
Cybersecurity researchers have exposed a large-scale fraud operation that makes use of Telegram’s Mini App function to run crypto scams, impersonate well known manufacturers, and distribute Android malware.
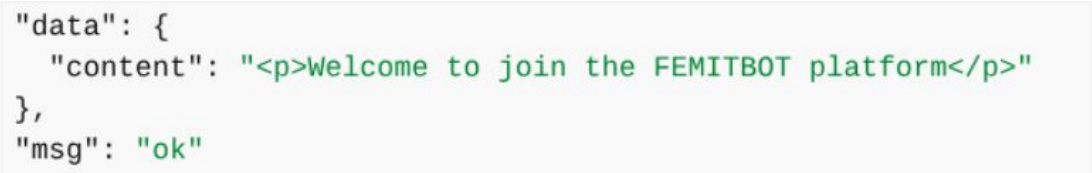
A brand new record via CTM360 says the platform, dubbed FEMITBOT, is in response to a string present in API responses and makes use of Telegram bots and embedded Mini Apps to create convincing, app-like reports at once throughout the messaging platform.
Telegram Mini Apps are light-weight internet programs that run within Telegram’s integrated browser, enabling products and services comparable to bills, account get right of entry to, and interactive gear with out requiring customers to go away the app.
Abusing Telegram mini apps
Consistent with a CTM360 record shared with BleepingComputer, the FEMITBOT platform is used to habits more than one kinds of scams, together with faux cryptocurrency platforms, monetary products and services, AI gear, and streaming websites.
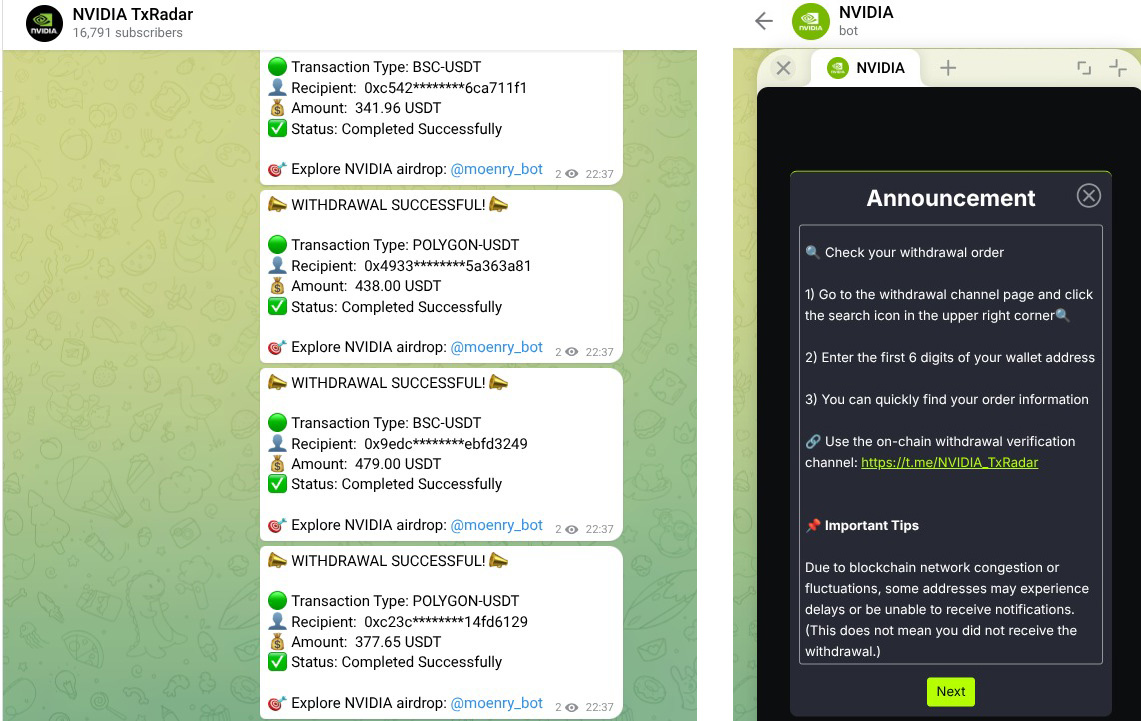
In quite a lot of campaigns, danger actors impersonated well known manufacturers to extend credibility and engagement, whilst the use of the similar backend infrastructure with other domain names and Telegram bots.
Probably the most manufacturers impersonated on this marketing campaign come with Apple, Coca-Cola, Disney, eBay, IBM, Moon Pay, NVIDIA, YouKu,
Supply: CTM360
Researchers say the task makes use of a shared backend, the place more than one phishing domain names use the similar API reaction, “Welcome to enroll in the FEMITBOT platform,” indicating they’re all the use of the similar infrastructure.
Supply: CTM360
The operation makes use of Telegram bots to show phishing websites at once throughout the social media platform. When a consumer interacts with a bot and clicks “Get started,” the bot launches a Mini App that presentations a phishing web page in Telegram’s integrated WebView, making it seem as a part of the app itself.
As soon as within, sufferers are proven dashboards with faux balances or “income,” ceaselessly paired with countdown timers or limited-time provides to create a way of urgency.
When customers try to withdraw price range, they’re brought on to make a deposit or entire referral duties, a not unusual tactic in funding and advance-fee scams.
The researchers say the infrastructure is designed for use throughout other campaigns, permitting attackers to simply transfer branding, languages, and topics.
The campaigns additionally use monitoring scripts, comparable to Meta and TikTok monitoring pixels, to trace customers’ task, measure conversions, and more likely to optimize efficiency.
Some Mini Apps additionally tried to distribute malware within the type of Android APKs that impersonated manufacturers just like the BBC, NVIDIA, CineTV, Coreweave, and Claro.

Supply: CTM360
Customers are brought on to obtain Android APK recordsdata, open hyperlinks throughout the in-app browser, or set up innovative internet apps that mimic respectable device.
“The APK filenames are moderately selected to resemble respectable programs or use random-looking names that do not straight away cause suspicion,” explains CTM360.
“The APKs are hosted at the identical area because the API, making sure TLS certificates validity and heading off mixed-content warnings within the browser.”
Customers must be wary when interacting with Telegram bots that advertise crypto investments or advised them to release Mini Apps, particularly if they’re requested to deposit price range or obtain apps.
As a normal rule, Android customers must steer clear of sideloading APK recordsdata, that are frequently used to distribute malware outdoor the Google Play Retailer.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Independent Validation Summit (Might 12 & 14), see how self sufficient, context-rich validation unearths what is exploitable, proves controls cling, and closes the remediation loop.
Declare Your Spot



