
In early March, GitHub patched a important far off code execution vulnerability (CVE-2026-3854) that may have allowed attackers to get right of entry to tens of millions of personal repositories.
The flaw used to be reported on March 4, 2026, via researchers at cybersecurity company Wiz via GitHub’s computer virus bounty program. GitHub Leader Knowledge Safety Officer Alexis Wales stated the corporate’s safety crew reproduced and showed the vulnerability inside 40 mins and deployed a repair to GitHub.com not up to two hours after receiving the document.
CVE-2026-3854 impacts GitHub.com, GitHub Undertaking Cloud, GitHub Undertaking Cloud with Knowledge Residency, GitHub Undertaking Cloud with Undertaking Controlled Customers, and GitHub Undertaking Server.

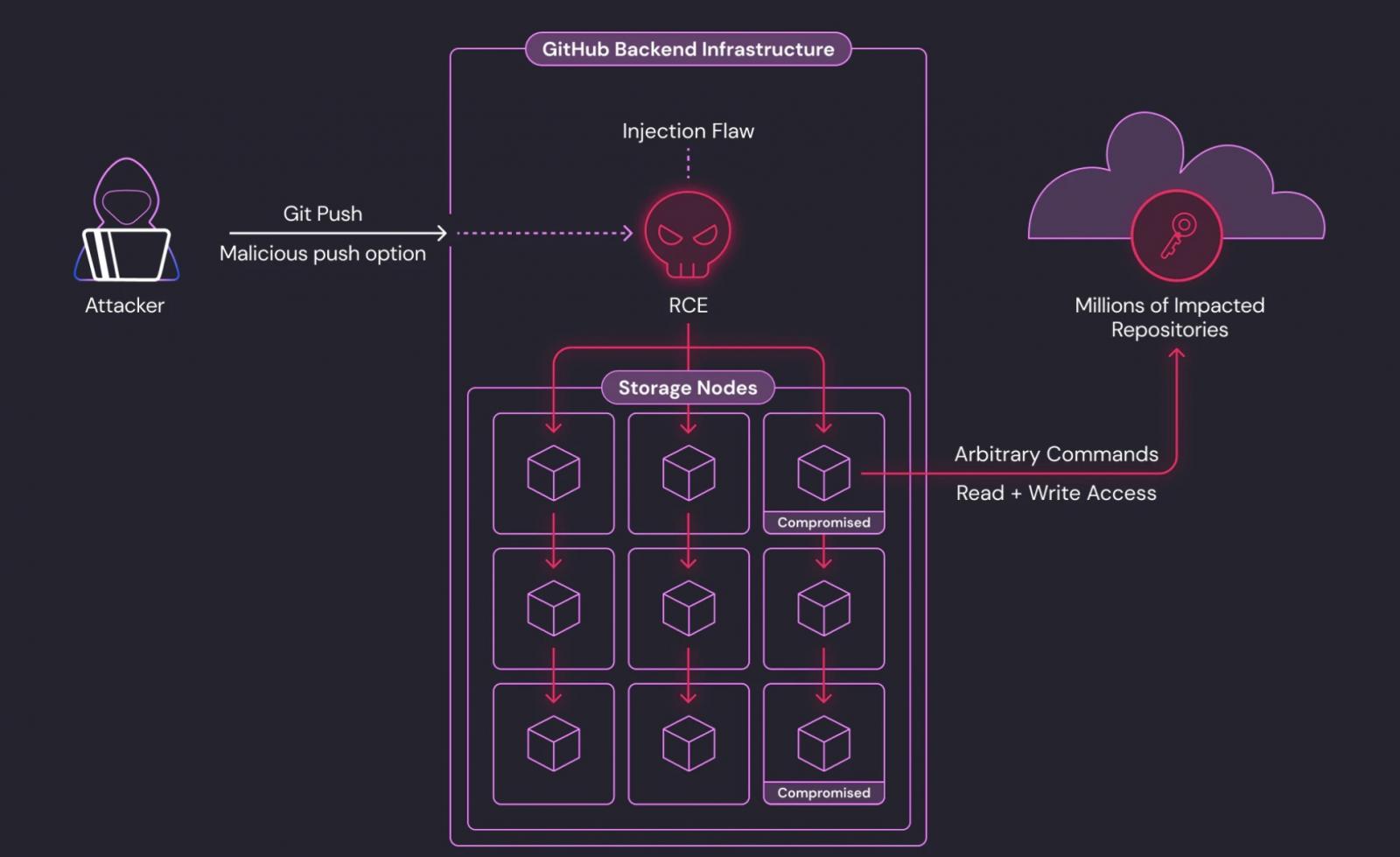
A hit exploitation calls for just a unmarried maliciously crafted ‘git push’ command and will grant complete learn/write get right of entry to to personal repositories on GitHub.com or prone GitHub Undertaking servers to attackers with push get right of entry to.
The vulnerability lies in how GitHub handles user-supplied choices all over git push operations, with values handed via customers being integrated into interior server metadata with out enough sanitization, permitting attackers to inject further fields relied on via the downstream provider.
As Wales defined on Tuesday, an attacker may bypass sandboxing protections and execute arbitrary code at the server dealing with the frenzy via chaining more than one injected values in combination.
”Exploitation may reveal the codebases of just about all the international’s greatest enterprises, making this one of the serious SaaS vulnerabilities ever discovered,” a Wiz spokesperson advised BleepingComputer.
“On GitHub.com, this vulnerability allowed far off code execution on shared garage nodes. We showed that tens of millions of private and non-private repositories belonging to different customers and organizations had been out there at the affected nodes,” Wiz safety researcher Sagi Tzadik added in a Tuesday document.
“On GitHub Undertaking Server, the similar vulnerability grants complete server compromise, together with get right of entry to to all hosted repositories and interior secrets and techniques.”
Tzadik additionally warned that whilst GitHub has patched this primary safety factor on GitHub.com inside 6 hours, GitHub Undertaking Server (GHES) directors will have to improve straight away, as round 88% of reachable GHES cases stay prone.
Alternatively, in spite of the flaw’s severity, a forensic investigation discovered no proof of exploitation prior to the Wiz disclosure, and GitHub stated telemetry information showed that each example of the anomalous code trail caused via the vulnerability used to be attributable only to the Wiz researchers’ checking out.
Wales added that no different customers or accounts caused the code trail used to milk this vulnerability, and that no buyer information used to be accessed, changed, or exfiltrated on account of CVE-2026-3854 exploitation prior to patches had been deployed on GitHub.com.
“For GitHub Undertaking Server, we ready patches throughout all supported releases (3.14.25, 3.15.20, 3.16.16, 3.17.13, 3.18.8, 3.19.4, 3.20.0, or later) and printed CVE-2026-3854,” Wales stated. “Those are to be had these days and we strongly suggest that each one GHES shoppers improve straight away.”

AI chained 4 zero-days into one exploit that bypassed each renderer and OS sandboxes. A wave of latest exploits is coming.
On the Self sustaining Validation Summit (Might 12 & 14), see how independent, context-rich validation reveals what is exploitable, proves controls hang, and closes the remediation loop.
Declare Your Spot



