
A financially motivated risk actor tracked as Typhoon-2755 is stealing Canadian staff’ wage bills after hijacking their accounts in payroll pirate assaults.
The attackers used malicious Microsoft 365 sign-in pages to scouse borrow sufferers’ authentication tokens and consultation cookies by way of redirecting them to domain names (e.g., bluegraintours[.]com) webhosting malicious internet pages (driven to the highest of seek engine effects thru malvertising or search engine optimization poisoning) that masqueraded as Microsoft 365 sign-in bureaucracy.
This allowed Typhoon-2755 to avoid multifactor authentication (MFA) in adversary‑in‑the‑center (AiTM) assaults by way of replaying stolen consultation tokens somewhat than re-authenticating.

“Moderately than harvesting most effective usernames and passwords, AiTM frameworks proxy all of the authentication drift in actual time, enabling the seize consultation cookies and OAuth get entry to tokens issued upon a hit authentication,” Microsoft defined.
“Because of those tokens representing an absolutely authenticated consultation, risk actors can reuse them to realize get entry to to Microsoft services and products with out being caused for credentials or MFA, successfully bypassing legacy MFA protections now not designed to be phishing-resistant.”
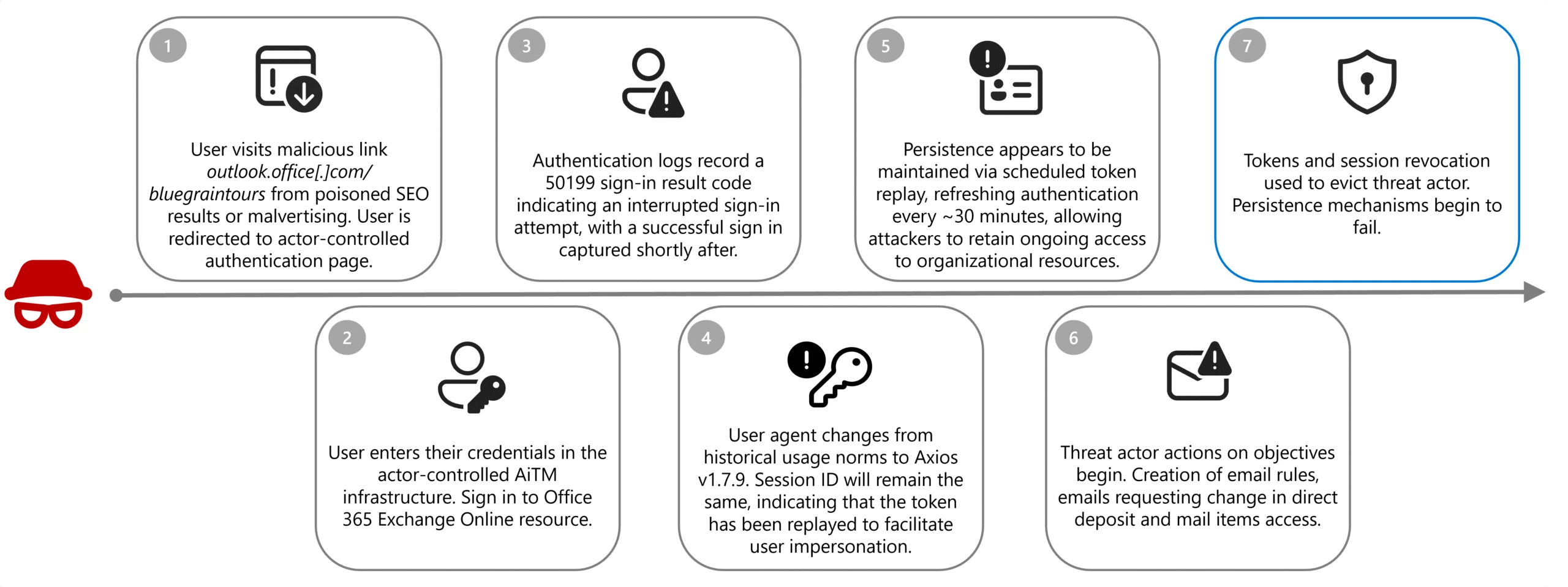
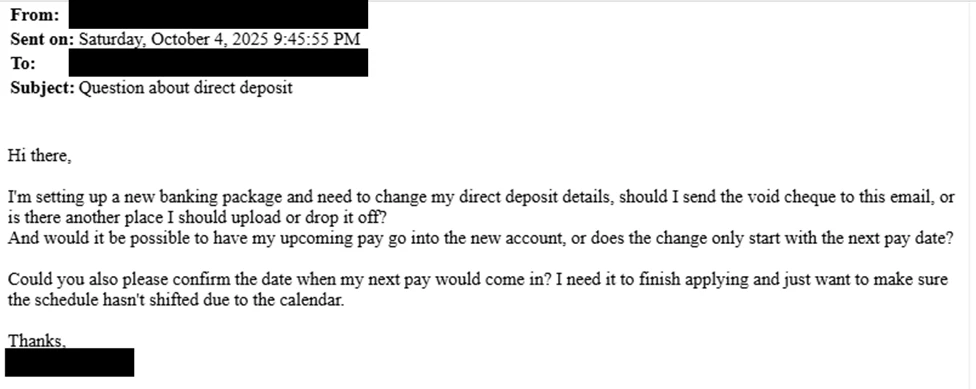
After getting access to an worker’s account, the attacker created inbox regulations that routinely moved messages from human assets personnel containing the phrases “direct deposit” or “financial institution” to hidden folders, fighting the sufferer from seeing the correspondence.
Within the subsequent degree, they looked for “payroll,” “HR,” “direct deposit,” and “finance,” then despatched emails to human assets personnel with the topic line “Query about direct deposit” to trick personnel into updating banking knowledge.
The place social engineering failed, the attacker logged without delay into HR tool platforms akin to Workday, the use of the stolen consultation to manually replace direct deposit main points.
To harden defenses in opposition to AiTM and payroll pirate assaults, Microsoft advises defenders to dam legacy authentication protocols and enforce phishing-resistant MFA.
If any indicators of compromise are detected, they will have to additionally revoke compromised tokens and classes in an instant, take away malicious inbox regulations, and reset MFA strategies and credentials for all affected accounts.
In October, Microsoft disrupted some other pirate payroll marketing campaign concentrated on Workday accounts since March 2025, during which a cybercrime gang tracked as Typhoon-2657 centered college staff throughout the US to hijack their wage bills.
In those assaults, Typhoon-2657 breached the goals’ accounts by means of phishing emails and stole MFA codes the use of AITM ways, which allowed the risk actors to compromise the sufferers’ Trade On-line accounts.
Payroll pirate assaults are a variant of commercial electronic mail compromise (BEC) scams that concentrate on companies and people who frequently make twine transfers. Ultimate yr, the FBI’s Web Crime Criticism Heart (IC3) recorded over 24,000 BEC fraud proceedings, leading to losses exceeding $3 billion, making it the second one maximum profitable crime sort in the back of funding scams.

Automatic pentesting proves the trail exists. BAS proves whether or not your controls forestall it. Maximum groups run one with out the opposite.
This whitepaper maps six validation surfaces, presentations the place protection ends, and offers practitioners with 3 diagnostic questions for any instrument analysis.



