
A brand new phishing equipment named Bluekit gives greater than 40 templates concentrated on fashionable services and products and contains elementary AI options for producing marketing campaign drafts.
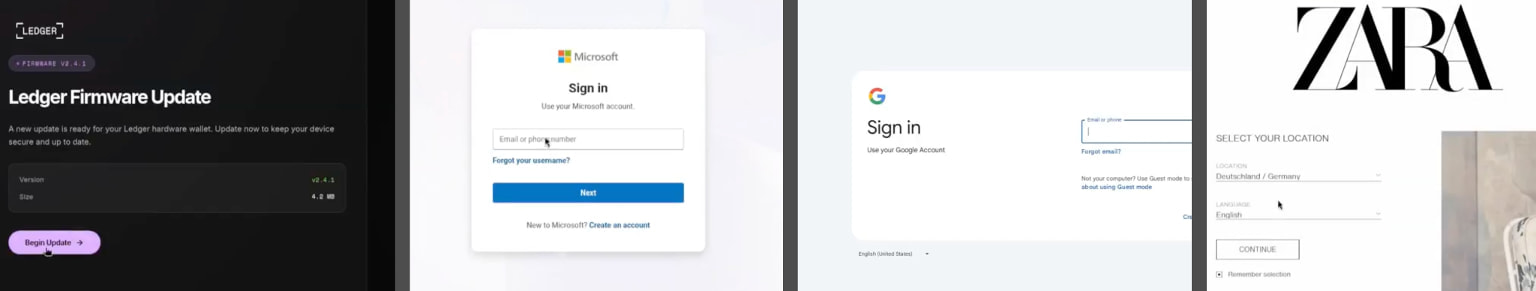
To be had templates can be utilized to focus on electronic mail accounts (Outlook, Hotmail, Gmail, Yahoo, ProtonMail), cloud services and products (iCloud), developer platforms (GitHub), and cryptocurrency services and products (Ledger).
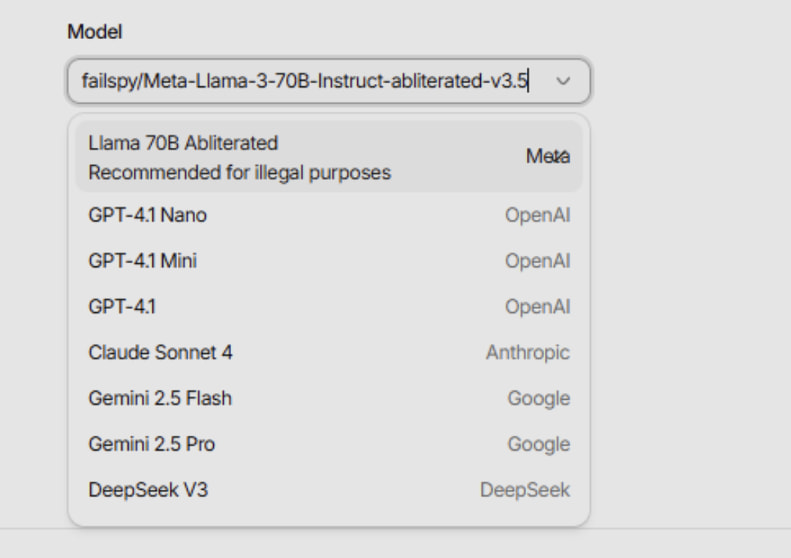
What makes the equipment stand out is the presence of an AI Assistant panel that helps a couple of fashions, together with Llama, GPT-4.1, Claude, Gemini, and DeepSeek, which is helping cybercriminals draft phishing emails.

This reinforces the wider pattern of cybercrime platforms integrating AI to streamline and scale their operations. Extraordinary Safety not too long ago reported about ATHR, a voice phishing platform that leverages AI brokers to behavior social engineering assaults.
Cybersecurity corporate Varonis analyzed a restricted model of Bluekit’s AI Assistant panel and notes that the generated outputs featured placeholder content material, suggesting a characteristic in an early, experimental level.
“The [generated] draft incorporated an invaluable construction, but it surely nonetheless relied on generic hyperlink fields, placeholder QR blocks, and duplicate that would wish cleanup prior to use,” Varonis says.
“Bluekit’s AI Assistant seemed extra like a method to generate a marketing campaign skeleton than a completed phishing glide.”
Supply: Varonis
Except the AI side, BlueKit integrates area acquire/registration, phishing web page setup, and marketing campaign control right into a unmarried panel.
Varonis reviewed templates for iCloud, Apple ID, Gmail, Outlook, Hotmail, Yahoo, ProtonMail, GitHub, Twitter, Zoho, Zara, and Ledger, that includes real looking designs and symbols.
Supply: Varonis
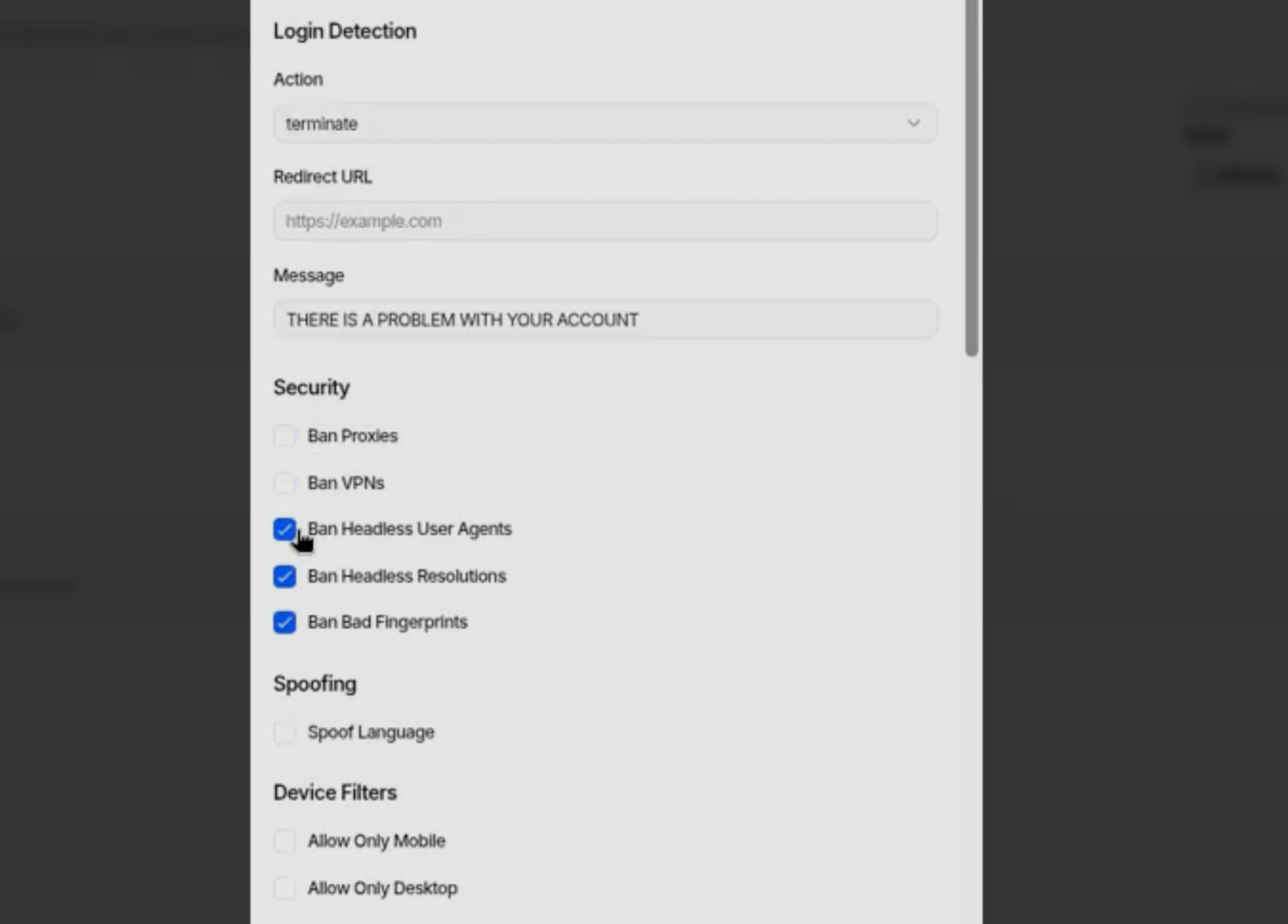
Operators can make a choice domain names, templates, and modes in a unified interface, configure the phishing web page conduct, corresponding to redirects, anti-analysis mechanisms, and login procedure dealing with, and track sufferer periods in real-time.
In line with the choices within the dashboard, customers have granular keep watch over over the conduct of the phishing pages and will block VPN or proxy visitors, headless person brokers, or set fingerprint-based filters.
Supply: Varonis
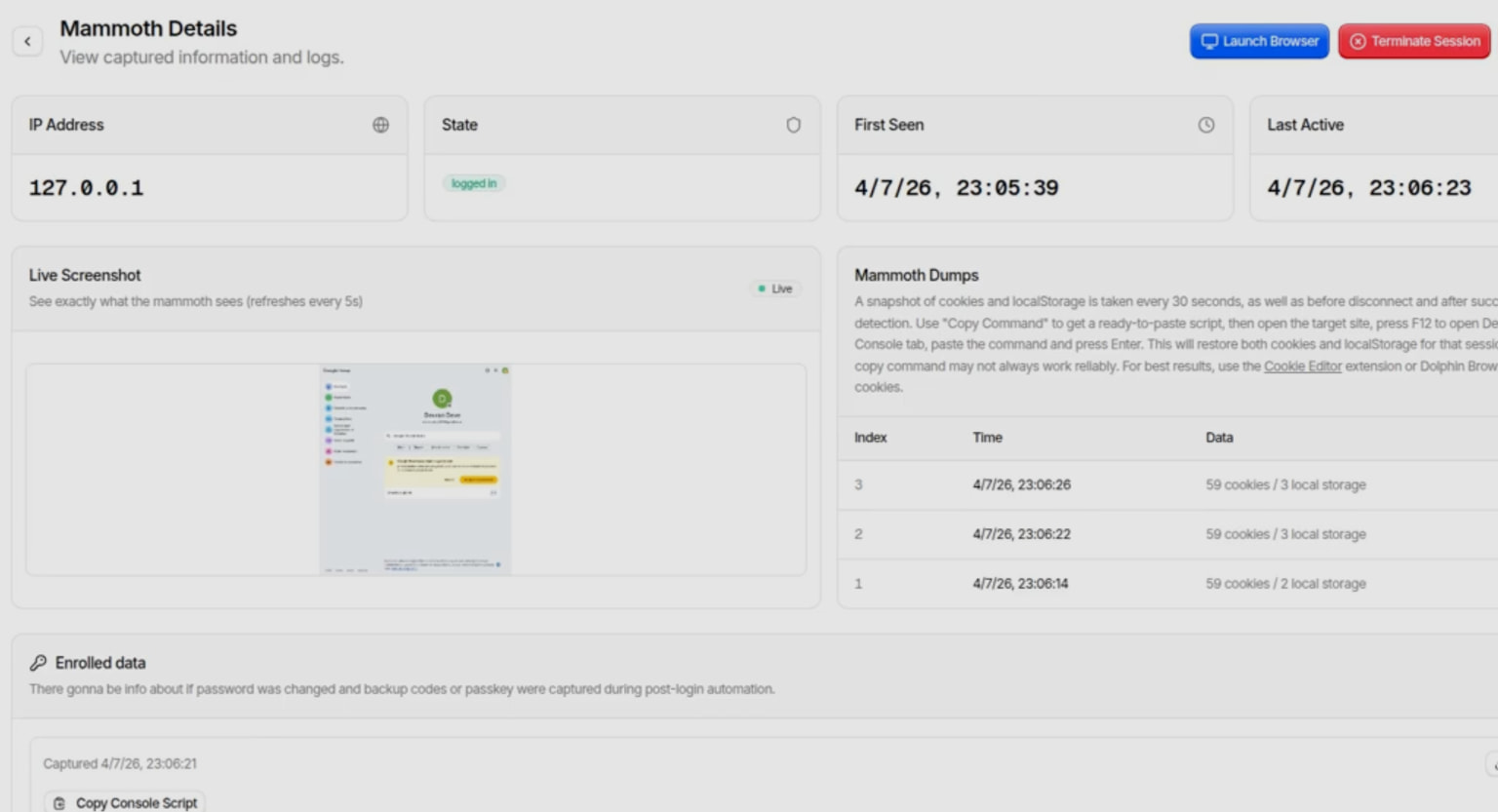
Stolen information is exfiltrated by way of Telegram, on non-public channels available by way of the operators.
The post-capture consultation tracking contains cookies, native garage, and are living consultation state, appearing what the sufferer was once served after login, serving to operators refine their assaults for max effectiveness.
Supply: Varonis
Varonis feedback that Bluekit is but any other instance of an “all-in-one” phishing platform, giving lower-tier cybercriminals totally fledged equipment to regulate all of the phishing assault lifecycle.
.jpg)
Supply: Varonis
Alternatively, the equipment lately seems to be below lively construction, receiving widespread updates and evolving briefly, making it a just right candidate for rising adoption.

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of recent exploits is coming.
On the Self sufficient Validation Summit (Might 12 & 14), see how self sufficient, context-rich validation reveals what is exploitable, proves controls cling, and closes the remediation loop.
Declare Your Spot



