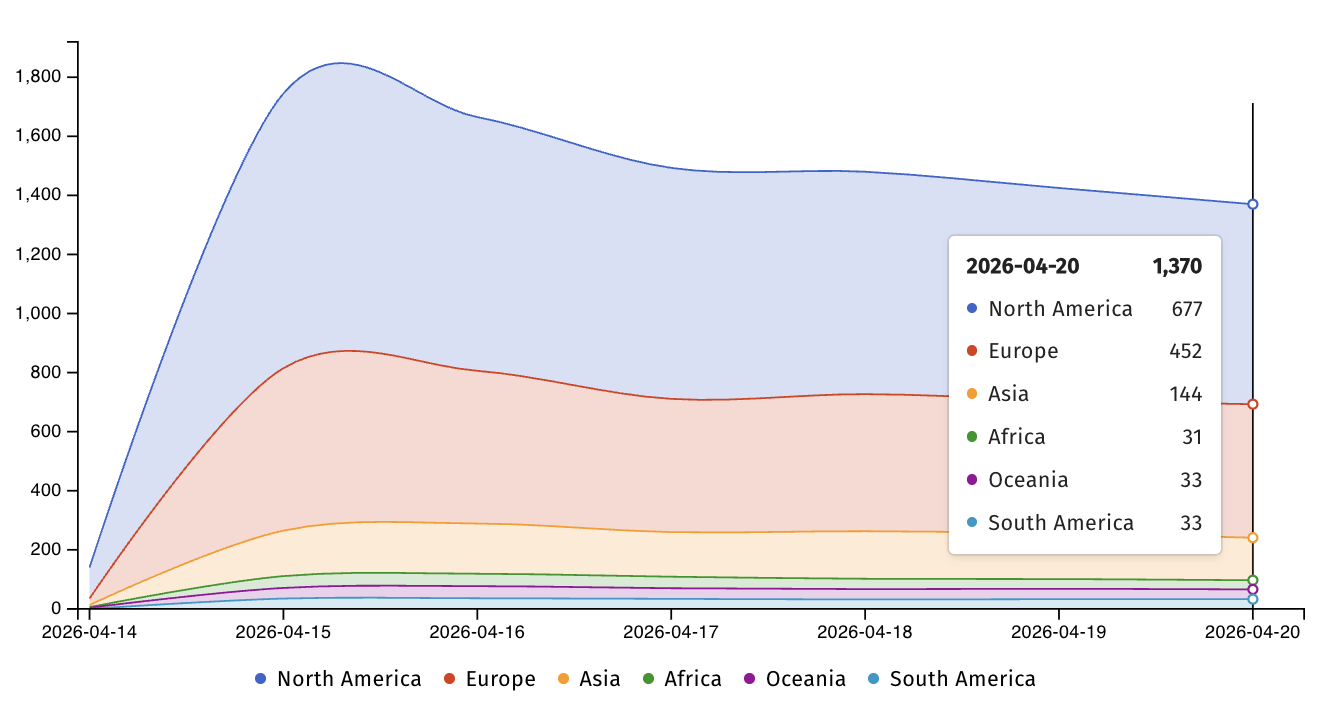
On Tuesday, Web safety watchdog staff Shadowserver warned that over 1,300 unpatched Microsoft SharePoint servers uncovered on-line are nonetheless ready to be secured, with fewer than 200 methods patched since Microsoft launched CVE-2026-32201 safety updates remaining week.
The similar day Microsoft launched patches for CVE-2026-32201, CISA added the vulnerability to its Identified Exploited Vulnerabilities (KEV) Catalog.
The U.S. cybersecurity company additionally ordered Federal Civilian Govt Department (FCEB) companies (govt department non-military companies, such because the Division of the Treasury and the Division of Native land Safety) to patch SharePoint servers inside two weeks, through April 28, as mandated through the Binding Operational Directive (BOD) 22-01.
“This sort of vulnerability is a common assault vector for malicious cyber actors and poses important dangers to the federal undertaking,” it warned.
“Practice mitigations in line with seller directions, observe acceptable BOD 22-01 steering for cloud services and products, or discontinue use of the product if mitigations are unavailable.”
One week in the past, CISA additionally flagged a Home windows Process Host privilege escalation vulnerability as exploited within the wild, caution federal companies to protected their units once imaginable, as it would permit attackers to achieve SYSTEM privileges on susceptible units.
On April 14, Microsoft launched safety updates addressing 167 vulnerabilities, together with two zero-day flaws, as a part of its April 2026 Patch Tuesday.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Self reliant Validation Summit (Might 12 & 14), see how self sustaining, context-rich validation unearths what is exploitable, proves controls grasp, and closes the remediation loop.
Declare Your Spot



