Microsoft has showed that the April 2026 safety updates are inflicting disasters in third-party backup packages the usage of the psmounterex.sys motive force.
As BleepinComputer reported ultimate week, this factor impacts device the usage of VSS (Quantity Shadow Replica Carrier) snapshots and reasons disasters because of a VSS carrier timeout.
Instrument impacted by way of this comprises, however isn’t restricted to, merchandise from Macrium (Replicate), Acronis (Cyber Give protection to Cloud), UrBackup Server, and NinjaOne Backup working on Home windows 11, Home windows Server, and Home windows 10 gadgets.
Microsoft has now up to date its toughen paperwork to substantiate that the April updates come with a safety hardening alternate that provides psmounterex.sys to the corporate’s prone motive force blocklist to shield customers in opposition to assaults focused on a high-severity buffer overflow vulnerability (CVE-2023-43896) that permits attackers to escalate privileges or execute arbitrary code.
Microsoft additionally urged the ones suffering from this factor to replace to a more moderen model in their app that makes use of more moderen drivers, which come with the desired protections.
On impacted programs, the place the prone power is blocked by way of Home windows Code Integrity enforcement, IT admins and customers would possibly apply the next habits:
- Backup packages that depend at the kernel motive force psmounterex.sys would possibly fail to mount backup picture information as digital drives.
- Making an attempt to browse or repair from a backup picture would possibly lead to mistakes or timeouts.
- Disasters could be adopted by way of error messages, corresponding to “The backup has failed as a result of Microsoft VSS has timed out right through the snapshot introduction” or VSS_E_BAD_STATE.
- Tournament Viewer would possibly display Code Integrity mistakes indicating that psmounterex.sys was once blocked from loading.
- Backup introduction (complete picture backups) would possibly nonetheless prevail, however image-mount operations will fail.
“Within the April 2026 Home windows safety replace, we added identified prone kernel motive force psmounterex.sys to the Prone Motive force Blocklist. Backup packages that depend on this motive force would possibly revel in disasters when making an attempt to mount or arrange disk pictures,” Microsoft advised BleepingComputer.
“We don’t counsel uninstalling or pausing this replace. Consumers with an impacted motive force must set up the newest utility variations and validate in opposition to the driving force blocklist to stay safe.”
To test whether or not the Microsoft Prone Motive force Blocklist blocks a motive force, affected shoppers can search for ‘Tournament ID 3077’ with Coverage ID {D2BDA982-CCF6-4344-AC5B-0B44427B6816} within the Code Integrity Operational log, which signifies that the psmounterex motive force was once blocked in enforcement mode.
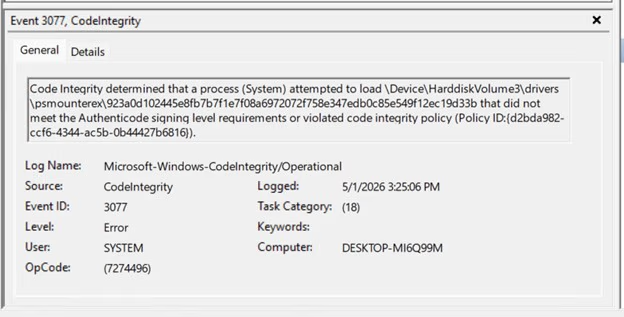
To do this, right-click Get started, make a selection Tournament Viewer, cross to ‘Programs and Services and products LogsMicrosoftWindowsCodeIntegrityOperational’ within the left pane, and search for Tournament ID 3077 within the center pane.
Previous this month, Microsoft warned that some Home windows Server 2025 gadgets might also boot into BitLocker restoration mode, prompting customers to go into the BitLocker key after putting in the KB5082063 replace.
Microsoft additionally launched out-of-band (OOB) updates to mend problems affecting Home windows Server programs that brought about replace set up disasters and restart loops after putting in the April 2026 safety updates.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Self reliant Validation Summit (Might 12 & 14), see how self sustaining, context-rich validation unearths what is exploitable, proves controls cling, and closes the remediation loop.
Declare Your Spot



