
When cybercrime operations are disrupted, the reason is usually no longer because of refined detection, however moderately elementary operational errors comparable to identification reuse, vulnerable infrastructure separation, or lost sight of metadata.
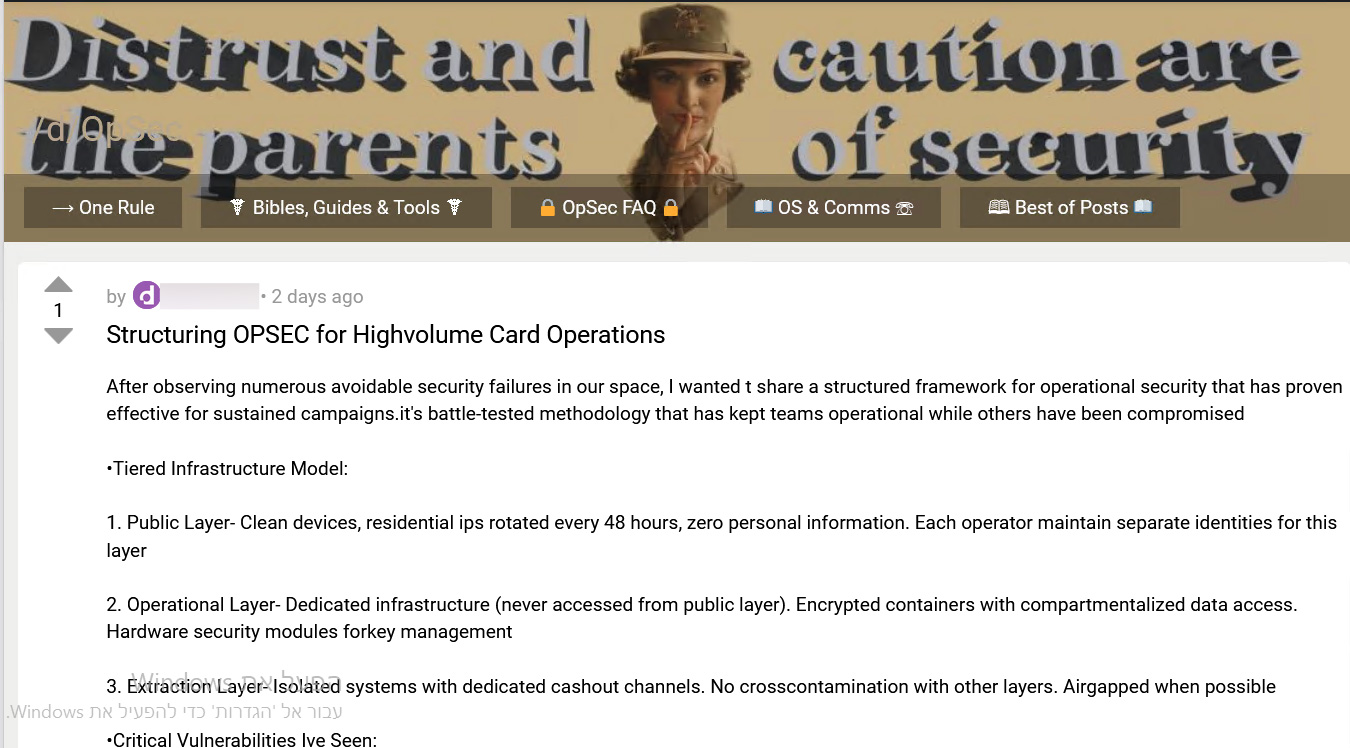
In a up to date cybercrime discussion board publish noticed and analyzed through Flare researchers, a danger actor makes an attempt to deal with those disasters through outlining a structured OPSEC framework designed for “high-volume carding operations.” As an alternative of specializing in gear or monetization, the publish centered totally on the right way to keep undetected over the years.
Consistent with the actor, this framework is a “battle-tested technique that has stored groups operational whilst others were compromised.” The publish reads much less like a discussion board tip and extra like an interior operations guide, whole with a three-tier structure, a taxonomy of commonplace errors, and contingency mechanisms borrowed from the intelligence tradecraft playbook.
Whilst lots of the ways aren’t new, the way in which they’re arranged into a transparent operational framework signifies a extra methodical solution to maintaining large-scale process.
For defenders, this gives an extraordinary glance into how cybercriminals are structuring long-term operational safety.
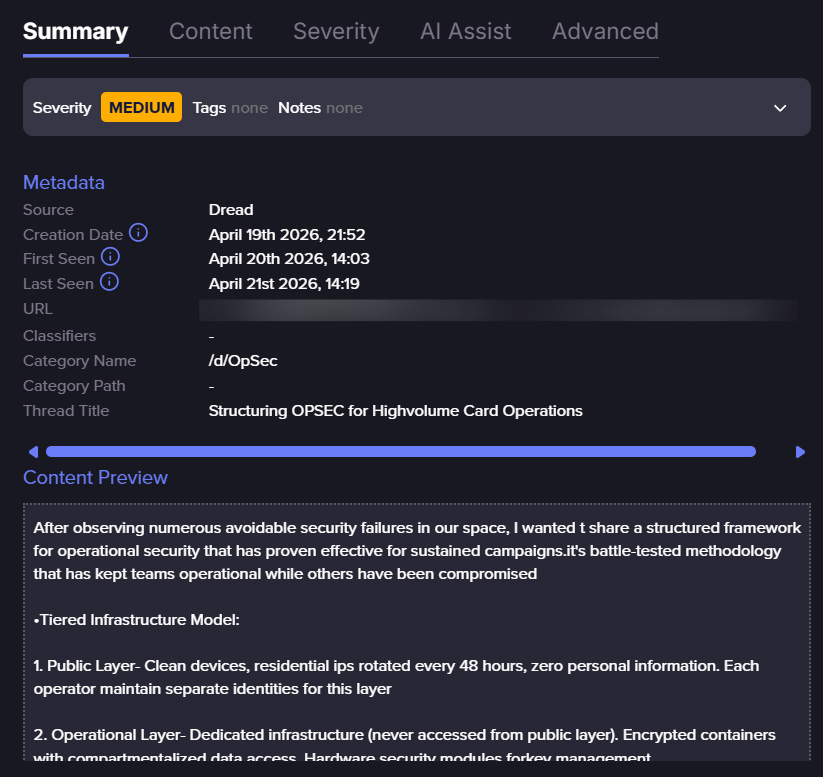
Flare hyperlink to publish, join the unfastened trial to get admission to in the event you aren’t already a buyer
A 3-Tier OPSEC Structure
On the core of the actor’s technique is a three-layer infrastructure style, designed to split publicity, execution, and monetization.
Public Layer
The actor states that the general public layer will have to include “blank gadgets, residential IPs turned around each 48 hours, 0 private data.” Each and every operator may be required to deal with separate identities.
This displays a transparent working out of contemporary detection features. Fraud prevention programs depend on identification correlation and behavioral monitoring, making identification reuse a number one chance.
Using residential IP rotation additionally aligns with real-world fraud campaigns, the place actors more and more depend on proxy networks to mix in with reputable visitors.
Operational Layer
The operational layer is described as utterly remoted from the general public layer, with a strict rule: “by no means accessed from public layer.” Consistent with the actor, this residue will have to come with:
The emphasis here’s on compartmentalization: making sure {that a} compromise in a single a part of the operation does no longer reveal all the infrastructure. This mirrors real-world cybercrime ecosystems. For instance, trendy ransomware teams comparable to LockBit function the usage of affiliate-based fashions, the place other actors maintain get admission to, execution, and monetization one by one to scale back chance publicity.
Structured OPSEC frameworks imply refined danger actors are staying hidden longer.
Flare displays cybercrime boards, darkish internet communities, and Telegram channels—giving your workforce early caution sooner than assaults achieve your surroundings.
Stay alongside of danger actors totally free
Extraction Layer
The overall layer makes a speciality of monetization. The actor specifies that this residue should be “remoted programs with devoted cashout channels” and, when conceivable, “airgapped.” The actor additionally emphasizes “no cross-contamination with different layers”.
This displays a vital working out: monetary transactions are steadily the purpose the place investigations be triumphant. Via separating cashout infrastructure, actors try to damage the forensic chain between fraud process and monetization.
The Errors That Nonetheless Result in Publicity
The actor identifies a number of routine disasters that proceed to reveal cybercriminal operations.
Identification Reuse
The reuse of burner accounts is highlighted as a significant safety chance. Consistent with the danger actor, this is likely one of the maximum commonplace operational disasters. In observe, this aligns with a lot of investigations the place regulation enforcement effectively connected actors via cross-platform identification reuse.
Susceptible Fingerprinting Evasion
The actor criticizes “insufficient virtual fingerprinting countermeasures.” This displays the rising significance of instrument fingerprinting in fraud detection. Trendy programs analyze:
The actor’s dismissive tone towards elementary OPSEC means that VPN-only anonymization is now not thought to be enough even inside of underground communities.
Deficient Separation Between Phases
The danger actor calls out “inadequate separation between acquisition and cashout operations.”
When the similar infrastructure is used throughout more than one levels, defenders can extra simply hint process around the assault chain. Consistent with the actor, strict separation is essential to deal with operational longevity.
Metadata Publicity
The actor additionally highlights “deficient metadata control on operational fabrics.”
This can be a delicate however vital chance. Metadata embedded in recordsdata, comparable to timestamps or instrument identifiers, has been utilized in more than one real-world instances to spot danger actors.
Complex Ways for Resilience
Past elementary hygiene, the actor outlines a number of complicated ways designed to support operational sturdiness.
-
Time-delayed triggers: Consistent with the actor, imposing “time-delayed operational triggers” can scale back correlation between movements and infrastructure. This method is usually noticed in malware campaigns, the place not on time execution complicates forensic timelines and makes it tougher to hyperlink reason and impact.
-
Behavioral randomization: The actor recommends “behavioral trend randomization” to evade detection. This without delay goals behavioral analytics programs, which might be broadly utilized in fraud prevention. Via mimicking reputable consumer process, attackers try to bypass computerized detection mechanisms.
-
Dispensed verification: The point out of “disbursed verification protocols” suggests multi-step validation throughout programs or operators, lowering reliance on unmarried issues of failure.
-
Lifeless guy’s switches: The actor proposes “lifeless guy’s switches for vital information.” Those mechanisms can routinely delete or disable delicate information if sure stipulations are met, indicating a focal point no longer solely on fending off detection but in addition on proscribing harm when issues cross mistaken.
Key TTPs Known from the Actor’s Framework
According to the actor’s conclusions, a number of transparent TTPs emerge:
-
Infrastructure segmentation to restrict blast radius
-
Identification compartmentalization throughout platforms and layers
-
Use of residential proxies and anti-fingerprinting ways to defeat behavioral analytics
-
Strict separation of operational levels, together with get admission to, execution, and monetization
-
Behavioral evasion via randomization of consumer patterns
-
Resilience mechanisms comparable to lifeless guy’s switches and time-delayed triggers
Those ways aren’t theoretical. They align with strategies noticed in different cybercrime operations.
OPSEC as a Aggressive Benefit
One of the vital revealing facets of the object is how the actor frames operational safety. Consistent with the actor, “If you are nonetheless the usage of VPNs as your number one safety measure, you want to degree up.”
The focal point isn’t on the right way to perform fraud, however on the right way to keep operational over the years. The stern separation between layers, enforced compartmentalization, and integrated contingency mechanisms all level to a transparent precedence: fending off disruption.
This implies that OPSEC is now not only a precaution, it’s changing into a aggressive filter out throughout the cybercrime ecosystem. Actors who depend on elementary protections are much more likely to be uncovered early, whilst the ones adopting structured fashions can function longer and at scale.
The framework isn’t introducing new ways, but it surely formalizes them. And as extra actors undertake equivalent approaches, keeping up get admission to might shift from technical capacity to who can keep hidden the longest.
What Defenders Can Do
Despite the fact that the unique publish is geared toward danger actors, it supplies precious defensive insights for safety groups.
-
Put money into working out cross-platform correlation: The emphasis on fending off identification reuse highlights the significance of cross-platform and cross-session correlation. Defenders will have to center of attention on linking process throughout accounts, gadgets, and behavioral patterns.
-
Evolve behavioral detection: The actor’s center of attention on fingerprinting and randomization underscores the will for complicated behavioral analytics moderately than reliance on static signs.
-
Track all the assault chain: The stern separation between levels manner defenders should attach indicators throughout other levels, from preliminary get admission to to monetization.
-
Leverage metadata: Metadata stays an underutilized however robust investigative software. Right kind research can divulge hidden hyperlinks between operations.
-
Get ready for resilient adversaries: Using contingency mechanisms means that attackers are making plans for disruption. Defensive methods should subsequently emphasize resilience and suppleness, no longer simply prevention.
The discussion board publish sheds mild on how some danger actors are prioritizing operational longevity over temporary get admission to. Consistent with the actor, disasters don’t come from loss of gear, however from deficient self-discipline: identification reuse, vulnerable separation, and operational errors.
For defenders, this shifts the problem. As attackers center of attention on longevity, detection should transfer past remoted signs and as a substitute attach conduct, identities, and infrastructure over the years.
Be told extra through signing up for our unfastened trial.
Subsidized and written through Flare.



