
Cybersecurity company Kaspersky experiences that the Amazon Easy E-mail Provider (SES) is being an increasing number of abused to ship convincing phishing emails that may bypass same old safety filters and render reputation-based blocks useless.
Despite the fact that the useful resource has been leveraged for malicious job prior to now, Kaspersky says the present spike is also because of a lot of AWS Id and Get right of entry to Control get entry to keys uncovered in public property.
As a result of this can be a official, relied on useful resource, phishing operations can leverage Amazon SES to ship out malicious emails that go authentication exams.
Kaspersky researchers word in a document these days that they have got “seen an uptick in phishing assaults leveraging Amazon SES” to ship hyperlinks that redirect to a malicious website.
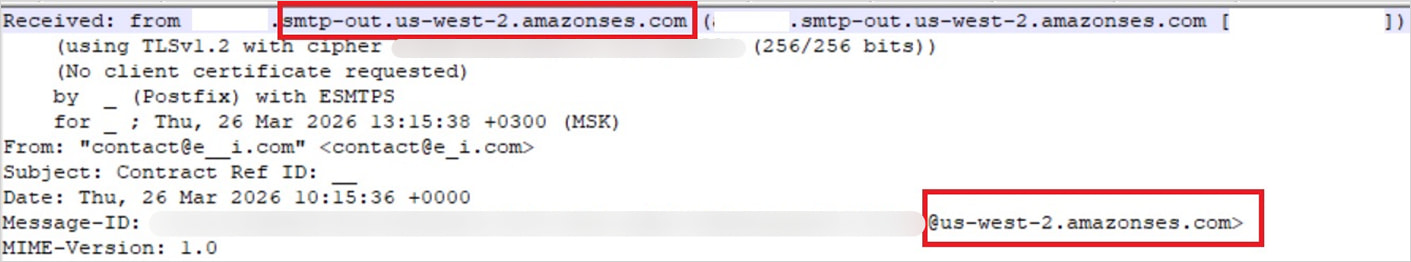
Supply: Kaspersky
The researchers imagine the primary motive force of this abuse is the expanding publicity of AWS credentials in GitHub repositories, .ENV information, Docker pictures, backups, and publicly obtainable S3 buckets.
Discovering the get entry to keys is normally achieved in an automatic method the usage of bots constructed at the open-source TruffleHog software, which is designed to scan for leaked secrets and techniques.
Risk actors now depend on computerized assaults that streamline secret scanning, permission validation, and e mail distribution, enabling exceptional ranges of abuse.
“After verifying the important thing’s permissions and e mail sending limits, attackers are supplied to unfold a large quantity of phishing messages,” Kaspersky explains.
In accordance with their findings, the researchers say that the phishing high quality is top, that includes customized HTML templates that mimic actual services and products and real looking login flows.
The seen assaults come with faux document-signing notifications that imitate DocuSign to steer sufferers to AWS-hosted phishing pages, in addition to extra complicated industry e mail compromise (BEC) assaults.
Attackers fabricate complete e mail threads to make the phishing messages seem extra convincing and ship faux invoices to trick finance departments into making bills.
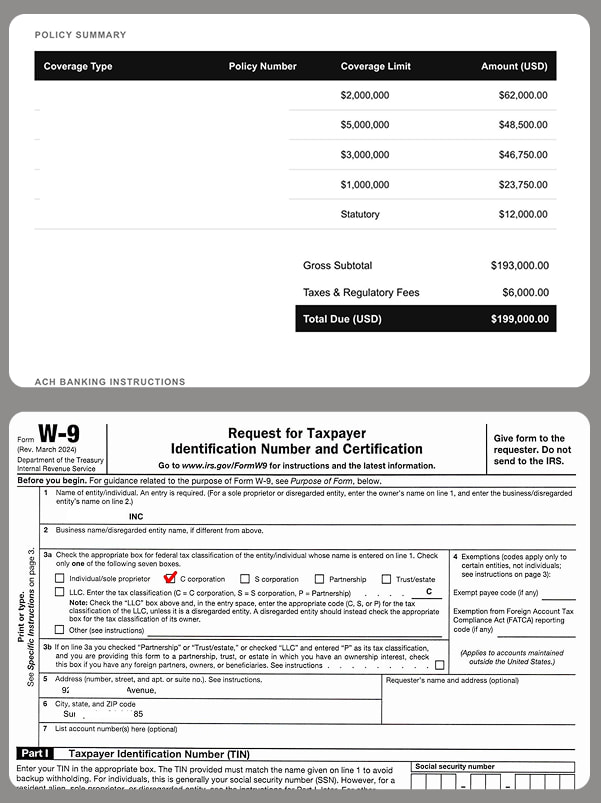
Supply: Kaspersky
Through leveraging Amazon SES, attackers now not want to fear about authentication exams such because the SPF, DKIM, and DMARC protocols.
Moreover, blockading the offending IP addresses that ship the phishing emails isn’t a suitable resolution as a result of it might save you all emails coming thru Amazon SES.
Risk actors are not any that specialize in Amazon SES by myself. They’re repeatedly looking for techniques to abuse different official e mail techniques to push phishing messages.
Kaspersky recommends that businesses limit IAM permissions in line with the “least privilege” ideas, permit multi-factor authentication, ceaselessly rotate keys, and practice IP-based get entry to restrictions and encryption controls.
In a observation for BleepingComputer, Amazon pointed to its safety steering on uncovered credentials and give protection to towards unauthorized get entry to to accounts.
The corporate additionally mentioned that it’s fast to react on experiences of doable phrases of carrier violations and take suitable motion.
“If any individual suspects that AWS assets are getting used for abusive job, they are able to document it to AWS Consider & Protection,” an AWS Spokesperson advised BleepingComputer.
Replace [May 4th, 16:59 EST]: Article up to date with data from an Amazon observation won after publishing time.
Replace [May 5th, 11:50 EST]: Added an replace and corrected the lede to mirror that the abuse build up is in line with Kaspersky telemetry knowledge and isn’t a basic development.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Self sustaining Validation Summit (Would possibly 12 & 14), see how self sufficient, context-rich validation reveals what is exploitable, proves controls cling, and closes the remediation loop.
Declare Your Spot



